Infosec News
-
Cloudflare 1.1.1.1 incident on July 14, 2025
On 14 July 2025, Cloudflare made a change to our service topologies that caused an outage for 1.1.1.1 on the edge, resulting in downtime for 62 minutes for customers using the 1.1.1.1 public DNS Resolver as well as intermittent degradation of service for Gateway DNS.Cloudflare's 1.1.1.1 Resolver service became unavailable to the Internet starting at 21:52 UTC and ending at 22:54 UTC. The majority of 1.1.1.1 users globally were affected. For many users, not being able to resolve names using the 1.1.1.1 Resolver meant that basically all Internet services were unavailable. This outage can be observed on Cloudflare Radar.
The outage occurred because of a misconfiguration of legacy systems used to maintain the infrastructure that advertises Cloudflare’s IP addresses to the Internet.
This was a global outage. During the outage, Cloudflare's 1.1.1.1 Resolver was unavailable worldwide.
We’re very sorry for this outage. The root cause was an internal configuration error and not the result of an attack or a BGP hijack. In this blog, we’re going to talk about what the failure was, why it occurred, and what we’re doing to make sure this doesn’t happen again.
Source: https://blog.cloudflare.com/cloudflare-1-1-1-1-incident-on-july-14-2025/
-
Salt Typhoon Hackers Breaches U.S. National Guard
Chinese state-sponsored APT Salt Typhoon pulled off a major breach, infiltrating a U.S. Army National Guard network for 9 months throughout 2024. They quietly exfiltrated network configs, admin creds, and inter-state comms data, potentially laying groundwork for lateral movement across other government networks.
- Exploited vulnerabilities:
- CVE-2018-0171 – Cisco Smart Install RCE
- CVE-2023-20198 + 20273 – Cisco IOS XE chain
- CVE-2024-3400 – PAN-OS GlobalProtect injection
- Stolen data:
- Network diagrams
- Admin credentials
- Interconnected traffic logs with other U.S. states & 4 territories
- PII of service members
Source:
- Exploited vulnerabilities:
-
Global SharePoint Zero-Day Attack Hits Thousands: Microsoft Warns of Ongoing Exploitation
A critical zero-day vulnerability in Microsoft SharePoint Server is being actively exploited by unknown threat actors, prompting urgent alerts from Microsoft, U.S. federal agencies, and international cybersecurity experts. The vulnerability affects only on-premises SharePoint servers. SharePoint Online (cloud) is not impacted.
This is one of the most significant post-SolarWinds-era attacks on enterprise infrastructure. Analysts warn that patching alone may not fully secure already compromised environments. Forensic investigation and credential auditing are essential.
Details:
- Exploit Type: Zero-day vulnerability allowing spoofing and remote exploitation.
- Affected Systems: Only on-prem SharePoint 2016/2019 installations; Microsoft 365 SharePoint Online is unaffected.
- Threat Actor: Likely a single coordinated actor, based on identical payloads and attack patterns across victims.
- Initial Exploits Detected: July 19–20, 2025, rapidly expanding globally.
- Targets: U.S. federal and state agencies, banks, energy companies, telecom, and universities. Over 8,000 vulnerable servers detected online (via Shodan).
Response:
- Microsoft released emergency security updates.
- FBI and CISA are involved in mitigation and investigation.
- Customers are urged to patch immediately or disconnect unpatched servers from the internet.
- Experts recommend an “assume breach” posture and full incident response.
Sources:
-
Starlink Suffers Global Outage on July 24, 2025
On July 24, 2025, at approximately 19:13 UTC, SpaceX’s Starlink network experienced a worldwide outage, resulting in a complete service blackout for thousands of users. By 20:54 UTC, platforms like Downdetector recorded 36k+ incident reports.
