Infosec News
-
Troy Hunt's Mailchimp List Breached via Phishing Attack in March 2025While old news, Troy Hunt, the security researcher behind Have I Been Pwned, disclosed that his Mailchimp account was compromised on March 25, 2025, via a phishing attack. The attacker tricked him into entering credentials on a fake Mailchimp SSO site, then swiftly replayed both his username and OTP to the real Mailchimp login endpoint. Within moments, the intruder exported his full mailing list—over 16,000 records—before access could be revoked.
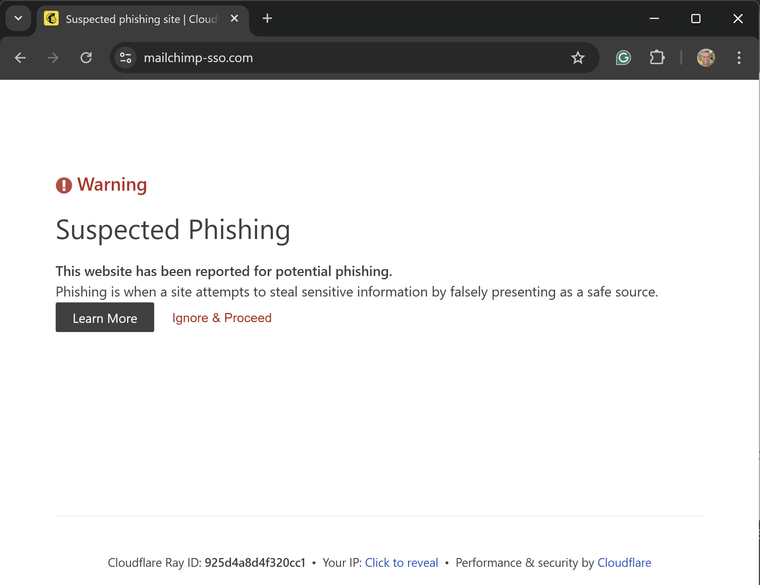
Cloudflare quickly blocked the phishing site, but not before Troy's credentials were compromised:
The stolen data included subscriber email addresses, subscription preferences, and metadata such as IP addresses, derived lat/long, time zones, and timestamps. Alarmingly, it also contained over 7,500 unsubscribed addresses, prompting questions about Mailchimp’s data retention policies and GDPR compliance.
The phishing email was sent to a unique Mailchimp-specific address, suggesting the attacker may have sourced their target list from a previous Mailchimp-related breach, possibly the 2022 crypto-targeted incident. Other organizations have reported receiving identical phishing messages, further supporting this theory.
Troy has since rotated credentials, removed the API key, and had his account access restored. The compromised data has already been loaded into Have I Been Pwned, and affected users have been notified.
https://haveibeenpwned.com/PwnedWebsites#TroyHuntMailchimpList
https://www.troyhunt.com/a-sneaky-phish-just-grabbed-my-mailchimp-mailing-list/
-
FBI Warns Senior U.S. Officials of AI Voice Cloning and Smishing Campaigns
The FBI has issued an urgent alert about a wave of sophisticated social engineering attacks where threat actors impersonate high-ranking U.S. officials using AI-generated voice cloning and malicious text messages (smishing).
These messages have targeted both current and former government personnel as well as their contacts, aiming to build trust and eventually extract access to sensitive accounts or information. The tactics mirror spear-phishing, but leverage newer AI tools to enhance credibility.
Notably:
- AI voice cloning usage surged 442% in late 2024, making vishing (voice phishing) a potent new threat.
- Publicly available speeches or interviews are often enough to train a voice model with highly realistic results.
- These methods are now part of campaigns by state-linked groups and ransomware actors like Scattered Spider and AlphV.
- Mandiant reports successful red-team use of cloned voices to bypass security teams and deploy malware.
This trend reflects a broader rise in AI-powered attack vectors and underscores the need for multi-factor authentication, strict access controls, and ongoing employee training in recognizing manipulative communications.
