Infosec News
-
Nation-State Hackers Breach F5 Networks
Summary
F5 Networks has confirmed a major security breach in which a nation-state-linked actor gained unauthorized access to internal systems and exfiltrated portions of BIG-IP source code and information on undisclosed vulnerabilities.
The intrusion is believed to have persisted for roughly 12 months before discovery.The company detected the incident on August 9, 2025, and delayed public disclosure at the request of the U.S. Department of Justice.
There is no indication that CRM, financial, support, or iHealth systems were accessed, although some customer configuration files were included in the stolen data.Technical and Attribution Details
- The attack is attributed to a Chinese cyber-espionage group tracked as UNC5221.
- The group deployed a custom backdoor named BRICKSTORM, previously used in intrusions against SaaS and BPO providers.
- The compromise targeted F5’s development environment, giving access to internal vulnerability data and code repositories.
- F5 brought in Mandiant and CrowdStrike for incident response, rotated all signing keys and credentials, and added additional security controls.
Government Response
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued Emergency Directive 26-01, requiring all federal agencies to:- Inventory all F5 BIG-IP, F5OS, BIG-IQ, and APM systems.
- Verify that management interfaces are not exposed to the internet.
- Apply vendor patches no later than October 22, 2025.
- Submit compliance reports to CISA by October 29, 2025.
CISA stated that the stolen source code and vulnerability information provide adversaries with a technical advantage for developing zero-day exploits.
CVEs and Patch References
Key vulnerabilities disclosed following the breach include:- CVE-2025-53868 – BIG-IP SCP/SFTP privilege escalation (CVSS 8.7)
- CVE-2025-61955 – F5OS command injection, appliance mode (CVSS 8.8)
- CVE-2025-57780 – F5OS arbitrary code execution, appliance mode (CVSS 8.8)
Administrators should immediately apply the latest firmware and software updates for BIG-IP, F5OS, BIG-IQ, APM, and BIG-IP Next (Kubernetes).
Recommended Actions:
- Patch all F5 systems immediately.
- Remove or restrict public access to management interfaces.
- Audit and retire end-of-life or unsupported devices.
- Monitor for anomalous configuration changes or new admin accounts.
- Treat F5 perimeter devices as high-risk until verified patched and hardened.
Sources:
- https://thehackernews.com/2025/10/f5-breach-exposes-big-ip-source-code.html
- https://www.reuters.com/technology/breach-us-based-cybersecurity-provider-f5-blamed-china-bloomberg-news-reports-2025-10-16/
- https://www.techradar.com/pro/security/significant-threat-to-us-networks-after-hackers-stole-f5-source-code-cisa-warns
-
Major Amazon Web Services (AWS) Outage
AWS is currently experiencing a major outage in the US-EAST-1 region, impacting dozens of core services and many third-party platforms.
Status: Degraded performance and elevated error rates across multiple services.
Root Cause (according to AWS): Internal subsystem failure tied to the monitoring of network load balancers and EC2 internal networking.Origin & propagation: Issues began around 3:11 a.m. ET in US-EAST-1, and have cascaded globally for services dependent on that region.
Affected AWS Services (partial list):
Core compute/storage/database services including EC2, S3, RDS, Lambda, CloudWatch, CloudFront, DynamoDB, SQS, SNS, ECS, EKS, Glue, Redshift, SageMaker, Cognito, Connect, VPC services, Step Functions, Secrets Manager, and more.
AWS lists around 90 services impacted.Third-Party Services / Platforms Impacted:
Major consumer/enterprise platforms reported disruptions: games like Fortnite, Roblox; apps like Snapchat, Venmo; smart home devices (Ring, Alexa); banks and financial apps; many SaaS services relying on AWS infrastructure.What this means for you:
- If you rely on AWS in US-EAST-1, expect slower API responses, partial failures, or launch errors (especially for new EC2 instances).
- If you rely on third-party services (SaaS, gaming, streaming, banking), you may see outages despite those services not being your direct provider.
Sources:
- AWS Status Page: https://health.aws.amazon.com/health/status
- Downdetector Report: https://downdetector.com/status/aws-amazon-web-services/
- Tom's Guide: https://www.tomsguide.com/news/live/amazon-outage-october-2025
- Reuters: https://www.reuters.com/business/retail-consumer/amazons-cloud-unit-reports-outage-several-websites-down-2025-10-20/
-
Xubuntu.org Compromised - Torrent Downloads Served Windows Malware
Over the weekend (October 18–19, 2025), the official Xubuntu website (xubuntu.org) was compromised. Attackers managed to inject a malicious download link into the torrent section of the downloads page. A similar attack also happened in September 2025 where attackers injected malicious javascript into non-English language pages of the site.
What Happened
The legitimate .torrent link was replaced with a ZIP archive:
xubuntu-safe-download.zipWhich contained files:
TestCompany.SafeDownloader.exe terms-of-service.txtThe EXE impersonated a “Xubuntu - Safe Downloader” GUI installer.
On execution, it installed itself to:%AppData%\Roamingand added a Windows registry key for persistence at startup.
Malware Behavior
The EXE was identified as a Crypto Clipper Trojan, flagged by 26/72 vendors on VirusTotal.