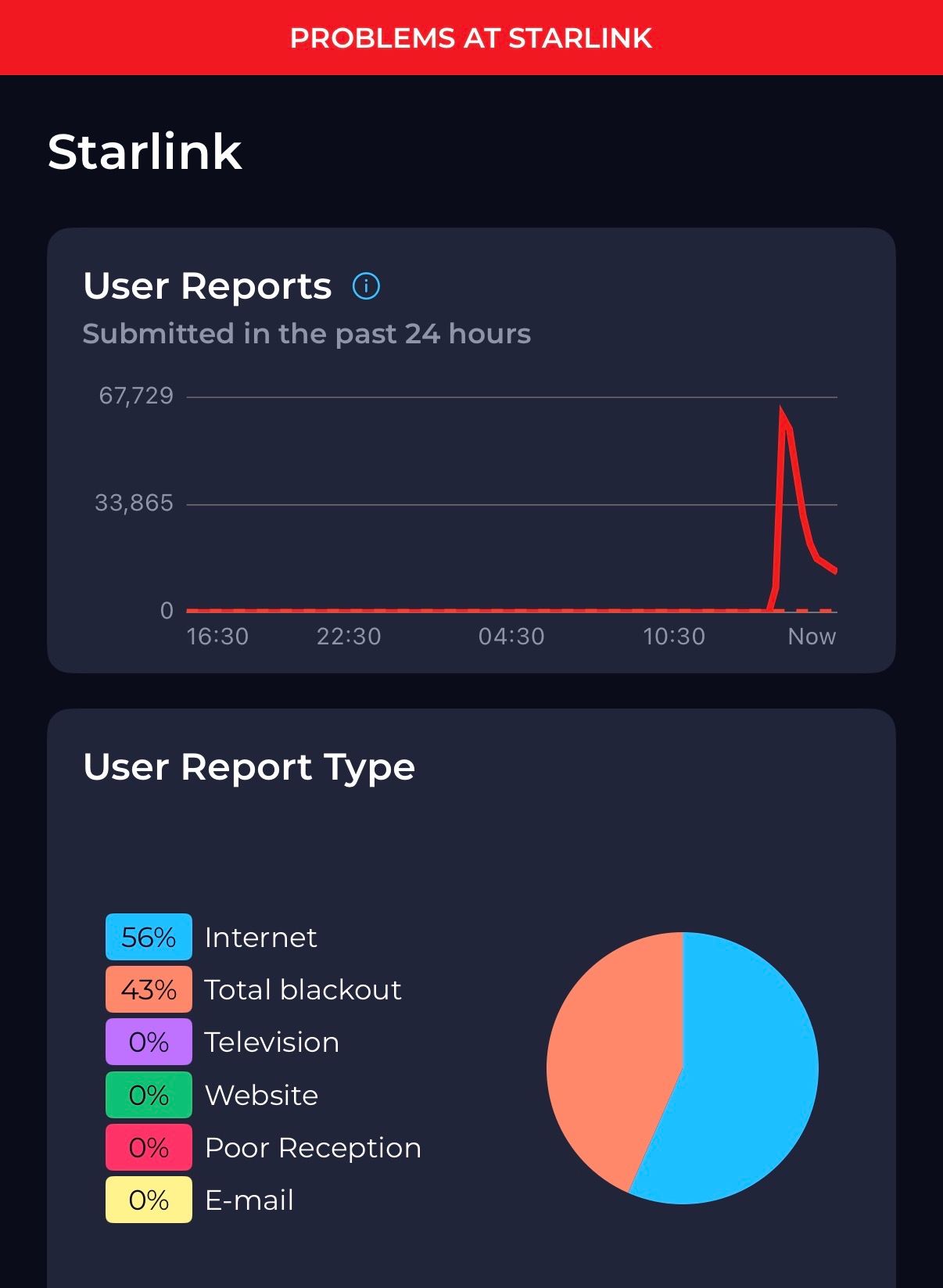
The outage extended across every major region including the US, Europe, Asia, Africa, and Australia, and severely impacted critical users, such as Ukrainian military terminals and T-Mobile’s newly launched satellite messaging service.
Starlink acknowledged the disruption via a website banner and posts on X, stating they were “actively implementing a solution”. CEO Elon Musk apologized, promising to rectify the underlying issue and restore service “shortly”.
Sources:
-
Announced on 8/1/2025 by jsteube:hashcat v7.0.0
Repository: hashcat/hashcat · Tag: v7.0.0 · Commit: 483efe2 · Released by: jsteube
Welcome to hashcat v7.0.0!
We're proud to announce the release of hashcat v7.0.0, the result of over two years of development, hundreds of features and fixes, and a complete refactor of several key components. This version also includes all accumulated changes from the v6.2.x minor releases.
This release is huge. The full write-up is nearly 10 000 words, which exceeds what MyBB supports in a single post.
If you have 30 minutes, here's the write-up (PDF):
https://github.com/hashcat/hashcat/blob/master/docs/release_notes_v7.0.0.pdfQuick summary
- Over 900 000 lines of code changed
- Contributions from 105 developers, including 74 first-time contributors
- Merged and documented all previously unannounced 6.2.x features
This release has 2 assets:
- Source code (zip)
- Source code (tar.gz)
Visit the release page to download them.
-
WinRAR Zero-Day Exploit (CVE-2025-8088)
A critical zero‑day vulnerability, CVE‑2025‑8088, affecting Windows versions of WinRAR (and related tools such as UnRAR.dll and portable UnRAR) has been actively exploited in targeted spear‑phishing attacks by the Russian‑linked threat group RomCom (also known as Storm‑0978, Tropical Scorpius, UNC2596).
A path traversal flaw using alternate data streams (ADSes) allows attackers to embed malicious files in RAR archives, which WinRAR may extract to sensitive system locations such as the Startup folder, enabling automatic code execution on system boot.
Between July 18–21, 2025, spear‑phishing emails carrying booby‑trapped RAR attachments disguised as job applications or CVs were sent to financial, manufacturing, defense, and logistics organizations across Europe and Canada. The payloads included stealth delivery of backdoors such as Mythic Agent, SnipBot, and RustyClaw.
BI.ZONE reports that another group, Paper Werewolf, also exploited this same vulnerability in separate phishing campaigns targeting Russian organizations. Evidence suggests the exploit may have been sold on dark‑web forums for approximately $80,000.
WinRAR acknowledged the vulnerability following ESET’s disclosure on July 24, 2025, releasing a patched version (7.13) by July 30, 2025. Users must manually update, as WinRAR lacks an auto‑update feature.
Sources:
- https://www.tomshardware.com/tech-industry/cyber-security/newly-discovered-winrar-exploit-linked-to-russian-hacking-group-can-plant-backdoor-malware-zero-day-hack-requires-manual-update-to-fix
- https://socradar.io/cve-2025-8088-winrar-zero-day-exploited-targeted/
- https://threatprotect.qualys.com/2025/08/11/winrar-path-traversal-vulnerability-exploited-in-the-wild-cve-2025-8088/
-
OpenAI GPT-5 - Mixed User Reception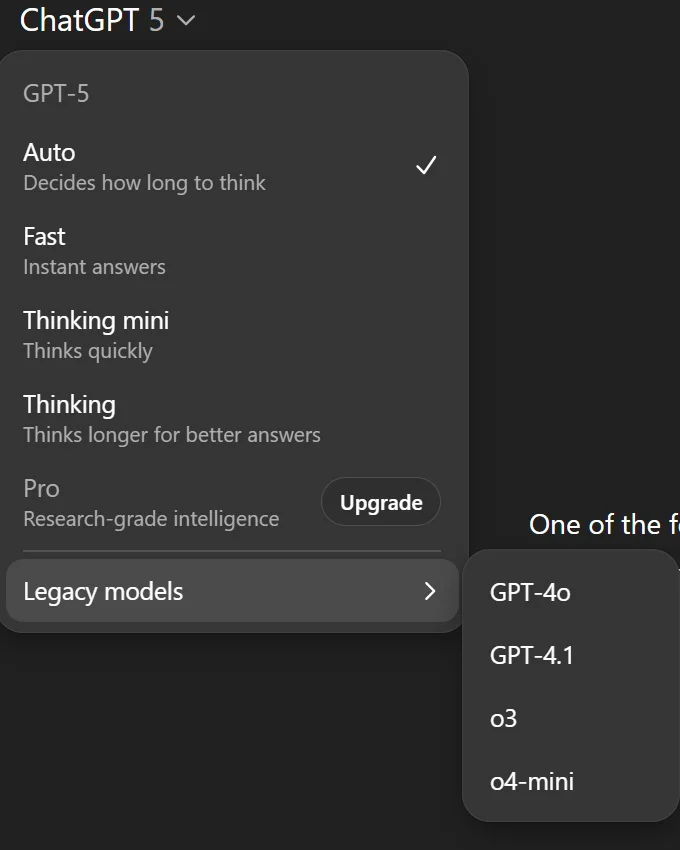
GPT-5 is now the default in ChatGPT with selectable “thinking” modes and an auto-router. After user backlash, OpenAI restored legacy 4 models behind a toggle and promised better deprecation hygiene. “Thinking” usage now has a 3,000 per week cap for paid Plus users.