Sources:
https://www.ic3.gov/PSA/2025/PSA250515https://www.cybersecuritydive.com/news/fbi-us-officials-impersonated-text-ai-voice/748334/
-
Inside Job - Coinbase Faces $400M Fallout After Insider Data Breach and $20M Ransom Demand
On May 15, 2025, Coinbase disclosed a significant data breach involving bribed overseas customer support agents who leaked sensitive customer information. The breach affected approximately 1% of users, compromising data such as names, contact details, masked Social Security numbers, bank account identifiers, government-issued ID images, and transaction histories.
The attackers demanded a $20 million ransom, which Coinbase refused to pay. Instead, the company established a $20 million reward fund for information leading to the arrest and conviction of the perpetrators. The breach is projected to cost Coinbase between $180 million and $400 million, encompassing remediation efforts and customer reimbursements.
In response, Coinbase has terminated the involved contractors, enhanced fraud monitoring, and is cooperating with U.S. and international law enforcement agencies. The U.S. Department of Justice has initiated an investigation into the incident.
The breach has also led to multiple lawsuits alleging inadequate security measures by Coinbase. Despite the breach, Coinbase confirmed that no passwords, private keys, or customer funds were compromised.
Sources:
https://cybersecuritynews.com/coinbase-hacked
https://www.businessinsider.com/coinbase-hack-crypto-scam-fraud-coin-sp500-listing-cryptocurrency-exchange-2025-5
https://www.thetimes.com/business-money/companies/article/coinbase-says-hackers-bribed-staff-in-cyberattack-9vgkbq5wh -
Critical RCE Vulnerability in Lexmark Printers (CVE-2025-1127) Threatens Networks
A critical vulnerability, CVE-2025-1127, has been identified in over 150 Lexmark printer models, including the CX, MX, XC, and CS series. This flaw allows remote attackers to execute arbitrary code on unpatched devices by exploiting a combination of path traversal (CWE-22) and race condition (CWE-362) vulnerabilities in the embedded web server. The vulnerability has been assigned a CVSS v3.1 score of 9.1 (Critical).
Discovered by DEVCORE researchers through Trend Micro’s Zero Day Initiative, the exploit requires network access and valid credentials. However, many devices remain vulnerable due to unchanged default admin credentials. Attackers can leverage this flaw to deploy ransomware, exfiltrate documents, or use compromised printers as entry points into corporate networks.
Affected Models:
The vulnerability impacts devices running firmware versions released before February 13, 2025. A wide range of Lexmark models are affected, including CX950, XC9525, MX953, CX961, XC9635, CS963, CX833, MS531, MX532, CS531, CX930, XC9325, CS943, MX432, CX730, CS730, MS321, M1242, B2338, MS622, MX321, MB2338, MS725, B2865, MS822, MX721, XM5365, MB2770, CS622, CS421, C2325, CX522, MC2535, CX421, MC2325, B2236, MS331, M1342, B3442, XM1342, MX331, MB3442, C3426, CS431, CS331, C3224, C2326, MC3426, CX431, XC2326, MC3426, MC3224, CX331, CX820, XC6152, CS820, C6160, CS720, C4150, CX725, XC4140, CS921, C9235, CX920, XC9225, and more.Lexmark has released patched firmware versions with “.206” or “.408” suffixes across 38 distinct product families. Administrators can verify firmware versions through the control panel’s Settings → Reports → Menu Setting Page.
Sources:
https://gbhackers.com/critical-vulnerability-in-lexmark-printers/
https://cyberpress.org/lexmark-printer-flaw/ -
AirBorne Alert: 23 Zero-Click Vulnerabilities in Apple AirPlay Expose Billions of Devices to RCE Threats
Security researchers at Oligo Security have disclosed 23 previously unknown vulnerabilities in Apple's AirPlay protocol, collectively dubbed “AirBorne.” These flaws affect Apple and third-party AirPlay-compatible devices, including smart TVs, speakers, and in-car systems like CarPlay. Critically, several of the bugs are zero-click and wormable, meaning attackers can exploit them without user interaction and potentially spread laterally across networks.
