-
Hashes.com Escrow Feed
Watching Ignoring Scheduled Pinned Locked Moved Resources1 Votes13k Posts223k Views -
1 Votes121 Posts34k Views
-
Bitlocker Bypass Vulnerability
Watching Ignoring Scheduled Pinned Locked Moved General Discussion 1
0 Votes2 Posts38 Views
1
0 Votes2 Posts38 Views -
Spider - Web Crawler and Wordlist / Ngram Generator
Watching Ignoring Scheduled Pinned Locked Moved Network & IP3 Votes5 Posts2k Views -
hashpwn wordlist
Watching Ignoring Scheduled Pinned Locked Moved Wordlists6 Votes11 Posts4k Views -
Hashmob rules
Watching Ignoring Scheduled Pinned Locked Moved Hashcat Rules hashcat rules hashcat hashmob4 Votes5 Posts821 Views -
37 x WPA handshake
Watching Ignoring Scheduled Pinned Locked Moved Wireless / WPA Cracking0 Votes11 Posts1k Views -
25 Hashes or Less Requests (Database)
Watching Ignoring Scheduled Pinned Locked Moved Database: MySQL, MySQL5, MSSQL, etc.0 Votes6 Posts877 Views -
Concentrator - Unified Hashcat Rule Processor
Watching Ignoring Scheduled Pinned Locked Moved Scripts0 Votes6 Posts736 Views -
rulest - GPU Rules Extractor
Watching Ignoring Scheduled Pinned Locked Moved Scripts0 Votes23 Posts1k Views -
25 Hashes or Less Requests (Standard)
Watching Ignoring Scheduled Pinned Locked Moved Standard: MD5, SHA1, SHA256, etc.1 Votes13 Posts2k Views -
Hashcat Rules
Watching Ignoring Scheduled Pinned Locked Moved Hashcat Rules0 Votes19 Posts4k Views -
Emails rules extractor
Watching Ignoring Scheduled Pinned Locked Moved Scripts0 Votes3 Posts826 Views -
76k SHA256 hash
Watching Ignoring Scheduled Pinned Locked Moved Standard: MD5, SHA1, SHA256, etc.0 Votes3 Posts97 Views -
Hashcat GUI with hashes.com escrow integration
Watching Ignoring Scheduled Pinned Locked Moved HashcatGUI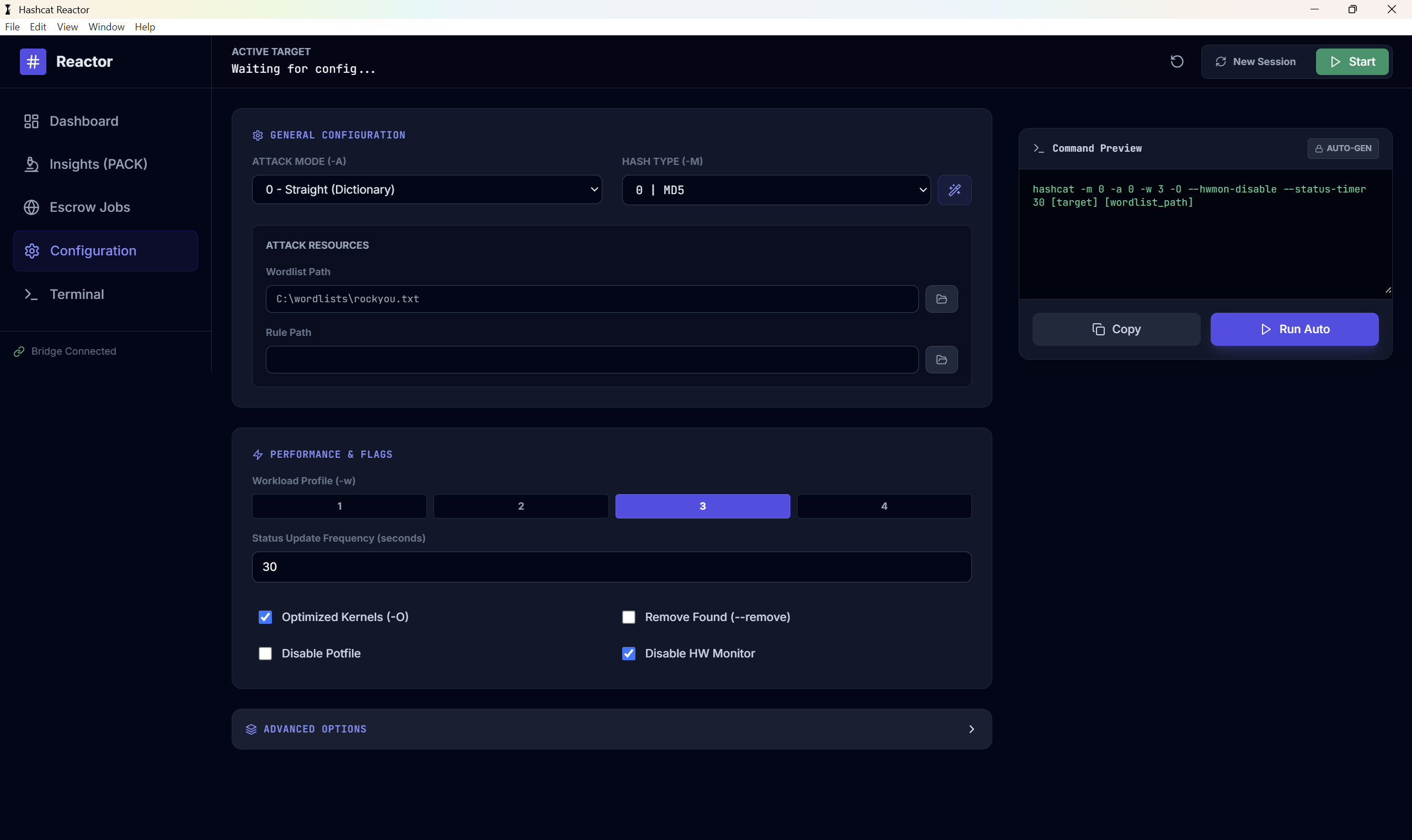 4
0 Votes19 Posts2k Views
4
0 Votes19 Posts2k Views -
Definition of the hashing algorithm.
Watching Ignoring Scheduled Pinned Locked Moved Unknown Algo0 Votes2 Posts841 Views -
hashgen - the blazingly fast hash generator
Watching Ignoring Scheduled Pinned Locked Moved Text / Wordlist / Rules1 Votes12 Posts5k Views -
Cracking metamask hash
Watching Ignoring Scheduled Pinned Locked Moved Crypto Currency: $bitcoin$ $metamask$ $electrum$ $ethereum$ $blockchain$, etc.0 Votes19 Posts2k Views -
Hash cracking rig specs
Watching Ignoring Scheduled Pinned Locked Moved General Discussion0 Votes2 Posts118 Views -
Crack the Con - 2026 (Completed - Team Hashmob Wins!)
Watching Ignoring Scheduled Pinned Locked Moved Contest / CTF0 Votes2 Posts312 Views
Home | Donate | GitHub | Matrix Chat | PrivateBin | Rules

