Solflare Crypto Wallet Vulnerability - "xpass exploit"
-
Cyclone, this very much annoys me. How could you do this? I found this vulnerability and I had ALREADY reported it.
-
This post is deleted!
-
I independently found the vulnerability while reverse engineering the encryption function, wrote the solflare_pwn toolkit, and reported the vulnerability on Feb 12 to Solflare with a followup email on Feb 15. All of this with timestamps is disclosed on my post above.
This is the 2nd time rickyc2024 has publicly taken credit for my solflare_pwn toolkit and my work on this project. To once again clarify, he has nothing to do with solflare_pwn or me discovering the vulnerability.
@rickyc2024 has been
banned.# EDIT 2025/02/21
I've also banned his dup accounts below since running multiple accounts on the forum is not allowed.General Forum Rules: https://forum.hashpwn.net/post/11
@rickyc2024banned
@rickyig2025banned
@donotbanbanned
@youremailbanned
@jdjwjdiwbanned -
-
@cyclone will you create versions of these for firefox aswell?
-
@cyclone will you create versions of these for firefox aswell?
@dawp9duhn9gom
I can port the toolkit to Firefox if there is enough interest. However, I generally do not write tooling for Firefox due to the very low global usage only being approx 2%, while Chrome based browsers dominate the global usage at over 70%. -
Update: Details of the Solflare “xpass” Exploit
March 13, 2026
Over the past year I have received many requests asking when I would release the full details of the Solflare xpass exploit. Today, I am publishing those details.
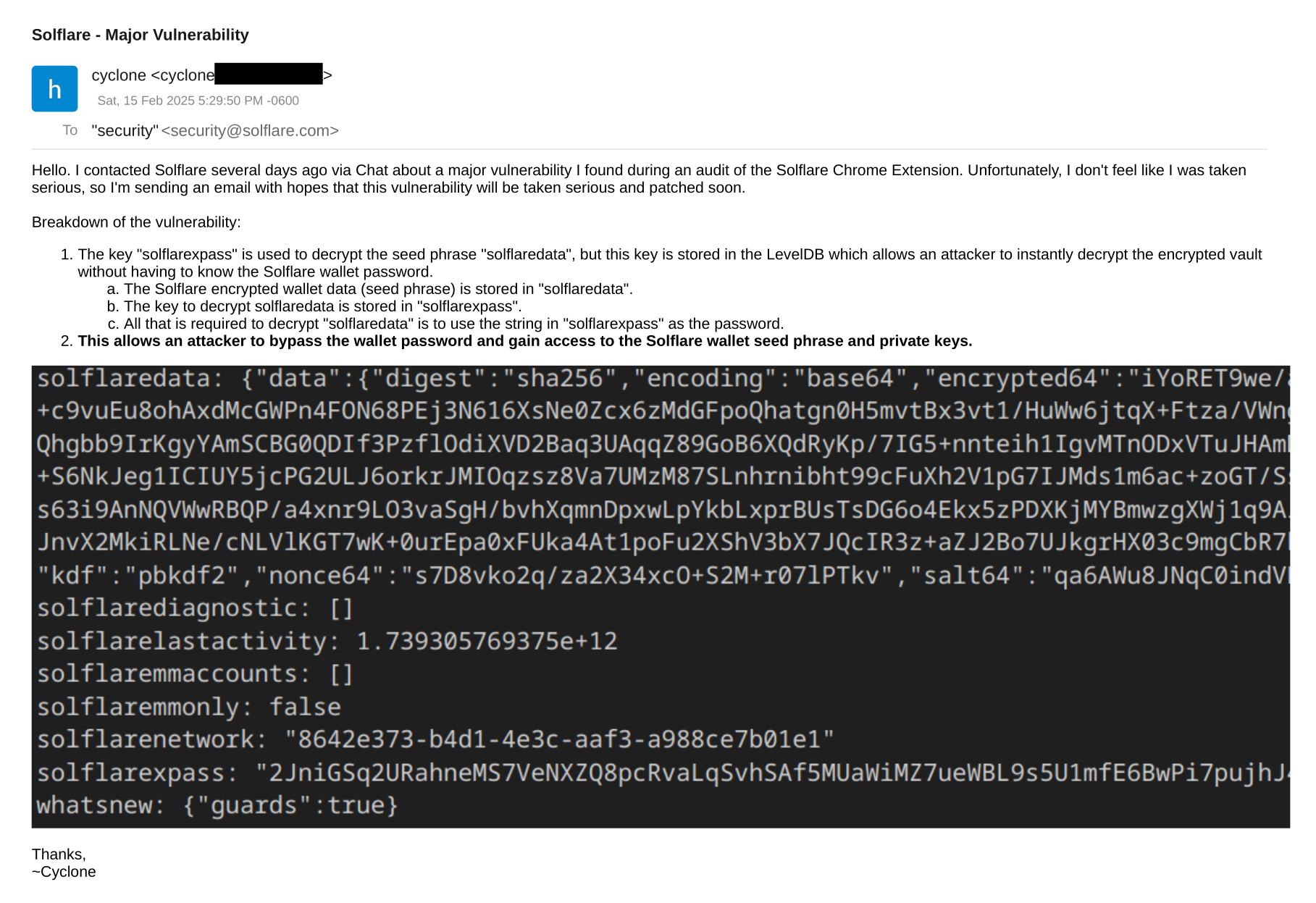
This post serves as an update to my original disclosure in Feb 2025 regarding a purposeful backdoor master key I discovered in the Solflare Chrome wallet extension that allows a wallet vault to be decrypted without requiring the user's wallet password.
At the time of the original report I privately disclosed this to Solflare and delayed public publication to give Solflare time to address the exploit.
The Core Issue
Solflare stores two critical values inside the extension's LevelDB storage:
solflaredata– encrypted wallet vault containing the seed phrase <-- this encrypted string contains the wallet seed phrasesolflarexpass– a key used to decrypt the vault <-- the "backdoor master key"
Because the decryption key is stored locally alongside the encrypted vault, the user's wallet password is not required to decrypt the vault and gain access to the wallet's seed phrase.
All that is required to decrypt the wallet and gain access to the seed phrase is access to the Chrome extension storage and extraction of the solflarexpass key -- something very easy for a malicious actor or stealer malware to do.
Once the vault is extracted with the key, the seed phrase can be recovered. No password cracking required.
Example Storage Layout
Inside the Chrome Solflare extension storage database the relevant entries appear similar to:
solflaredata: { "data":{ "digest":"sha256", "encoding":"base64", "encrypted64":"..." } } solflarexpass: "<stored key>"Using the key stored in
solflarexpass, the encrypted vault (solflaredata) can be decrypted.A screenshot of the original report is attached below.
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login