Early writeups and reporting show jailbreakability remains (narrative/multi-turn attacks still work).
Backlash on removals/personality: Users complained about 4o being pulled and GPT-5 feeling “colder.” OpenAI rolled 4o back (opt-in) and pledged advance notice before removing models next time; personality tweaks inbound.
Media/dev takes: Coverage spans “smarter coding/agents, messier lineup.” BleepingComputer called the new menu “a mess (again)” after OpenAI added options while saying GPT-5 would simplify things.
OpenAI’s claims: Fewer hallucinations, better instruction-following, less sycophancy; strongest coding model to date.
Sources:
- https://help.openai.com/en/articles/11909943-gpt-5-in-chatgpt
- https://www.bleepingcomputer.com/news/artificial-intelligence/openai-adds-new-gpt-5-models-restores-o3-o4-mini-and-its-a-mess-all-over-again/
- https://www.thestack.technology/chatgpt-capacity-tradeoffs-gpt5-bumpy-rollout/
- https://thehackernews.com/2025/08/researchers-uncover-gpt-5-jailbreak-and.html
-
Storm0501 Ransomware Gang Wipes Data and Backups in Azure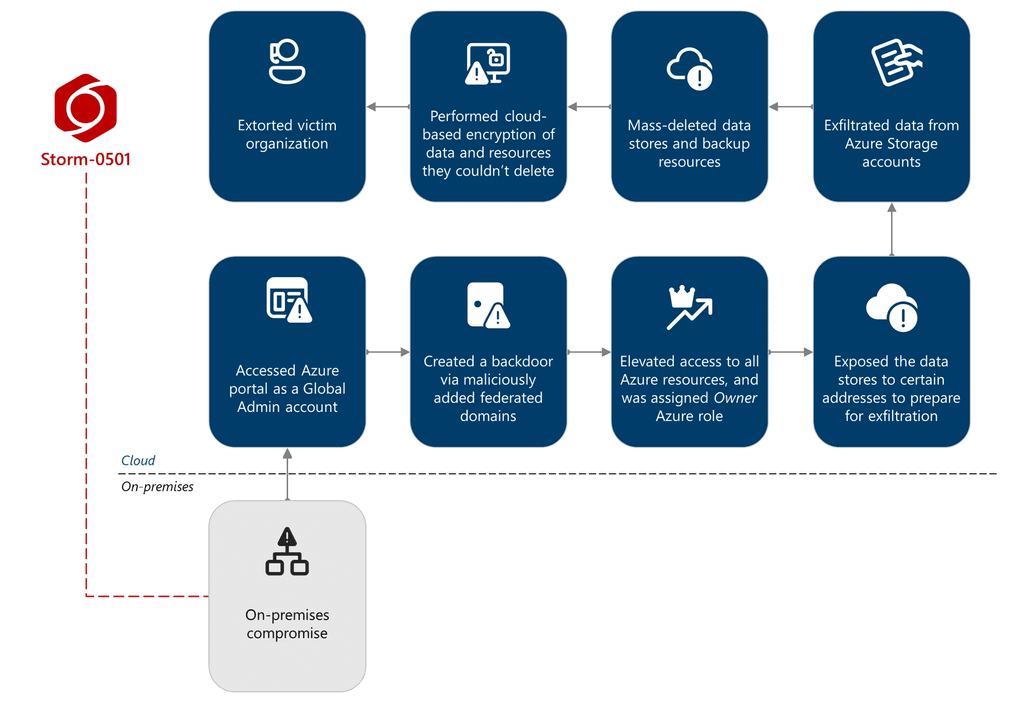
A financially motivated threat group known as Storm0501 has executed one of the most destructive cloud ransomware attacks seen to date. According to Microsoft Threat Intelligence, the group infiltrated a large enterprise operating multiple subsidiaries and successfully pivoted from on premises systems into Microsoft Azure.
Once inside, Storm0501 exfiltrated large volumes of data using the AzCopy CLI tool before deleting backups and encrypting what remained. The attackers exploited weaknesses in Microsoft Entra ID by compromising synchronization servers and abusing a non human global administrator account that lacked multifactor authentication. With full global admin access, the group granted itself ownership of Azure subscriptions, stole storage account keys, and ultimately wiped or encrypted critical resources.
This tactic prevented the victim from restoring operations, forcing them into a difficult recovery scenario. The incident shows how ransomware actors are evolving beyond traditional malware and now weaponizing cloud features to maximize damage.
Microsoft has warned that other threat groups are likely to adopt these same methods and recommends several defensive measures. Organizations should enforce least privilege across Azure environments, enable blob and VM backups, log activity in Key Vault, and harden hybrid cloud attack paths.