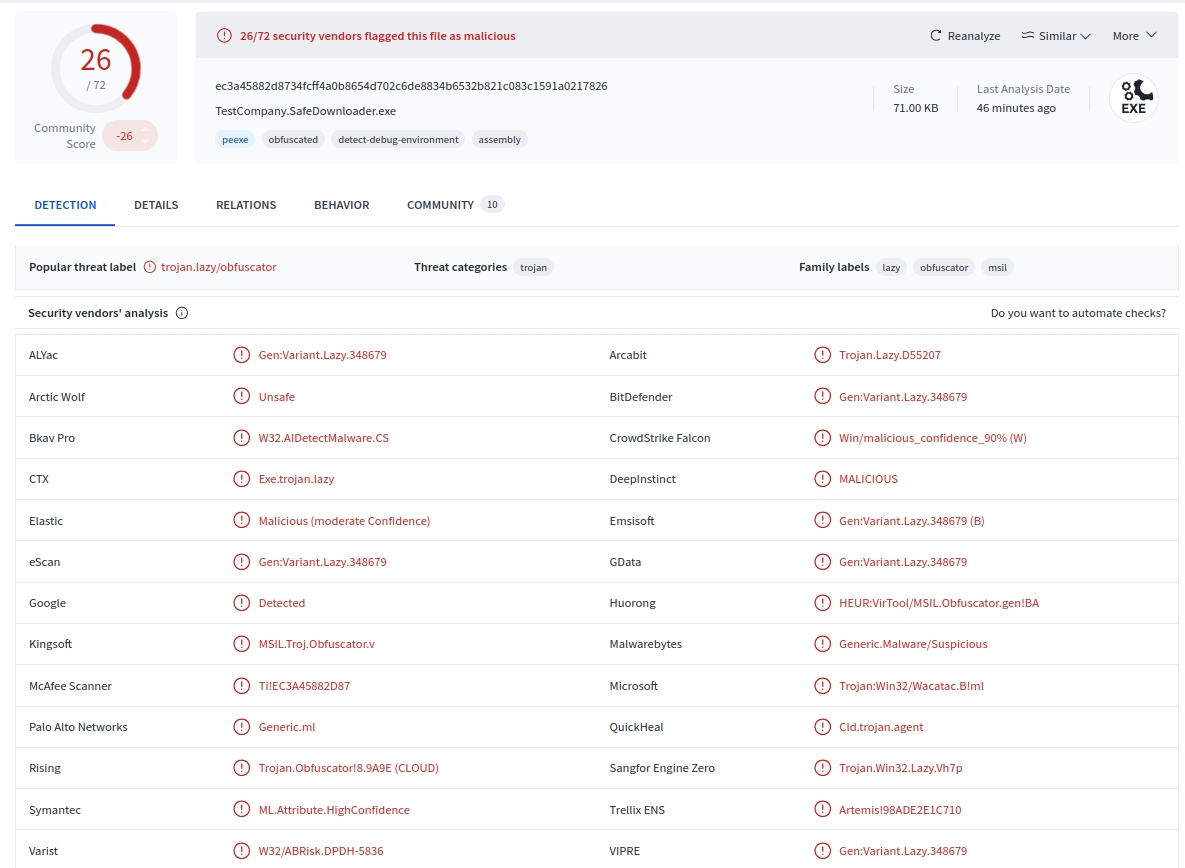
Behavior:
- Monitors the clipboard for cryptocurrency wallet addresses (BTC, ETH, LTC, etc.).
- Replaces copied wallet addresses with attacker-controlled ones.
- Windows-only payload. It targets Windows users downloading from Xubuntu.org.
- No confirmed reports of cryptocurrency theft at the time of this writing.
Technical Context
The malicious file was hosted within a WordPress uploads path "
/wp-content/uploads/", suggesting the compromise occurred via a vulnerable plugin or outdated component.A similar minor incident in September 2025 served malvertising on the same domain, implying the attackers retained access.
The Xubuntu team has disabled the affected download page and announced a migration to a static-site architecture to prevent further injection or file tampering.
What Was Not Affected
Direct ISO images and checksums hosted on Canonical’s official mirror (cdimage.ubuntu.com) were not compromised.
Only the torrent download link from the Xubuntu.org domain was affected.
Recommendations
If you downloaded Xubuntu via torrent from Xubuntu.org between October 18–19, 2025:
- Delete xubuntu-safe-download.zip immediately.
- Scan your Windows system for malware or autorun persistence keys.
- Rotate cryptocurrency wallets and reset all associated credentials.
- Verify all future downloads against SHA256/PGP checksums provided on Canonical mirrors.