The vulnerabilities allow remote code execution (RCE) and device hijacking over the same Wi-Fi network. Attackers can silently compromise a device, execute arbitrary payloads, and even eavesdrop via smart systems, turning entertainment features into serious security liabilities.
Impacted devices range from iPhones, iPads, and MacBooks to third-party IoT devices, many of which may not receive timely security updates. Despite Apple patching the core vulnerabilities in recent OS updates, many third-party vendors remain exposed, as they rely on outdated SDKs or unsupported firmware.
Key Points:
- Zero-click, wormable RCE vulnerabilities
- Exploitable via Wi-Fi proximity, no pairing needed
- 23 CVEs affecting both Apple and OEM AirPlay implementations
- Attacks demonstrated on smart TVs, speakers, and vehicle infotainment systems
- Major concern for unpatched third-party devices still using vulnerable AirPlay stacks
- Researchers urge users to disable AirPlay on untrusted networks
- Apple users should update iOS/macOS immediately
- Devs/OEMs must audit third-party SDKs and deploy firmware updates ASAP
Sources:
- https://www.kaspersky.com/blog/airborne-wormable-zero-click-vulnerability-in-apple-airplay/53443/
- https://timesofindia.indiatimes.com/technology/tech-news/apple-airplay-may-have-major-security-flaws-that-can-allow-hackers-to-hijack-devices-researchers-claim/articleshow/121346229.cms
- https://www.ndtv.com/world-news/apple-warns-iphone-users-advises-them-to-urgently-turn-off-this-feature-8464822
-
GhostSpy Android RAT: Stealthy Remote Control Malware
A newly surfaced Android RAT dubbed GhostSpy is making waves in the wild. It uses Accessibility abuse, UI automation, and overlay techniques to gain full device control — logging keystrokes, stealing 2FA codes, bypassing secure banking app protections, and maintaining persistence through anti-uninstall overlays.
High level overview:
- Installs silently via dropper APK using update.apk
- Bypasses permissions with automated UI taps
- Screenshares even protected apps via UI reconstruction
- Intercepts 2FA codes from Google/Microsoft Authenticator
- Remotely wipes device via Device Admin API
- Uses fake full-screen uninstall warnings
- Real-time audio/video surveillance, SMS exfiltration
Sources:
-
Unimed Data Breach Exposes 14 Million Patient-Doctor Communications
Unimed, Brazil's largest healthcare cooperative, inadvertently exposed over 14 million patient-doctor messages through an unsecured Apache Kafka instance. The breach included sensitive data such as names, phone numbers, email addresses, Unimed card numbers, uploaded images, documents, and real-time chat logs from both human doctors and Unimed's AI chatbot, "Sara".
Cybernews researchers discovered the misconfigured Kafka broker on March 24, 2025, and notified Unimed on March 31. The exposed instance was secured by April 7. Unimed stated on May 29 that the incident was isolated, promptly resolved, and that there is no evidence, so far, of any leakage of sensitive data from clients, cooperative physicians, or healthcare professionals. An in-depth investigation remains ongoing.
Sources:
-
ViciousTrap: Persistent SSH Backdoors Found in 9,000+ ASUS Routers
A sophisticated cyberattack campaign, dubbed ViciousTrap, has compromised over 9,000 ASUS routers, establishing persistent SSH backdoors that survive reboots and firmware updates.
Discovered by GreyNoise in March 2025, the attackers exploit a command injection vulnerability (CVE-2023-39780) and authentication bypass techniques to gain access. They then enable SSH on port 53282 and insert their own public keys into the routers' NVRAM, ensuring persistence even after firmware upgrades.