Storm0501 has previously targeted schools and healthcare organizations, and with this latest pivot to cloud only operations the group has raised the stakes for enterprises everywhere.
Sources:
-
RAID Failure Causes Matrix.org Outage - Sep 2–3, 2025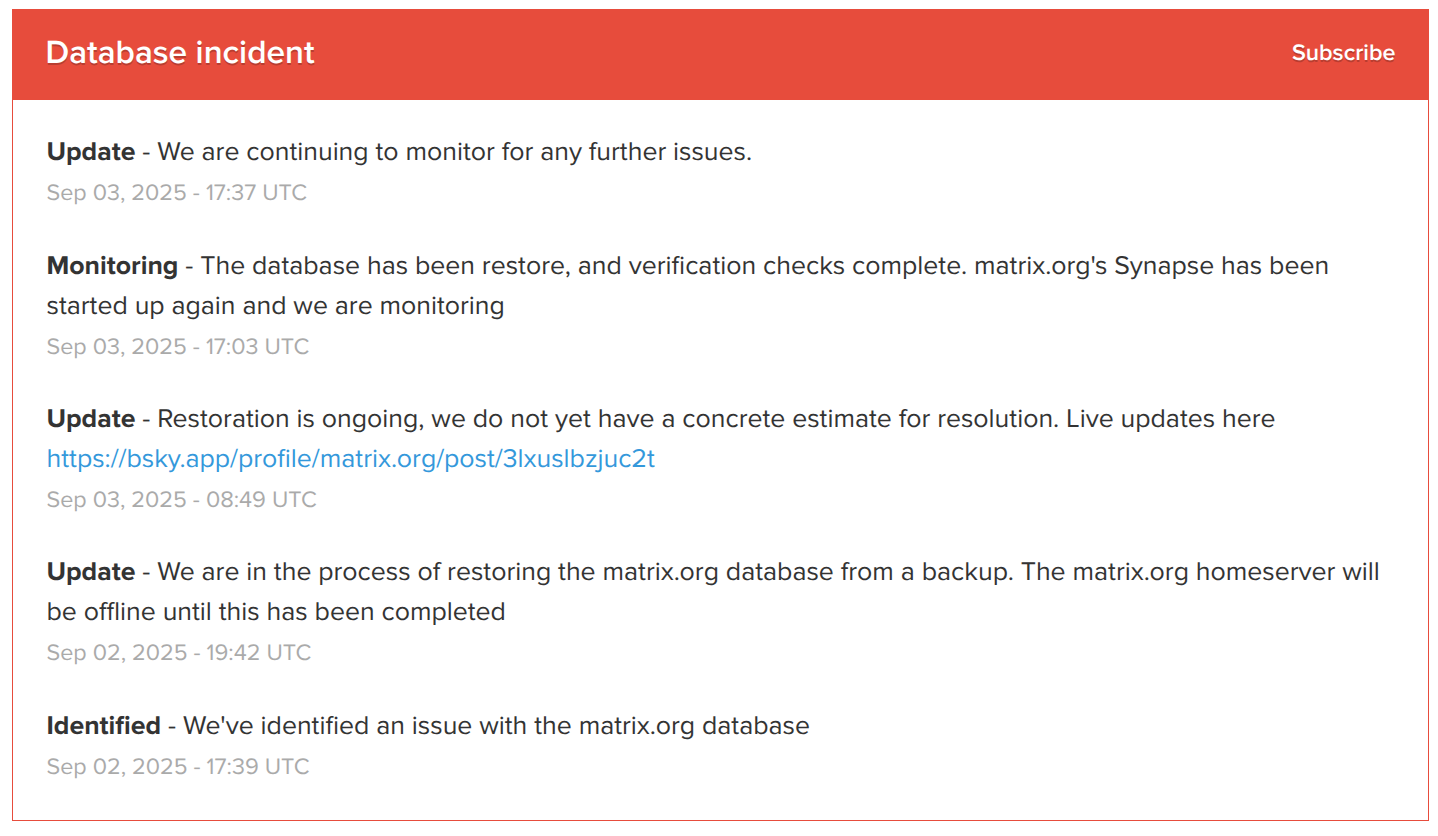
What happened: On Sep 2, a RAID failure took out Matrix.org’s DB secondary (11:17 UTC), and later the primary failed (17:26 UTC). Engineers abandoned an unsafe filesystem recovery and instead restored a full 55 TB PostgreSQL snapshot from the previous night, rebuilt the DB, and replayed queued traffic. The homeserver came back online around 17:00 UTC on Sep 3 and was then monitored as it caught up.
Who was affected: Users on the matrix.org homeserver (e.g.,
@user:matrix.org) lost service during the restore/catch-up window. Folks running their own homeservers were not impacted.
Timeline (UTC):
- Sep 2, 11:17 — DB secondary lost its filesystem due to a RAID failure.
- Sep 2, 17:26 — DB primary failed.
- Sep 2, 17:39 — Incident acknowledged on the status page (“identified an issue with the matrix.org database”).
- Sep 2, 19:02 — Public post confirms RAID failure + plan (point-in-time restore).
- Sep 2, 19:42 — Begin restoring from backup; matrix.org homeserver kept offline.
- Sep 2, 21:41 — “Bad news”: switching to full 55 TB snapshot restore.
- Sep 3, 07:13 — Progress: 47 TB/55 TB restored; still need DB rebuild + ~17 h traffic replay.
- Sep 3, 08:49 — Status page: restoration ongoing; live-updates link shared.
- Sep 3, 10:56 — “Snapshot + incrementals restored; about to replay remaining traffic” (ETA 3–4 h if all goes well).
- Sep 3, 17:00 — matrix.org back online (reported).
- Sep 3, 17:03 — Status: “Database restored; verification complete; Synapse started” — monitoring.
- Sep 3, 17:37 — Continued monitoring.