Sources:
-
Recap of Record Setting Hyper-Volumetric DDoS Attacks in 2025 (CloudFlare)
Overview:
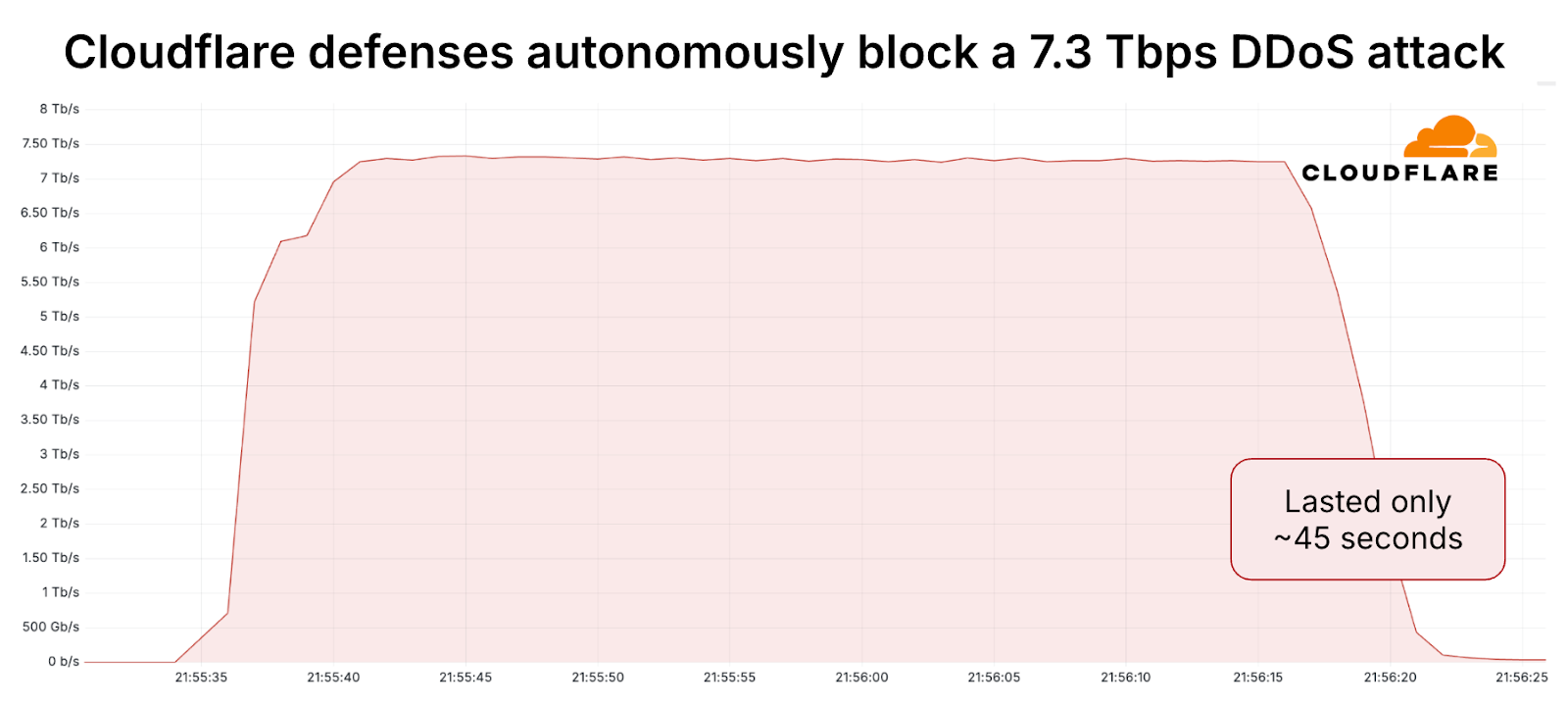
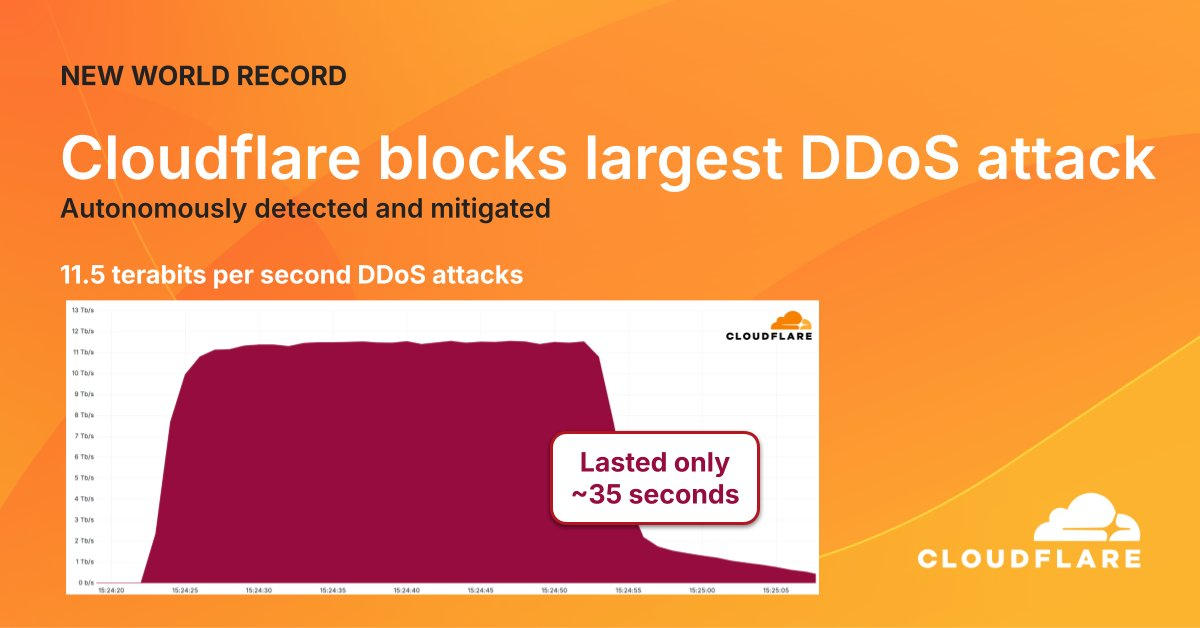
Recent months have seen a dramatic escalation in Distributed Denial-of-Service (DDoS) attacks, both in volume and packet rate. Two ultra-high-volume events stand out: a 7.3 Tbps / 4.8 Bpps attack on May 15 2025, and a later and eye watering 11.5 Tbps / 5.1 Bpps assault on September 3 2025, both successfully mitigated by Cloudflare.Key Details:
- The 7.3 Tbps attack targeted an unnamed hosting provider in mid-2025 and delivered roughly 37.4 TB of data in ~45 seconds.
- The 11.5 Tbps event occurred in September 2025, lasted about 35 seconds, and was primarily a UDP flood. Sources included cloud providers and massive IoT botnets.
- These attacks reflect a trend: “hyper-volumetric” DDoS defined as >1 Tbps or >1 Bpps are now occurring at disproportionately high rates.
Final Thoughts:
- The sheer rate and short duration (under a minute) make detection and response challenging.
- Attackers are increasingly deploying multi-vector strategies and exploiting large botnets of compromised IoT/cloud devices.
- These record-breaking DDoS events signal that we’ve entered a new era of scale in DDoS attacks. The days of only mitigating sub-100 Gbps events are behind us - now it’s multi-Tbps and packet rates in the billions.