The attack is stealthy, involving no malware installation and disabling router logging to avoid detection. The compromised routers are believed to be part of a larger operational relay box (ORB) network, potentially laying the groundwork for future botnet activities.
Indicators of Compromise (IOCs):
- SSH enabled on TCP port 53282
- Presence of unauthorized SSH public keys
- Known malicious IP addresses:
- 101.99.91.151
- 101.99.94.173
- 79.141.163.179
- 111.90.146.237
Sources:
-
New Linux Flaws Allow Password Hash Theft via Core Dumps in Ubuntu, RHEL, FedoraTwo information disclosure flaws have been identified in apport and systemd-coredump, the core dump handlers in Ubuntu, Red Hat Enterprise Linux, and Fedora, according to the Qualys Threat Research Unit (TRU).
CVE-2025-5054 (CVSS score: 4.7) - A race condition in Canonical apport package up to and including 2.32.0 that allows a local attacker to leak sensitive information via PID-reuse by leveraging namespaces CVE-2025-4598 (CVSS score: 4.7) - A race condition in systemd-coredump that allows an attacker to force a SUID process to crash and replace it with a non-SUID binary to access the original's privileged process coredump, allowing the attacker to read sensitive data, such as /etc/shadow content, loaded by the original processSource: https://thehackernews.com/2025/05/new-linux-flaws-allow-password-hash.html?m=1&s=09
-
FBI: Over 900 Organizations Hit by Play Ransomware, SimpleHelp Exploits and ESXi Variants Used
The Play ransomware group, also known as Playcrypt, has compromised approximately 900 organizations since its emergence in June 2022, according to a newly updated advisory from the FBI, CISA, and Australian Cyber Security Centre (ACSC). Initially thought to have about 300 victims as of October 2023, Play has seen a rapid expansion, becoming one of the most active ransomware gangs in 2024 and into 2025.
Play operates as a closed ransomware-as-a-service (RaaS) group employing double-extortion tactics, exfiltrating data before encrypting it to pressure victims into paying ransoms.
Play ransomware’s advanced operational security, tailored builds per target, and use of human-operated extortion methods reflect a shift toward more customized, persistent threat campaigns. The exploitation of RMM software like SimpleHelp and targeting of ESXi environments shows an intent to hit core infrastructure, increasing pressure on victims to pay.
Exploited Vulnerabilities:
Source:
https://www.securityweek.com/fbi-aware-of-900-organizations-hit-by-play-ransomware/ -
Supply-Chain RAT Compromise Strikes 16 Gluestack React-Native-Aria Packages With Nearly 1 Million Weekly Downloads
On June 6, 2025, threat actors injected heavily obfuscated remote-access-trojan (RAT) code into a new version of the Gluestack react-native-aria/focus package on NPM. Within hours, 16 of the 20 total Gluestack React-Native-Aria packages, totaling roughly 960,000 weekly downloads, were compromised. The malicious payload was appended (padded with spaces) to the end of each package’s lib/index.js file, making it easy to miss via the standard NPM code viewer.
Aikido Security’s analysis revealed that the RAT establishes a persistent connection to the attacker’s command-and-control (C2) server and accepts a variety of commands, including directory changes, file uploads, and arbitrary shell execution via child_process.exec(). Additionally, the malware prepends a fake Python path to the Windows PATH environment variable, hijacking legitimate python and pip invocations to execute malicious binaries silently.
Attempts by Aikido researcher Charlie Eriksen to contact Gluestack maintainers via GitHub issues have gone unanswered, and while NPM has been alerted, remediation could take several days. This campaign appears linked to the same actors behind four other NPM compromises earlier this week (biatec-avm-gas-station, cputil-node, lfwfinance/sdk, and lfwfinance/sdk-dev), underscoring the growing risk of high-volume supply-chain attacks in the JavaScript ecosystem.