Sources:
- Incident history timestamps: https://status.matrix.org/incidents/mm9hdm78svgv
- Matrix.org Mastodon updates (Sep 2–3, 2025):
- Live update link shared by Matrix.org: https://bsky.app/profile/matrix.org/post/3lxuslbzjuc2t
-
Plex Breached... Again - Reset Your Passwords Now
Plex breached again, change your password and sign out everywhere.
Plex says an attacker got into one of its databases and pulled a limited set of user data, email, username, hashed passwords, authentication data. No payment info was stored. Plex is telling all users to reset their password, tick “Sign out connected devices” during the reset, then re-enable 2FA. If you use SSO, sign out of all devices from your account security page. Expect phishing around this, Plex won’t ask for your password or card details by email.
This mirrors the 2022 incident, so treat it seriously.
Sources:
-
WhatsApp Zero-Click Hack - CVE-2025-55177
A recently patched zero-click exploit in WhatsApp (CVE-2025-55177), combined with an Apple OS flaw (CVE-2025-43300), allowed attackers to silently install spyware on iOS and Mac devices. The campaign ran for 90 days and targeted fewer than 200 people worldwide, mainly activists and journalists. Victims’ messages, photos, locations, and device data could be exposed without any user action. While mass users were not affected, the flaw remained dangerous until fixed.
Sources:
-
Plot to Cripple NYC Cell Networks Foiled by U.S. Secret Service
The U.S. Secret Service uncovered a massive underground telecom operation just days before the UN General Assembly in Manhattan. Agents seized more than 300 SIM servers and over 100,000 SIM cards hidden across multiple sites within 35 miles of the UN headquarters.
According to officials, the devices had the ability to launch devastating telecom attacks, from spamming up to 30 million texts per minute to jamming 911 lines and disabling cell towers. Investigators say such an attack could have paralyzed New York’s communications network, echoing the cellular outages that followed 9/11.
Authorities are probing possible foreign government links. The timing and sophistication raised concerns about espionage, with experts suggesting state-level actors like Russia or China could be behind it. The Secret Service launched the investigation earlier this year after telecom threats were made against senior U.S. officials.
Rows of servers and shelves stacked with SIM cards were discovered, many already activated. Officials warn the system could have been used for encrypted communication between organized crime, cartels, or even terrorist groups. Forensics teams now face the daunting task of analyzing 100,000 devices to trace connections.
Sources:
-
Akira Ransomware Bypassing MFA on SonicWall VPNs
Akira ransomware operators are still hitting SonicWall SSL VPNs, even when OTP-based MFA is enabled.
Key points:
- Root cause linked to CVE-2024-40766, an access control flaw exploited in 2024.
- Attackers appear to have stolen both credentials and OTP seeds during earlier breaches.
- MFA bypass observed: multiple OTP prompts issued, then successful logins.
- Once inside, actors quickly scan networks, enumerate AD, and target Veeam servers for stored creds.
- BYOVD attacks used to kill endpoint protection via vulnerable drivers like rwdrv.sys.
- Even patched SonicOS 7.3.0 devices are being impacted.
Mitigation:
- Reset all VPN credentials, rotate MFA seeds, and monitor login patterns for anomalies. Backup servers should be treated as high-risk targets.
- MFA cannot protect against stolen seeds. If your SonicWall appliance ever ran vulnerable firmware, reset everything.
Sources:
-
Gen Z Failing at Identifying Phishing Attacks
A new global survey from Yubico reveals that Gen Z, those born between 1997–2012, is the most vulnerable group to phishing attacks, with 62% admitting to engaging with a phishing message in the past year, and are most likely to click on phishing links, attachments, or scams, with AI-powered social engineering attacks driving a new wave of deepfakes and voice-clone phishing.
The 2025 Global State of Authentication Survey, covering 18,000 participants across nine countries, found that:
- 44% of all respondents interacted with a phishing attempt in the past year.
- 70% believe AI has made phishing more effective, and 78% say attacks have grown more sophisticated.
- 54% of people shown a phishing email believed it was genuine or were unsure, highlighting the rising danger of AI-crafted scams.
- Only 48% of companies enforce MFA, and 40% of workers report no cybersecurity training at all.
Sources:
-
Scattered Lapsus$ Hunters Demand Neary $1 Billion in Ransom
A newly revived threat group calling itself Scattered Lapsus$ Hunters, a collaboration between members of Scattered Spider, Lapsus$, and ShinyHunters, has claimed responsibility for stealing over 1 billion Salesforce-related records and is demanding nearly $1 billion in ransom to prevent public release.
According to news reports, the attackers exploited Salesloft’s Drift integration, using stolen OAuth and refresh tokens to access Salesforce APIs and extract customer data, including contact information and case objects. Salesforce itself was not directly breached.
The group has launched a public extortion site listing roughly 40 affected organizations, including major names like Cloudflare, Palo Alto Networks, Zscaler, and Tenable. Victims are urged to “negotiate” to prevent leaks.
Salesforce maintains that its core platform remains secure, stating:
“There is no indication that the Salesforce platform has been compromised, nor is this activity related to any known vulnerability in our technology.”
Security researchers note that the campaign resembles previous Lapsus$ and Scattered Spider operations, focusing on third-party integrations to bypass enterprise protections. Google TAG and Mandiant are investigating the breach’s scope and potential secondary access vectors.
Sources:
-
Harvard Probes Data Breach Tied to Oracle Zero-Day Exploit
Harvard University is investigating a potential data breach after the Clop ransomware gang claimed to have stolen data by exploiting a zero-day flaw in Oracle’s E-Business Suite (CVE-2025-61882).
The university confirmed it was affected by the vulnerability, which has impacted multiple Oracle customers, but said the incident appears limited to a small administrative unit. Harvard stated it applied Oracle’s emergency patch and found no evidence of compromise in other systems.
The Clop group, known for high-profile zero-day exploits in platforms such as MOVEit Transfer and GoAnywhere MFT, recently began targeting Oracle users in a new extortion campaign. Harvard is the first organization publicly linked to the attacks, though more victims are expected to surface in the coming weeks.