Sources:
-
Qilin Ransomware Using WSL to Deploy Encryptors on Windows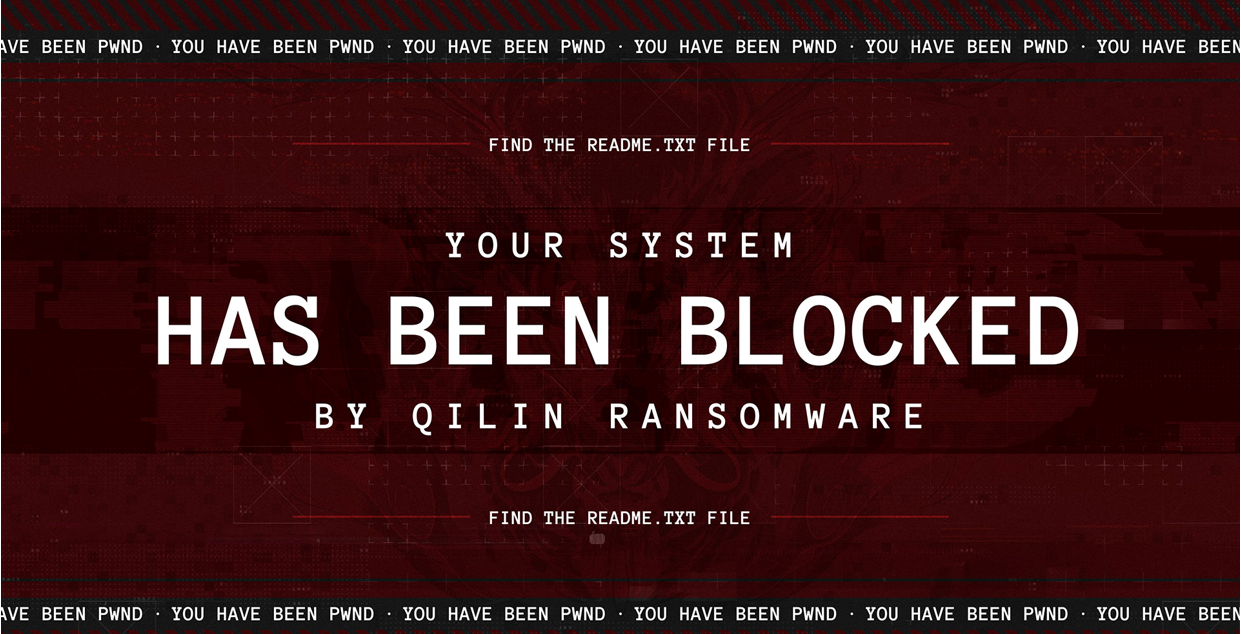
The Qilin ransomware group (formerly “Agenda”) has started abusing Windows Subsystem for Linux (WSL) to execute Linux ELF encryptors directly inside Windows environments, a move designed to evade EDR and antivirus detection.
Behavior:
- Threat actors gain access to a Windows host, then install or enable WSL via command-line tools or scripts.
- They transfer a Linux encryptor (ELF binary) using WinSCP and launch it through remote management tools like Splashtop (SRManager.exe).
- Since most Windows EDRs focus on PE-based behaviors, activity inside the WSL environment goes largely undetected.
Tactics:
- BYOVD attacks using vulnerable drivers (e.g. eskle.sys, rwdrv.sys, hlpdrv.sys) to disable security tools.
- Use of AnyDesk, ScreenConnect, Splashtop for persistence and remote access.
- DLL sideloading, dark-kill, and HRSword to remove traces or disable defenses.
- Manual inspection of files using Paint and Notepad before exfiltration.
Scale:
- Over 700 confirmed victims across 62 countries in 2025.
- Roughly 40 new victims/month during the second half of the year.
- Focus on hybrid Windows–Linux infrastructures, including VMware ESXi environments.
Sources:
- https://blog.talosintelligence.com/uncovering-qilin-attack-methods-exposed-through-multiple-cases/
- https://www.bleepingcomputer.com/news/security/qilin-ransomware-abuses-wsl-to-run-linux-encryptors-in-windows/
- https://www.trendmicro.com/en_us/research/25/j/agenda-ransomware-deploys-linux-variant-on-windows-systems.html
-
Rust CVE-2025-62518 - Critical RCE Vulnerability "TARmageddon" in Rust tar Libraries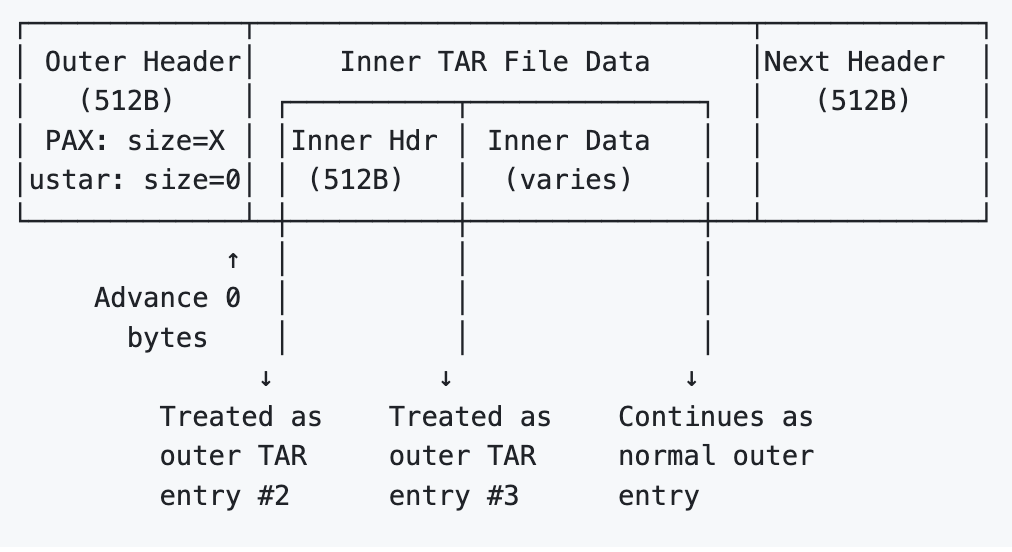
A new high-severity vulnerability (CVE-2025-62518, “TARmageddon”) has been disclosed in several Rust async tar libraries: async-tar, tokio-tar, and their forks.