-
GitLab Urgently Patches Multiple High‑Severity Flaws Allowing Account Takeover and CI/CD Job Injection
Critical versions released: GitLab has shipped security updates, Community and Enterprise editions 18.0.2, 17.11.4, and 17.10.8, addressing several severe vulnerabilities. Administrators of self-hosted instances are urged to upgrade immediately. GitLab.com already runs the patched versions; dedicated customers unaffected.
Vulnerabilities patched:
- HTML injection / account takeover (CVE‑2025‑4278): A malicious actor could exploit this flaw via the search page, injecting HTML to hijack user sessions and take over accounts remotely.
- Auth bypass in Ultimate EE, CI/CD job injection (CVE‑2025‑5121): This missing-authorization bug allows authenticated users on Ultimate editions to inject arbitrary CI/CD jobs into any future pipelines, raising risk of code injection. Exploitation requires Ultimate license and authenticated access.
- Cross-site scripting (CVE‑2025‑2254): Enables session hijacking via script execution in snippet viewer.
- Denial-of-Service (CVE‑2025‑0673): Infinite redirect loop forcing memory exhaustion and denial of service.
-
Widespread Google Cloud & Cloudflare Outage Disrupts Spotify, Discord, Gmail & More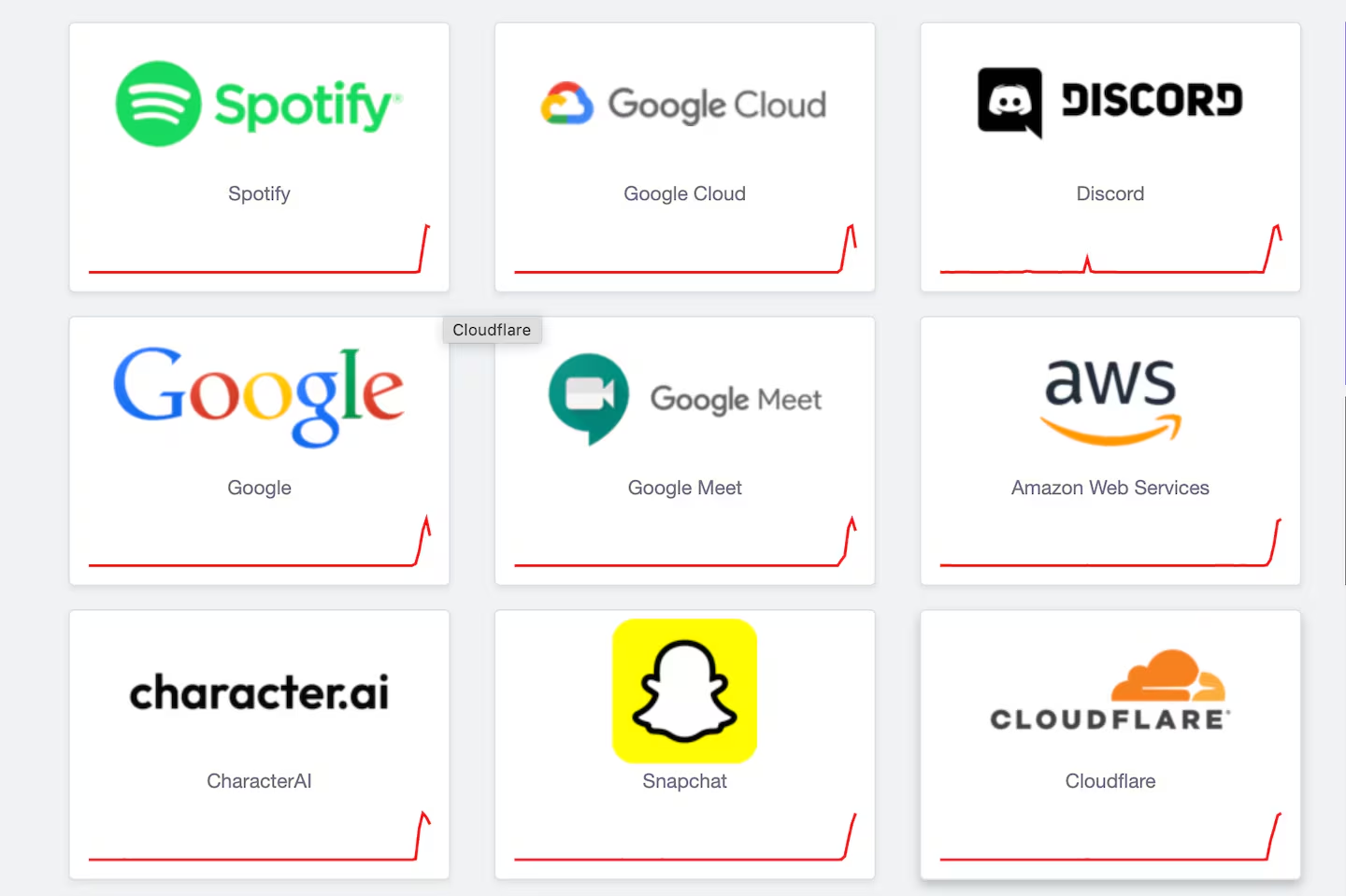
Timeline & Root Cause
- The outage began approximately 10:51 UTC on June 12, when Google Cloud’s Identity and Access Management (IAM) service began failing, triggering cascading disruptions.
- Around 18:19 UTC, Cloudflare reported numerous authentication and connectivity failures, notably in Access and Zero Trust WARP services.
Services Impacted
- Google Cloud: Over 50 services impacted, BigQuery, App Engine, Cloud Storage, Vertex AI Search, Cloud Shell, Memorystore, Dataproc, Workstations, IAM tools, and more.
- Cloudflare: Authentication failures affected Access, Workers KV, Stream, dashboard, AI Gateway, AutoRAG, WARP, Durable Objects; core network and CDN remained largely unaffected.
Downstream Effects
- Major platforms including Spotify, Discord, Google Workspace (Gmail, Meet), Twitch, Snapchat, Shopify, OpenAI services, and Replit experienced intermittent outages.