Sources
- https://www.bleepingcomputer.com/news/security/harvard-investigating-breach-linked-to-oracle-zero-day-exploit/
- https://www.oracle.com/security-alerts/alert-cve-2025-61882.html
- https://www.crowdstrike.com/en-us/blog/crowdstrike-identifies-campaign-targeting-oracle-e-business-suite-zero-day-CVE-2025-61882/
-
Nation-State Hackers Breach F5 Networks
Summary
F5 Networks has confirmed a major security breach in which a nation-state-linked actor gained unauthorized access to internal systems and exfiltrated portions of BIG-IP source code and information on undisclosed vulnerabilities.
The intrusion is believed to have persisted for roughly 12 months before discovery.The company detected the incident on August 9, 2025, and delayed public disclosure at the request of the U.S. Department of Justice.
There is no indication that CRM, financial, support, or iHealth systems were accessed, although some customer configuration files were included in the stolen data.Technical and Attribution Details
- The attack is attributed to a Chinese cyber-espionage group tracked as UNC5221.
- The group deployed a custom backdoor named BRICKSTORM, previously used in intrusions against SaaS and BPO providers.
- The compromise targeted F5’s development environment, giving access to internal vulnerability data and code repositories.
- F5 brought in Mandiant and CrowdStrike for incident response, rotated all signing keys and credentials, and added additional security controls.
Government Response
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued Emergency Directive 26-01, requiring all federal agencies to:- Inventory all F5 BIG-IP, F5OS, BIG-IQ, and APM systems.
- Verify that management interfaces are not exposed to the internet.
- Apply vendor patches no later than October 22, 2025.
- Submit compliance reports to CISA by October 29, 2025.
CISA stated that the stolen source code and vulnerability information provide adversaries with a technical advantage for developing zero-day exploits.
CVEs and Patch References
Key vulnerabilities disclosed following the breach include:- CVE-2025-53868 – BIG-IP SCP/SFTP privilege escalation (CVSS 8.7)
- CVE-2025-61955 – F5OS command injection, appliance mode (CVSS 8.8)
- CVE-2025-57780 – F5OS arbitrary code execution, appliance mode (CVSS 8.8)
Administrators should immediately apply the latest firmware and software updates for BIG-IP, F5OS, BIG-IQ, APM, and BIG-IP Next (Kubernetes).
Recommended Actions:
- Patch all F5 systems immediately.
- Remove or restrict public access to management interfaces.
- Audit and retire end-of-life or unsupported devices.
- Monitor for anomalous configuration changes or new admin accounts.
- Treat F5 perimeter devices as high-risk until verified patched and hardened.
Sources:
- https://thehackernews.com/2025/10/f5-breach-exposes-big-ip-source-code.html
- https://www.reuters.com/technology/breach-us-based-cybersecurity-provider-f5-blamed-china-bloomberg-news-reports-2025-10-16/
- https://www.techradar.com/pro/security/significant-threat-to-us-networks-after-hackers-stole-f5-source-code-cisa-warns
-
Major Amazon Web Services (AWS) Outage
AWS is currently experiencing a major outage in the US-EAST-1 region, impacting dozens of core services and many third-party platforms.
Status: Degraded performance and elevated error rates across multiple services.
Root Cause (according to AWS): Internal subsystem failure tied to the monitoring of network load balancers and EC2 internal networking.Origin & propagation: Issues began around 3:11 a.m. ET in US-EAST-1, and have cascaded globally for services dependent on that region.
Affected AWS Services (partial list):
Core compute/storage/database services including EC2, S3, RDS, Lambda, CloudWatch, CloudFront, DynamoDB, SQS, SNS, ECS, EKS, Glue, Redshift, SageMaker, Cognito, Connect, VPC services, Step Functions, Secrets Manager, and more.
AWS lists around 90 services impacted.Third-Party Services / Platforms Impacted:
Major consumer/enterprise platforms reported disruptions: games like Fortnite, Roblox; apps like Snapchat, Venmo; smart home devices (Ring, Alexa); banks and financial apps; many SaaS services relying on AWS infrastructure.What this means for you:
- If you rely on AWS in US-EAST-1, expect slower API responses, partial failures, or launch errors (especially for new EC2 instances).
- If you rely on third-party services (SaaS, gaming, streaming, banking), you may see outages despite those services not being your direct provider.
Sources:
- AWS Status Page: https://health.aws.amazon.com/health/status
- Downdetector Report: https://downdetector.com/status/aws-amazon-web-services/
- Tom's Guide: https://www.tomsguide.com/news/live/amazon-outage-october-2025
- Reuters: https://www.reuters.com/business/retail-consumer/amazons-cloud-unit-reports-outage-several-websites-down-2025-10-20/
-
Xubuntu.org Compromised - Torrent Downloads Served Windows Malware
Over the weekend (October 18–19, 2025), the official Xubuntu website (xubuntu.org) was compromised. Attackers managed to inject a malicious download link into the torrent section of the downloads page. A similar attack also happened in September 2025 where attackers injected malicious javascript into non-English language pages of the site.
What Happened
The legitimate .torrent link was replaced with a ZIP archive:
xubuntu-safe-download.zipWhich contained files:
TestCompany.SafeDownloader.exe terms-of-service.txtThe EXE impersonated a “Xubuntu - Safe Downloader” GUI installer.
On execution, it installed itself to:%AppData%\Roamingand added a Windows registry key for persistence at startup.
Malware Behavior
The EXE was identified as a Crypto Clipper Trojan, flagged by 26/72 vendors on VirusTotal.