The flaw is a boundary-parsing desynchronization in TAR header handling.
When archives contain PAX-extended headers that override the file size, the vulnerable parser incorrectly trusts the ustar size (often zero) to advance the read position. This misaligns the stream, letting hidden nested TAR data be treated as legitimate entries.This enables archive smuggling where attackers can insert extra files that overwrite configs or inject malicious build files. This can lead to remote code execution or supply-chain compromise when untrusted TARs are processed.
Note: this is not a memory safety vulnerability in Rust (which is inherintly memory safe), but a logic vulnerability in the code.
Impacted Ecosystem
- Directly vulnerable crates: async-tar, tokio-tar, krata-tokio-tar, astral-tokio-tar (<0.5.6)
Affected downstreams include:
- uv (Astral’s Python package manager)
- testcontainers
- wasmCloud, binstalk-downloader, and others
Attack Scenarios
- Python package RCE - malicious PyPI tarballs overwrite pyproject.toml.
- Container poisoning - crafted layers inject or overwrite files during unpack.
- BOM bypass - scanners approve the clean outer archive; hidden inner files slip through during extraction.
Sources:
-
Operation Endgame Takes Down Rhadamanthys, VenomRAT, and Elysium
Law enforcement has delivered another heavy blow to the cybercrime ecosystem. In the latest phase of Operation Endgame, agencies from nine countries coordinated a large-scale takedown targeting Rhadamanthys, VenomRAT, and Elysium malware infrastructure.
Between November 10 and 14, 2025, Europol and Eurojust led joint raids across Germany, Greece, and the Netherlands, seizing 20 domains and over 1,000 servers. A key VenomRAT suspect was also arrested in Greece on November 3.
According to Europol, the dismantled networks consisted of hundreds of thousands of infected systems and several million stolen credentials. Investigators also linked the primary Rhadamanthys operator to more than 100,000 compromised crypto wallets potentially worth millions of euros.
Lumen’s Black Lotus Labs reported that Rhadamanthys activity surged through late 2025, with over 500 active C2 servers and daily infections averaging 4,000 new IPs. More than 60 percent of its infrastructure was undetected on VirusTotal, making it one of the stealthier info-stealer networks active this year.
Europol suggests users verify possible compromise via politie.nl/checkyourhack and haveibeenpwned.com.
Operation Endgame has now disrupted numerous major threats, including IcedID, Bumblebee, Trickbot, SystemBC, and DanaBot. The cooperation between international law enforcement and private partners such as Shadowserver, CrowdStrike, Proofpoint, and Bitdefender continues to prove effective at dismantling large-scale criminal infrastructure.
Takeaway:
This action shows that even mature, well-distributed malware-as-a-service networks can be crippled when global coordination works. Expect the void left by Rhadamanthys and VenomRAT to be filled soon, likely by new variants or rebranded operations. Stay vigilant and monitor for related activity.Sources:
-
Go(lang) Turns 16
Go turned 16 this month, celebrating another milestone for one of the most influential languages in modern infrastructure. Originally built for simplicity and speed, Go now powers critical systems at companies like Google, Cloudflare, Uber, Dropbox, Stripe, Netflix, plus thousands of others.
Recent releases delivered major upgrades: Go 1.24 introduced traversal-safe filesystem APIs and a redesigned high-performance map implementation, while Go 1.25 added container-aware scheduling and the new Green Tea garbage collector, cutting GC overhead by 10-40% and paving the way for AVX-512 acceleration in Go 1.26. With stronger native cryptography (CAVP-certified), improved concurrency testing via testing/synctest, and expanding adoption across AI, cloud, and security tooling, Go’s 16th year cements it as a performant, memory safe, and production-ready foundation for the next generation of scalable systems.
Sources:
-
Cloudflare Outage Summary - 18 Nov 2025
On 18 November 2025 at 11:20 UTC, Cloudflare experienced a widespread outage that disrupted core CDN, security, and authentication services globally. While initially suspected to be a large-scale DDoS, the root cause was a malformed Bot Management feature file propagated across the edge.
Root Cause
A permissions change applied to a ClickHouse cluster at 11:05 UTC caused a metadata query used by Bot Management to return duplicate feature rows.
This doubled the size of the ML feature file, exceeding a 200-feature limit within Cloudflare’s proxy engines (FL + FL2).
When the oversized file propagated, proxies panicked and began returning HTTP 5xx errors for any request touching the bots module.Because ClickHouse nodes were being updated gradually, the system oscillated between “good” and “bad” configuration states every five minutes, heavily complicating diagnosis.
Impact
- CDN & Security: Widespread 5xxs, increased latency.
- Turnstile: Unavailable, breaking login flows.
- Workers KV: Heavy 5xx rates until bypassed at 13:05.
- Access: Auth failures for most users.
- Dashboard: Mostly up, but logins failed due to Turnstile + KV issues.
- Email Security: Minor degradation in spam detection accuracy, no critical impact.
Customers on the older FL proxy saw bot scores drop to zero, causing massive false positives for bot-blocking rules. FL2 customers saw outright 5xx errors.
Timeline (Key Events)
- 11:05 - ClickHouse permission change deployed.
- 11:20–11:28 - First propagation, core traffic starts failing.
- 13:05 - Workers KV + Access bypass reduces blast radius.
- 14:24 - Bad feature file generation halted; good file prepared.
- 14:30 - Global rollout of known-good file; major recovery begins.
- 17:06 - All services fully restored.
Why This Was So Severe
- Feature files update every few minutes globally.
- The malformed file exceeded a hard-coded runtime limit, causing unhandled panics.