- Outage trackers like Downdetector, ThousandEyes, and similar services showed massive report spikes around midday UTC.
Mitigation & Recovery Status
- By 20:09 UTC, Google’s engineering teams had identified the root cause, initiated mitigations, and began service restorations, most regions recovered, except us-central1, with no ETA for full restoration.
- Cloudflare confirmed service recovery under way around 18:30 UTC, though some intermittent authentication errors persisted while caches refreshed.
- A scheduled maintenance was ongoing in Cloudflare’s Dallas data center earlier (08:00–10:00 UTC), but engineers affirm it was unrelated to this global outage.
Sources:
-
Digital Fallout: U.S. Firms Brace for Cyber Crossfire in Iran-Israel Escalation
As Israel and Iran engage in direct military strikes, a covert cyberwar is unfolding in parallel and U.S. companies may soon be caught in the blast radius. Cybersecurity experts are sounding the alarm over a 700% surge in Iranian cyberattacks on Israeli targets since Israel’s June 12 missile strike on Tehran. These attacks include disinformation campaigns, DDoS floods, and phishing operations with potential to escalate into more destructive cyber campaigns depending on the U.S. response.
- U.S. ISACs (Food & Ag, IT) are warning infrastructure operators to harden defenses now.
- Radware reports a 7x increase in Iranian cyber activity.
- Fake SMS alerts are being sent, masquerading as official Israeli government warnings.
- Flashpoint warns: If Iran pivots toward U.S. targets, expect state-backed ransomware or wiper malware to hit critical infrastructure.
Source:
https://www.axios.com/newsletters/axios-future-of-cybersecurity-1038e950-4889-11f0-b558-17dac864894e -
Major Data Breach at Krispy Kreme – Sensitive Employee Data Leaked
Krispy Kreme Doughnut Corporation has confirmed a major data breach compromising sensitive personal data of thousands of current and former employees, as well as their family members. The intrusion was discovered on November 29, 2024, with attackers gaining unauthorized access to internal systems.