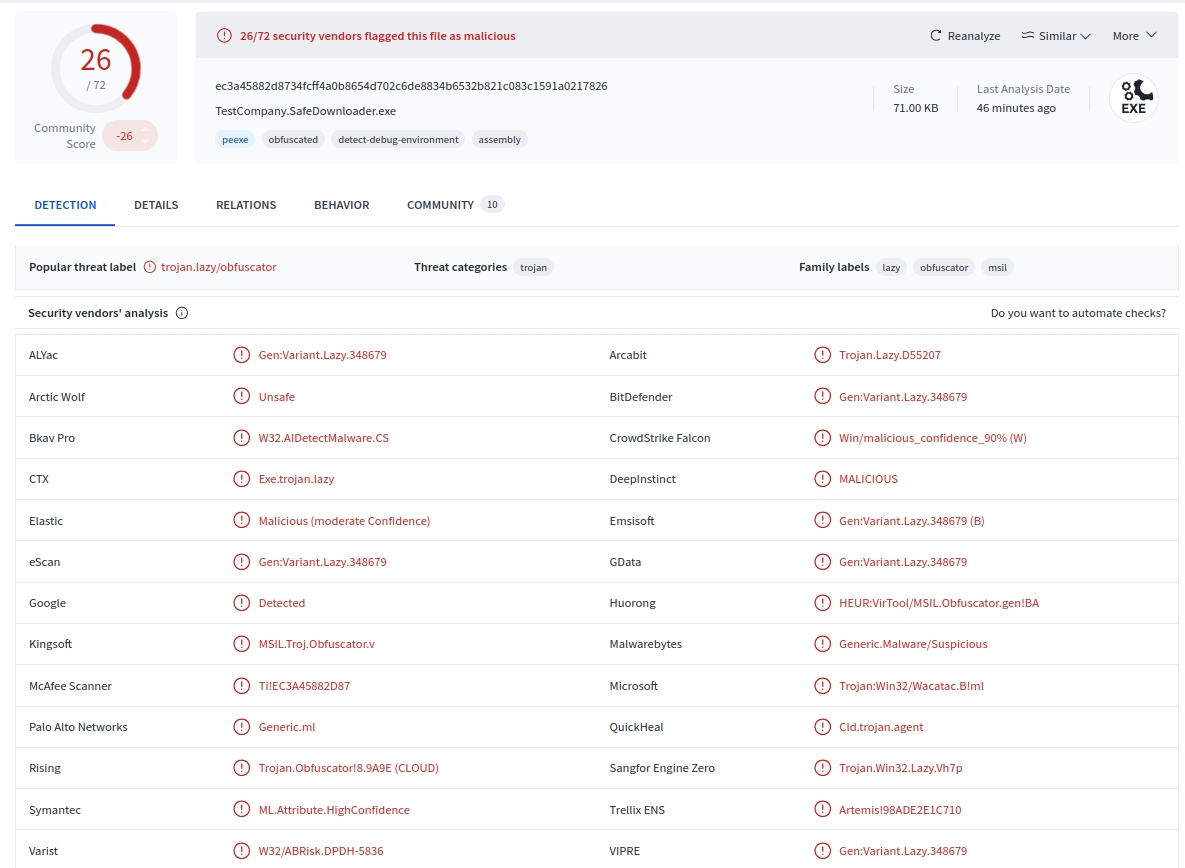
Behavior:
- Monitors the clipboard for cryptocurrency wallet addresses (BTC, ETH, LTC, etc.).
- Replaces copied wallet addresses with attacker-controlled ones.
- Windows-only payload. It targets Windows users downloading from Xubuntu.org.
- No confirmed reports of cryptocurrency theft at the time of this writing.
Technical Context
The malicious file was hosted within a WordPress uploads path "
/wp-content/uploads/", suggesting the compromise occurred via a vulnerable plugin or outdated component.A similar minor incident in September 2025 served malvertising on the same domain, implying the attackers retained access.
The Xubuntu team has disabled the affected download page and announced a migration to a static-site architecture to prevent further injection or file tampering.
What Was Not Affected
Direct ISO images and checksums hosted on Canonical’s official mirror (cdimage.ubuntu.com) were not compromised.
Only the torrent download link from the Xubuntu.org domain was affected.
Recommendations
If you downloaded Xubuntu via torrent from Xubuntu.org between October 18–19, 2025:
- Delete xubuntu-safe-download.zip immediately.
- Scan your Windows system for malware or autorun persistence keys.
- Rotate cryptocurrency wallets and reset all associated credentials.
- Verify all future downloads against SHA256/PGP checksums provided on Canonical mirrors.
Sources:
-
Recap of Record Setting Hyper-Volumetric DDoS Attacks in 2025 (CloudFlare)
Overview:
Recent months have seen a dramatic escalation in Distributed Denial-of-Service (DDoS) attacks, both in volume and packet rate. Two ultra-high-volume events stand out: a 7.3 Tbps / 4.8 Bpps attack on May 15 2025, and a later and eye watering 11.5 Tbps / 5.1 Bpps assault on September 3 2025, both successfully mitigated by Cloudflare.Key Details:
- The 7.3 Tbps attack targeted an unnamed hosting provider in mid-2025 and delivered roughly 37.4 TB of data in ~45 seconds.