- Debugging systems increased CPU load during the failure, amplifying latency.
- The recursive “good/bad” cycle produced misleading signals resembling an active attack.
Remediation Steps (In Progress)
- Harden validation of internal configuration files.
- Add global kill switches for rapid feature disablement.
- Prevent debugging/observability systems from burning excessive CPU during faults.
- Review failure modes across all proxy modules.
Summary
This was Cloudflare’s most serious outage since 2019 - not caused by malicious activity, but by an internal consistency failure in configuration generation. A single database permission change cascaded into a global edge failure due to assumptions in legacy code and missing safeguards.
Cloudflare has acknowledged the severity and is implementing systemic fixes to prevent feature-file-induced outages in the future.
Source:
-
Fortinet: FortiWeb Actively Exploited (again)
Fortinet has issued an alert for CVE-2025-58034, a command injection bug in FortiWeb (CVSS 6.7) that is being weaponized. The flaw is an OS command injection issue in FortiWeb’s HTTP and CLI handling that allows arbitrary code execution, but only after an attacker has authenticated by some other method.
Patches are available for all affected branches:
• 8.0.0 to 8.0.1 → update to 8.0.2
• 7.6.0 to 7.6.5 → update to 7.6.6
• 7.4.0 to 7.4.10 → update to 7.4.11
• 7.2.0 to 7.2.11 → update to 7.2.12
• 7.0.0 to 7.0.11 → update to 7.0.12Reported by Trend Micro’s Jason McFadyen, the flaw is already under active exploitation, prompting CISA to add it to the Known Exploited Vulnerabilities catalog with a federal patch deadline of November 25, 2025.
Exploit chain activity:
The situation escalates when paired with CVE-2025-64446, an authentication bypass silently patched by Fortinet in 8.0.2. According to Orange Cyberdefense and Rapid7, attackers are chaining the two bugs: bypassing authentication via CVE-2025-64446, then leveraging CVE-2025-58034 for command execution. This converts an authenticated-only issue into full unauthenticated RCE against unpatched appliances.Industry concern:
Security teams have raised concerns about Fortinet’s decision to patch these flaws before publishing advisories. Analysts note that silent patching provides attackers with a window of advantage and leaves defenders unaware of what they're exposed to until exploitation is already underway.Action required:
Apply the fixed releases immediately and audit FortiWeb instances for suspicious authenticated activity or anomalous command execution attempts, especially if systems were running vulnerable versions prior to Fortinet’s disclosure.Source:
-
Russian-linked Infostealer Hiding in Blender 3D Files
Morphisec recently tracked a campaign weaponizing malicious .blend files uploaded to 3D model marketplaces like CGTrader. These models contain embedded Python that executes automatically when Blender’s Auto Run feature is enabled.
Once opened, the script pulls a loader from a Cloudflare Workers domain, which then delivers a PowerShell stage responsible for fetching two ZIP payloads (ZalypaGyliveraV1 and BLENDERX). These unpack into %TEMP%, create Startup LNKs for persistence, and drop both StealC V2 and an auxiliary Python-based stealer.
StealC’s latest version extends support for data theft from:
- 23+ browsers, including Chrome 132+
- 100+ crypto wallet extensions and 15+ standalone crypto apps
- Telegram, Discord, Tox, Pidgin, VPN clients (ProtonVPN, OpenVPN), and mail clients (Thunderbird)
- UAC bypass
The variant analyzed reportedly had zero detections on VirusTotal, highlighting how quickly StealC’s developers are iterating.
Because Blender can auto-execute Python and marketplaces cannot inspect uploaded scripts, 3D assets now pose real supply-chain risk. Anyone pulling models from untrusted sources should disable auto execution:
- Blender → Edit → Preferences → uncheck “Auto Run Python Scripts”
Treat .blend files as potentially executable content and test untrusted assets in sandboxes or isolated VMs.
Source:
-
ShadyPanda Extension Campaign Hits 4.3 Million Users Across Chrome and Edge
Security researchers at Koi Security have uncovered a long-running browser extension operation known as ShadyPanda, affecting over 4.3 million installs across Google Chrome and Microsoft Edge.
The campaign operated in four phases beginning in 2018. Many extensions originally appeared legitimate, with some even gaining trust badges and large userbases before receiving malicious updates.

Key Findings
• 145 total malicious extensions were identified (20 Chrome, 125 Edge).
• Early activity (2023) involved affiliate fraud by injecting tracking codes into eBay,Booking.com, and Amazon links.
• Search hijacking (2024) redirected queries throughtrovi.comwhile exfiltrating cookies and search data.
• Five extensions were later updated with a full backdoor, checkingapi.extensionplay[.]comhourly to download and execute arbitrary JavaScript with full browser API access.
• Stolen data included browsing history, search queries, cookies, fingerprinting data, keystrokes, and mouse clicks.
• Data was sent to multiple servers, includingapi.cleanmasters[.]storeand 17 domains in China.
• One extension, Clean Master, was previously featured and verified by Google before being weaponized.
• WeTab 新标签页 (3 million installs) and Infinity New Tab (Pro) (650k installs) remain live on the Microsoft Edge Add-ons store at the time of reporting.Impact
The malicious updates allowed:
• Remote code execution through hourly payload retrieval
• Browser-level surveillance
• Search hijacking and manipulation
• Potential credential theft via adversary-in-the-middle techniquesRecommendations
Users who installed any affected extensions should:
- Remove them immediately
- Reset all account passwords
- Monitor accounts for unusual activity
Koi Security notes that the abuse of the browser auto-update pipeline allowed attackers to weaponize trusted extensions without user interaction. Google has removed the known malicious Chrome extensions; Microsoft has been notified but some listings remain active.