Compromised data includes:
- Social Security Numbers (SSNs)
- Dates of Birth
- Driver’s License & Passport Numbers
- Credit/Debit Card Info (w/ CVV)
- Financial Account Logins
- Biometric & Health Insurance Data
- U.S. Military IDs, USCIS & Alien Reg. Numbers
- Digital Signatures & Email Credentials
Source:
-
No, the “16 Billion Credentials” Leak Isn’t a New Breach
An explosive claim, but not a fresh hack. Earlier this week, headlines announced “one of the largest data breaches in history”, a staggering 16 billion credentials allegedly leaked from platforms like Google, Facebook, Apple, and Telegram. However, cybersecurity research reveals this is not a fresh breach at all. Instead, it’s an aggregated dump of older data sourced from infostealer malware, past data breaches, and credential-stuffing attacks compiled into 30 datasets and briefly exposed online.
Where did the data come from?
- Infostealer logs: Malware installed on infected machines that harvest browser and app credentials, storing them in text-based "logs" structured as username:password.
- Credential stuffing collections: Dumps from past breaches that attackers used to test login combos across services.
- Aggregated stale dumps: Some large collections (e.g., 184 million credentials) surfaced earlier, and now combined into a massive compilation.
Despite the hype, no central platform was recently compromised in this event.
Sources:
-
U.S. House Bans WhatsApp on Gov Devices Citing "High-Risk" Security Flaws
On June 23, 2025, the U.S. House of Representatives officially banned WhatsApp from all government-issued devices, citing serious cybersecurity concerns. The directive came from the House’s Chief Administrative Officer and was based on assessments by the Office of Cybersecurity.
Why the Ban?
- Lack of transparency in WhatsApp’s data handling and encryption models
- Stored data not encrypted at rest, violating federal standards
- General classification of WhatsApp as a “high-risk” communication platform
Sources:
-
Citrix Netscaler Hit with Critical Actively Exploited CVEs
A newly discovered critical vulnerability in Citrix NetScaler, CVE-2025-5777, is raising serious alarms. The flaw stems from insufficient input validation when NetScaler is configured as a Gateway (VPN, ICA Proxy, CVPN, RDP Proxy) or AAA virtual server. This vulnerability carries a CVSS score of 9.3 and may allow memory overread, potentially exposing sensitive data such as session tokens.
In parallel, Google researchers confirmed a second critical flaw, CVE-2025-6543, is actively being exploited as a zero-day. This is a memory overflow vulnerability (CVSS 9.2) that can lead to unintended control flow and denial of service. Like CVE-2025-5777, it affects NetScaler appliances configured as a Gateway or AAA vServer.
Both vulnerabilities impact the following NetScaler ADC and Gateway builds:
- NetScaler ADC and NetScaler Gateway 14.1 BEFORE 14.1-43.56
- NetScaler ADC and NetScaler Gateway 13.1 BEFORE 13.1-58.32
- NetScaler ADC 13.1-FIPS and NDcPP BEFORE 13.1-37.235-FIPS and NDcPP
- NetScaler ADC 12.1-FIPS BEFORE 12.1-55.328-FIPS
- Note: 12.1 and 13.0 are End-of-Life (EOL) and are vulnerable
Citrix warns that Secure Private Access on-prem and hybrid deployments using vulnerable NetScaler instances are also at risk.
Cloud Software Group, alongside multiple national security agencies, are urging all customers to immediately patch or upgrade to supported builds. For EOL versions (12.1, 13.0), upgrades are mandatory to eliminate exposure.
Sources:
-
Fake SonicWall NetExtender Targets VPN Credentials
A new remote access malware campaign is distributing a trojanized version of SonicWall’s NetExtender VPN client, named SilentRoute, to harvest VPN credentials and other sensitive configuration data from unsuspecting users.