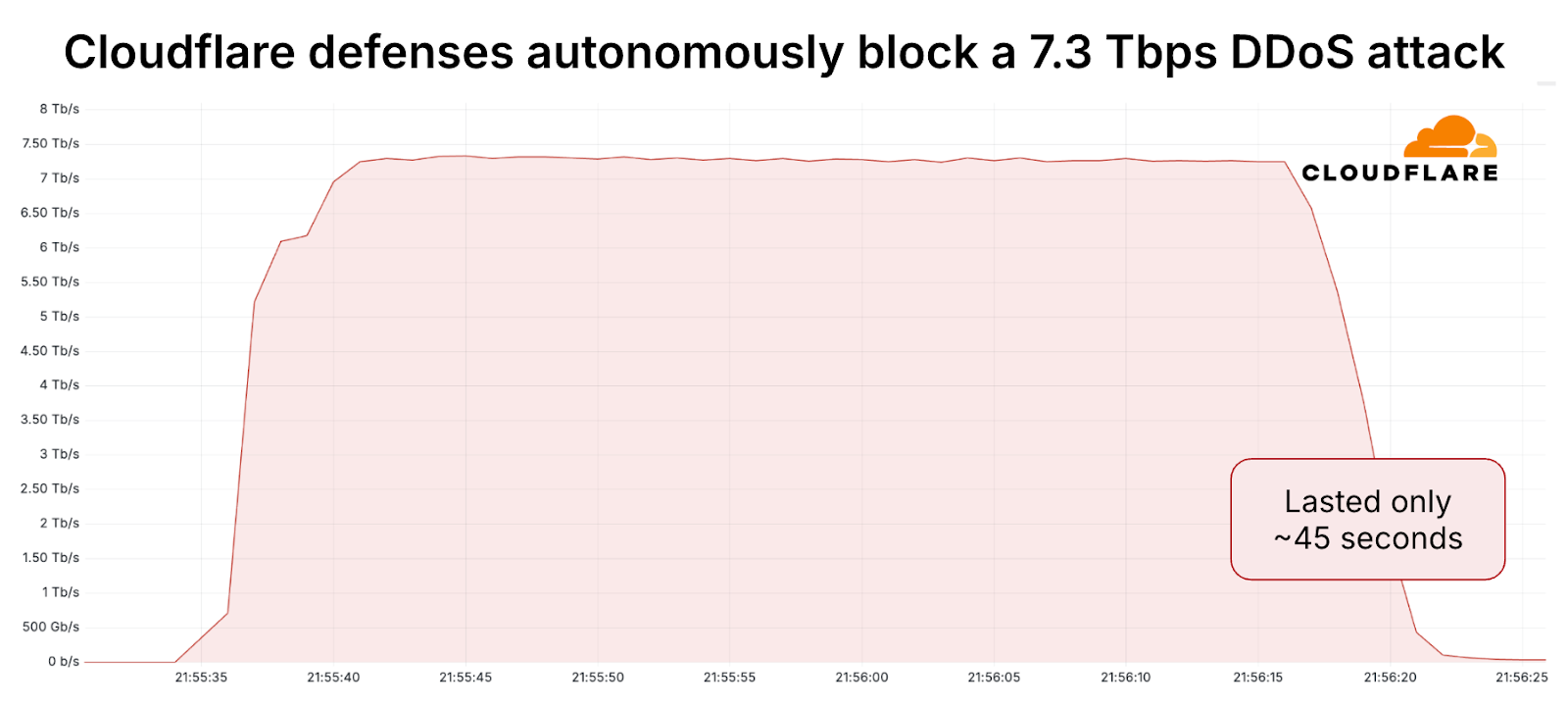
- The 11.5 Tbps event occurred in September 2025, lasted about 35 seconds, and was primarily a UDP flood. Sources included cloud providers and massive IoT botnets.
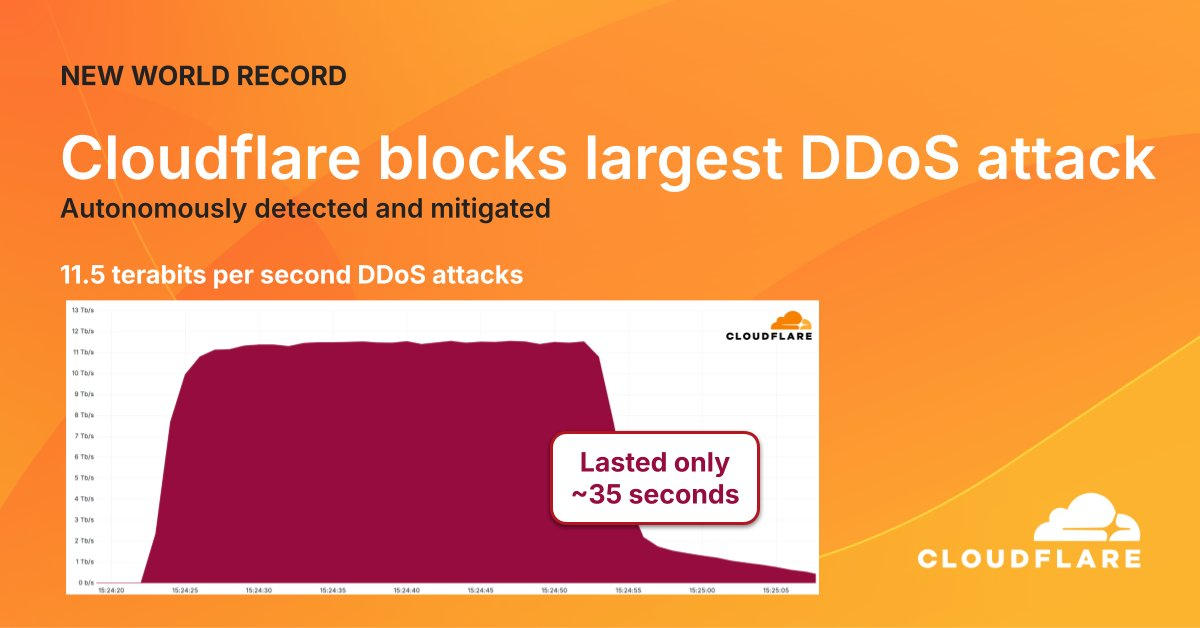
- These attacks reflect a trend: “hyper-volumetric” DDoS defined as >1 Tbps or >1 Bpps are now occurring at disproportionately high rates.
Final Thoughts:
- The sheer rate and short duration (under a minute) make detection and response challenging.
- Attackers are increasingly deploying multi-vector strategies and exploiting large botnets of compromised IoT/cloud devices.
- These record-breaking DDoS events signal that we’ve entered a new era of scale in DDoS attacks. The days of only mitigating sub-100 Gbps events are behind us - now it’s multi-Tbps and packet rates in the billions.
Sources:
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login