Sources:
-
Record 29.7 Tbps DDoS Attack Linked to AISURU Botnet with up to 4 Million Infected Hosts

Cloudflare on Wednesday said it detected and mitigated the largest ever distributed denial-of-service (DDoS) attack that measured at 29.7 terabits per second (Tbps).The activity, the web infrastructure and security company said, originated from a DDoS botnet-for-hire known as AISURU, which has been linked to a number of hyper-volumetric DDoS attacks over the past year. The attack lasted for 69 seconds. It did not disclose the target of the attack.
The botnet has prominently targeted telecommunication providers, gaming companies, hosting providers, and financial services. Also tackled by Cloudflare was a 14.1 Bpps DDoS attack from the same botnet. AISURU is believed to be powered by a massive network comprising an estimated 1-4 million infected hosts worldwide.
...
As many as 36.2 million DDoS attacks were thwarted in 2025, of which 1,304 were network-layer attacks exceeding 1 Tbps, up from 717 in Q1 2025 and 846 in Q2 2025. Some of the other notable trends observed in Q3 2025 are listed below --
The number of DDoS attacks that exceeded 100 million packets per second (Mpps) increased by 189% QoQ.
-
Most attacks, 71% of HTTP DDoS and 89% of network layer, end in under 10 minutes.
-
Seven out of the 10 top sources of DDoS are locations within Asia, including Indonesia, Thailand, Bangladesh, Vietnam, India, Hong Kong, and Singapore. The other three sources are Ecuador, Russia, and Ukraine.
-
DDoS attacks against the mining, minerals, and metals industry surged, making it the 49th most attacked sector globally.
-
The automotive industry saw the largest increase in DDoS attacks, placing it as the sixth most attacked sector globally.
-
DDoS attack traffic against artificial intelligence (AI) companies spiked by 347% in September 2025
-
Information technology, telecommunications, gambling, gaming, and internet services topped the list of most attacked sectors.
-
China, Turkey, Germany, Brazil, the U.S., Russia, Vietnam, Canada, South Korea, and the Philippines were the most attacked countries.
-
Nearly 70% of HTTP DDoS attacks originated from known botnets.
Source:
-
-
Critical flaw in WordPress add-on for Elementor exploited in attacks

Attackers are exploiting a critical-severity privilege escalation vulnerability (CVE-2025–8489) in the King Addons for Elementor plugin for WordPress, which lets them obtain administrative permissions during the registration process.The threat activity started on October 31, just a day after the issue was publicly disclosed. So far, the Wordfence security scanner from Defiant, a company that provides security services for WordPress websites, has blocked more than 48,400 exploit attempts.
King Addons is a third-party add-on for Elementor, a popular visual page builder plugin for WordPress sites. It is used on roughly 10,000 websites, providing additional widgets, templates, and features.
CVE-2025–8489, discovered by researcher Peter Thaleikis, is a flaw in the plugin’s registration handler that allows anyone signing up to specify their user role on the website, including the administrator role, without enforcing any restrictions.
According to observations from Wordfence, attackers send a crafted ‘admin-ajax.php’ request specifying ‘user_role=administrator,’ to create rogue admin accounts on targeted sites.
The researchers noticed a peak in the exploitation activity between November 9 and 10, with two IP addresses being the most active: 45.61.157.120 (28,900 attempts) and 2602:fa59:3:424::1 (16,900 attempts).Wordfence provides a more extensive list of offensive IP addresses and recommends that website administrators look for them in the log files. The presence of new administrator accounts is also a clear sign of compromise.
Website owners are advised to upgrade to version 51.1.35 of King Addons, which addresses CVE-2025–8489, released on September 25.
Wordfence researchers are also warning of another critical vulnerability in the Advanced Custom Fields: Extended plugin, active on more than 100,000 WordPress websites, which can be exploited by an unauthenticated attacker to execute code remotely.
The flaw affects versions 0.9.0.5 through 0.9.1.1 of the plugin and is currently tracked as CVE-2025-13486. It was discovered and reported responsibly by Marcin Dudek, the head of the national computer emergency response team (CERT) in Poland.
The vulnerability is "due to the function accepting user input and then passing that through call_user_func_array(),” Wordfence explains.
“This makes it possible for unauthenticated attackers to execute arbitrary code on the server, which can be leveraged to inject backdoors or create new administrative user accounts.”
The security issue was reported on November 18, and the plugin vendor addressed it in version 0.9.2 of Advanced Custom Fields: Extended, released a day after receiving the vulnerability report.
Given that the flaw can be leveraged without authentication only through a crafted request, the public disclosure of technical details is likely to generate malicious activity.
Website owners are advised to move to the latest version as soon as possible or disable the plugin on their sites.
-
Massive 16 Terabyte Database With 4.3 Billion-Records Leaked
A massive unprotected MongoDB instance containing over 4.3 billion records and totaling roughly 16 TB of data was discovered exposed online. The dataset included highly structured professional and corporate intelligence data, much of it clearly scraped from LinkedIn and enriched through lead-generation pipelines. The exposed collections contained PII such as full names, emails, phone numbers, LinkedIn profile URLs, employment history, skills, education, location data, and even photographs.
The leak, uncovered by cybersecurity researcher Bob Diachenko on November 23rd, 2025, consisted of nine major collections. Three of those - profiles, unique_profiles, and people - alone contained nearly 2 billion individual PII-rich entries. The dataset also referenced an “Apollo ID”, suggesting potential linkage to Apollo-style sales intelligence ecosystems or enrichment tools.
The structured nature of the data, combined with its massive scale, makes it extremely attractive to threat actors. Attackers could weaponize the PII for targeted phishing, CEO fraud, corporate reconnaissance, credential stuffing, and AI-assisted social engineering at unprecedented volume. With up-to-date professional metadata, malicious operators can automatically craft convincing spear-phishing messages or build large internal mapping structures of corporate roles and contacts.
The exposed database was secured on November 25th, the day after responsible disclosure, but it is unknown how long it had been publicly accessible. Given the size and organization of the dataset, researchers warn that malicious parties may have already accessed it.
This exposure adds to a growing trend of massive, scraping-driven data leaks, which now routinely exceed billions of records and blur the line between legally scraped data and high-risk breach material.
Sources:
-
SoundCloud Confirms Data Breach
SoundCloud has confirmed a security breach after users reported widespread outages and 403 errors when accessing the platform through VPNs. According to the company, the issues were caused by its incident response after detecting unauthorized access to an ancillary service dashboard.
SoundCloud stated that a threat actor accessed a limited database containing user email addresses and information already visible on public profiles. The company said no passwords, financial data, or other sensitive information were exposed.
Sources cited by BleepingComputer estimate the breach impacts roughly 20 percent of SoundCloud’s user base, potentially affecting around 28 million accounts. SoundCloud says all unauthorized access has been blocked and that there is no ongoing risk.
As part of its response, SoundCloud implemented security configuration changes that disrupted VPN connectivity. The company has not provided a timeline for restoring full VPN access. It also reported experiencing denial-of-service attacks following the incident, briefly affecting site availability.
While SoundCloud has not named the attackers, BleepingComputer reports that the ShinyHunters extortion group is allegedly behind the breach and is attempting to extort the company after stealing user data.
Sources:
-
2025 Cybersecurity Predictions vs Reality
This article reviews 90+ predictions from 36 cybersecurity experts and compares them to what actually occurred in 2025. The main finding: most predictions were accurate, especially those focused on AI amplifying existing threats rather than creating new ones.
Key Outcomes
- AI Amplified Existing Attacks
- AI was widely adopted by attackers to scale and automate known techniques.
- Observed uses included AI-assisted phishing, automated recon, and malware with runtime code mutation to evade detection.
- Underground markets began selling configurable AI-powered attack tools.
- AI reduced the skill barrier and increased attack speed and volume.
Result: Prediction confirmed. AI increased efficiency, not novelty.
- SaaS, Cloud, and Identity Became the Main Attack Surface
- SaaS misconfigurations, excessive permissions, insecure APIs, and third-party integrations were major breach drivers.
- Identity and access failures eclipsed traditional perimeter security issues.
- Large-scale cloud outages were often caused by configuration errors.
Result: Prediction confirmed. Identity and SaaS security became critical weaknesses.
- Ransomware Fragmented Further
- Law enforcement pressure led to more, smaller ransomware groups rather than fewer.
- 30 to 40 percent increase in active ransomware operators.
- Affiliates increasingly moved between groups, complicating attribution.
Result: Prediction confirmed. Ransomware evolved into a fragmented ecosystem.
- Supply Chain Attacks Increased
- Enterprises were compromised through trusted vendors and enterprise software.
- SaaS and third-party providers became common initial access vectors.
Result: Prediction confirmed. Vendor risk became a primary concern.
- Data Became the Core Security Asset
- Data protection and governance overtook infrastructure as the main security focus.
- Large credential leaks and AI training on sensitive data accelerated this shift.
- Data visibility and classification became prerequisites for AI use.
Result: Prediction confirmed. Data security underpins most modern risks.
- Regulation Added Complexity Without Reducing Attacks
- Increased compliance and reporting requirements did not deter attackers.
- Regulatory burden primarily impacted internal operations, not threat actors.
Result: Prediction confirmed. Regulation did not materially change the threat landscape.
Bottom Line
2025 validated long-standing warnings rather than introducing new threat classes.
The biggest risks were known problems amplified by AI, automation, and scale, not futuristic scenarios.
Source:
-
Verizon Nationwide Outage (Jan. 14, 2026)
Verizon Communications experienced a major nationwide wireless network outage beginning around midday on January 14, 2026, disrupting voice, text, and mobile data services across the United States for approximately ten hours. Customers reported their phones showing “SOS” or “SOS-only” status in place of normal signal bars, indicating loss of cellular connectivity.
Outage monitoring sites such as DownDetector logged hundreds of thousands of reports at the peak, with impacts reported coast-to-coast in major metropolitan areas including New York City, Chicago, Boston, Atlanta, Dallas, and others. Some local officials warned that emergency calls (911) for Verizon users could be unreliable during the disruption, recommending alternatives such as landlines or other carriers where possible.
Verizon acknowledged the outage via social media and later confirmed that service was restored late Wednesday night. The company apologized for the interruption and stated it will issue account credits to affected customers. Verizon did not immediately disclose a specific technical cause, though internal reviews are expected.
The Federal Communications Commission (FCC) indicated it would review the outage’s impact on network reliability and public safety communications.
Sources:
-
Atomic Wallet - Where Did My XMR Go?
Many Atomic Wallet users recently logged in to find their Monero (XMR) balances missing or incorrect, causing understandable concern.
According to Atomic Wallet support, this is a display and synchronization issue specific to Monero, not a loss of funds. Atomic states that all XMR remains safe on-chain and that their development team is working on a fix. Once synchronization is corrected, balances and transaction history should update normally.

Users can independently confirm their funds by restoring their XMR wallet in another trusted Monero wallet using their existing keys or seed phrase. Multiple users report that their full balances appear correctly when checked outside Atomic, confirming the issue is isolated to Atomic’s wallet interface.
Given Atomic Wallet’s 2023 security breach, users are understandably cautious. While this situation appears unrelated and no theft has been reported, verifying balances independently is recommended.
Summary
- Issue affects XMR balance display in Atomic Wallet
- Funds are still on-chain and under user control
- Atomic says a fix is in progress
- Users can verify funds using another Monero wallet
- Use caution, verify independently, and never share your private keys or seed phrase with anyone

Sources:
- @cyclone (independent verification with Atomic)
- https://x.com/AtomicWallet/status/2011796132112826643
-

haahahahahah
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login