SonicWall NetExtender Trojan (SilentRoute):
- The trojan impersonates NetExtender v10.3.2.27, hosted on a spoofed website (now taken down).
- It was digitally signed by CITYLIGHT MEDIA PRIVATE LIMITED, possibly a compromised certificate authority or abuse of a legitimate cert.
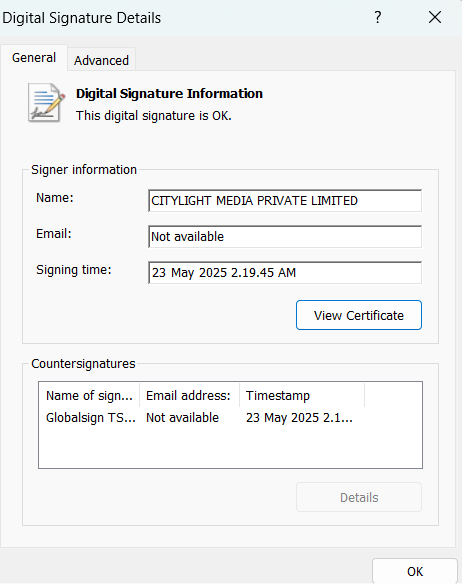
- The threat targets users searching for VPN downloads via:
- SEO poisoning
- Phishing
- Malvertising
- Social engineering on platforms like Facebook
Technical Behavior:
- Modifies NeService.exe and NetExtender.exe
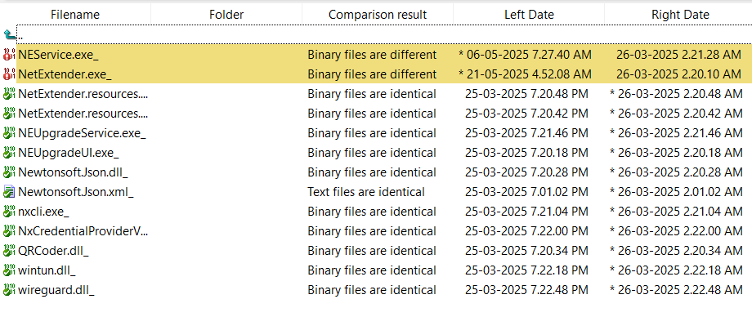
- Bypasses normal digital signature validation checks.
- Exfiltrates VPN config data including username, password, and domain to 132.196.198.163 using port 8080.
- Malicious behavior triggered upon clicking "Connect" inside the fake VPN client.
Sources:
-
CISA & NSA Double Down on Memory-Safe Languages for Secure-by-Design Software
The latest joint guidance from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and National Security Agency (NSA) elevates memory-safe languages (MSLs) such as Rust, Go, Java, Python, and C# from “best practice” to a national-security baseline. The agencies cite fresh data showing that 70–75 percent of exploited CVEs in the wild are rooted in memory bugs; Google’s Android team, for example, slashed that figure from 76 percent in 2019 to 24 percent in 2024 after mandating Rust/Java for all new code.
CISA and NSA stress that C and C++ can never be fully secured against buffer overflows, use-after-free, data races, and similar flaws because developers, not the compiler, must enforce safety. MSLs collapse whole vulnerability classes by enforcing bounds checking, lifetime/ownership rules, or automatic garbage collection at compile or run time.
Recommended first steps:
- Inventory legacy C/C++ components handling untrusted input.
- Mandate MSLs for all new repositories and features.
- Add Rust clippy, Go govulncheck, or equivalent linters to CI/CD.
- Track % unsafe code (Rust) or % legacy LOC to measure progress.
- Provide developers a focused “borrow-checker / GC” bootcamp to shorten the learning curve.
For those who have been following along, check my post from April 2025 concerning "Systems Programming: Memory Safety":
Sources:


