Infosec News
-
NVIDIA RTX 50-Series GPUs Face Thermal Challenges: Hotspots and Melting Thermal Gel Raise Reliability Concerns
Recent analyses have highlighted significant thermal issues affecting NVIDIA's RTX 50-series GPUs, raising concerns for users engaged in compute-intensive GPU tasks.
-
Power Delivery Hotspots Identified by Igor's Lab:
Investigations by Igor's Lab have uncovered that RTX 50-series GPUs, including models like the RTX 5060 Ti, 5070, and 5080, exhibit thermal hotspots in their power delivery systems. These hotspots, resulting from densely packed components such as FETs, coils, and drivers on compact PCBs, have been recorded at temperatures exceeding 100°C—surpassing the GPU core temperatures. Such elevated temperatures can accelerate material degradation, potentially compromising the longevity of the graphics cards. Mitigation efforts, such as applying thermal pads or putty to the affected areas, have shown temperature reductions of up to 12°C, indicating that design adjustments could alleviate these thermal concerns -
Gigabyte's Thermal Gel Leakage Issues:
Separately, users have reported instances of thermal gel leakage in Gigabyte's RTX 50-series GPUs, notably in models like the RTX 5080. The issue appears more prevalent in vertically mounted GPUs, where gravity may exacerbate the leakage of the server-grade thermal conductive gel used in place of traditional thermal pads. While the gel is non-conductive and generally safe, its unintended migration can affect the GPU's thermal performance and aesthetics. Gigabyte has acknowledged the problem and is reportedly working on a customer service policy to address affected units
These findings underscore the importance of thermal management in high-performance GPUs and suggest that both design refinements and user awareness are crucial to ensure the reliability and longevity of RTX 50-series graphics cards.
-
-
Marks & Spencer Cyberattack Disrupts Services Across UK Stores
British retailer Marks & Spencer (M&S) is grappling with a cyberattack that began over Easter weekend, disrupting online order deliveries, click-and-collect services, and contactless payments across the UK. The company has moved some operations offline to protect staff and customers, while shares fell 3% over five days. Despite the disruption, M&S confirmed no customer data has been compromised and is working with cybersecurity experts and the UK's National Cyber Security Center. The Information Commissioner’s Office has been notified. CEO Stuart Machin apologized and assured continued efforts to resolve the incident.
M&S Press Release:
https://corporate.marksandspencer.com/media/press-releases/cyber-incident-further-update -
SAP NetWeaver Zero-Day (CVE-2025-31324) Under Active Exploitation — Emergency Patch Issued
SAP has issued an out-of-band emergency fix for a critical zero-day RCE vulnerability (CVE-2025-31324, CVSS 10.0) affecting the NetWeaver Visual Composer. The flaw lies in the /developmentserver/metadatauploader endpoint, allowing unauthenticated attackers to upload malicious files and execute arbitrary commands — leading to full system compromise.
ReliaQuest and watchTowr confirm active in-the-wild exploitation, with attackers deploying JSP webshells, Brute Ratel payloads, and advanced evasion techniques like Heaven's Gate and MSBuild injection. Even fully patched systems prior to this emergency release remain vulnerable.
SAP has not yet publicly acknowledged the active exploitation. The vulnerability affects Visual Composer Framework 7.50 and is not covered in the April 8th patch cycle. Two additional critical bugs were also addressed in this emergency update (CVE-2025-27429 and CVE-2025-31330).
Immediate Actions:
- Apply the emergency SAP patch immediately
- Restrict or disable access to the vulnerable endpoint if patching isn't feasible
- Scan servlet paths for unauthorized uploads
- Conduct full environment scans for persistence mechanisms
- Stay alert — widespread exploitation is likely to follow
SAP Security Patch Info:
https://support.sap.com/en/my-support/knowledge-base/security-notes-news/april-2025.html -
Kali Linux Rolls Out New Archive Signing Key After Repository Access Loss
In a recent announcement, the Kali Linux team revealed that users will soon encounter apt update failures due to a missing GPG signing key.
Missing key 827C8569F2518CC677FECA1AED65462EC8D5E4C5, which is needed to verify signature.The failure stems from the team losing access to their previous signing key, prompting the rollout of a new one. Users must manually update their systems by downloading the new key using either wget or curl:
sudo wget https://archive.kali.org/archive-keyring.gpg -O /usr/share/keyrings/kali-archive-keyring.gpgor
sudo curl https://archive.kali.org/archive-keyring.gpg -o /usr/share/keyrings/kali-archive-keyring.gpgVerifying the SHA1 checksum is recommended to ensure file integrity.
sha1sum /usr/share/keyrings/kali-archive-keyring.gpg 603374c107a90a69d983dbcb4d31e0d6eedfc325 /usr/share/keyrings/kali-archive-keyring.gpgThe new keyring includes both the old and new keys, allowing a smooth transition without indicating any key compromise.
Additionally, all Kali images (ISO, NetHunter, VM, Cloud, Docker, WSL) have been refreshed (version 2025.1c and weekly builds from 2025-W17) to include the new key. Fresh installs are an option for users preferring a clean setup.
The team reassures that there was no security compromise—only a loss of key access—and signatures of the new key are publicly verifiable via the Ubuntu keyserver.
Users are advised to update immediately to restore normal package management and avoid repository signature errors.
Source:
https://www.kali.org/blog/new-kali-archive-signing-key/ -
How to use Hashcat on GeForce RTX 50 series video cards. How to install the driver for GeForce RTX 5060, 5070, 5080, 5090 in Linux
In recent years, Linux preparation for brute-force hashes using the Hashcat utility has been quite well-tested:installing Hashcat installing proprietary drivers for a video card installing CUDABut if you repeat the installation commands that have already been tested for years, then they will not work for the new GeForce RTX 5060, 5070, 5080, 5090 graphic cards. This article will provide updated commands that will allow you to configure Linux to work effectively with Hashcat, including using GeForce RTX 50 series video cards.
So, the changes are that now the NVIDIA driver for Linux is released in two flavors:
NVIDIA Proprietary (this is the same flavor that we have been installing for the past few years) NVIDIA Open (this is a relatively new flavor)In general, the difference between these driver flavors is not very significant and did not particularly affect Hashcat users. This was the case before the release of the GeForce RTX 50 series. Starting with the release of the GeForce RTX 50 series video cards (since 2025), the difference between the driver versions has become significant – only NVIDIA Open now supports the GeForce RTX 50 series. This means that when installing the driver, you need to select NVIDIA Open – fortunately, this does not cause any difficulties, since it is present in the standard repositories of many Linux distributions.
What is NVIDIA Open and should Linux users switch to the new driver:https://suay.site/?p=5090
Source: https://miloserdov.org/?p=8299 -
SentinelOne Under Siege: Chinese Espionage, North Korean Infiltration, and Ransomware Threats
In April 2025, SentinelOne revealed it has been the target of a broad spectrum of cyber threats, including Chinese state-sponsored espionage, North Korean job applicant infiltration, and ransomware operations. A China-nexus APT group dubbed PurpleHaze, likely linked to APT15, targeted SentinelOne infrastructure and clients using ShadowPad malware obfuscated via a compiler called ScatterBrain, and leveraged GoReShell, a Go-based reverse SSH backdoor. These intrusions exploited an N-day vulnerability in Check Point devices and targeted over 70 global organizations.
Meanwhile, North Korea-aligned actors submitted over 1,000 fake job applications to SentinelOne, attempting to penetrate intelligence teams. Separately, Russian ransomware groups—most notably Nitrogen—used advanced impersonation tactics to acquire legitimate EDR licenses from resellers with poor KYC controls. These attackers participate in a growing underground economy offering “EDR Testing-as-a-Service” to improve malware evasion against top-tier endpoint defenses.
SentinelOne emphasized that attacks on security vendors are both real and rising, and that openly acknowledging these threats is vital for industry-wide defense improvements.
Sources:
https://thehackernews.com/2025/04/sentinelone-uncovers-chinese-espionage.htmlhttps://cyberscoop.com/cybersecurity-vendors-are-under-attack-sentinelone-says/
-
UK Retailer Co-op Disables IT Systems Following Attempted Cyber Intrusion
British supermarket chain Co-op temporarily shut down parts of its IT infrastructure after detecting unauthorized access attempts, disrupting back office and call center operations. While stores and essential services remain unaffected, the company has not confirmed if the intrusion was successful. The incident follows a recent ransomware attack on Marks & Spencer by the "Scattered Spider" group, raising concerns about escalating threats to UK retail infrastructure.
-
NoName057(16) Targets Dutch Infrastructure in Ongoing DDoS Attacks
Hacktivist group NoName057(16) has launched a sustained wave of distributed denial of service (DDoS) attacks against Dutch public and private organizations, according to the Dutch National Cyber Security Center (NCSC). The attacks have disrupted access to online services across multiple provinces and municipalities, including Groningen, Noord-Holland, and Tilburg.
The group, active since early 2022, uses a crowdsourced platform dubbed "DDoSIA" to coordinate and incentivize global participants in DDoS operations. Despite arrests in Spain last year, the core leadership remains active, and their operations show no sign of stopping. Dutch authorities confirm no data breaches have occurred, but public-facing systems continue to face service outages.
This attack reinforces the shift from ransomware to geopolitically motivated DDoS attacks.
-
Microsoft to Retire Authenticator Password Autofill by August 2025, Shifting Users to Edge
Microsoft has announced the phased deprecation of the
password autofill featurein its Authenticator app, aiming to consolidate credential management within its Edge browser. The Authenticator app will still support MFA and Passkeys, however. The transition will occur over several months:June 2025: Users will no longer be able to save new passwords in Authenticator.July 2025: Autofill functionality will cease, and stored payment information will be deleted.August 2025: Saved passwords and unsaved generated passwords will become inaccessible within Authenticator.
To maintain access to their saved credentials, users must switch to Microsoft Edge, where passwords and addresses synced to their Microsoft account will remain available. Edge must also be set as the default autofill provider on mobile devices to utilize this functionality. Alternatively, users can export their passwords from Authenticator before August 1, 2025, and import them into another password manager. Payment information, however, must be manually re-entered into the new platform as it cannot be exported from Authenticator.
Microsoft Announcement:
https://support.microsoft.com/en-us/account-billing/changes-to-microsoft-authenticator-autofill-09fd75df-dc04-4477-9619-811510805ab6 -
Magento Supply Chain Attack Unleashes Six-Year Dormant Backdoors, Hits Up to 1,000 E-Stores
A sophisticated supply chain attack has compromised between 500 and 1,000 Magento-powered e-commerce sites through 21 maliciously backdoored third-party extensions. Discovered by security firm Sansec, the breach involves vendors Tigren, Meetanshi, and MGS, with some backdoors embedded as far back as 2019 but only activated in April 2025. The attackers used a covert PHP backdoor hidden in license verification files, enabling remote code execution, webshell deployment, and full administrative control.
The malicious code validates specially crafted HTTP requests using hardcoded keys before executing administrative functions, including dynamic PHP code injection via uploaded "license" files. Notably, past versions of this backdoor lacked authentication, highlighting an evolving threat. One victim is reportedly a $40 billion multinational.
While Meetanshi acknowledged a server breach, Tigren denied any compromise and continues distributing affected code. MGS has remained unresponsive. BleepingComputer independently verified the backdoor in at least one extension (MGS StoreLocator). Users are urged to scan their systems for indicators of compromise and revert to known-clean backups. Sansec has pledged further analysis as investigations continue.
-
19 Billion Leaked Credentials Reveal Dangerous Reuse Patterns
A comprehensive study by Cybernews has uncovered that over 19 billion passwords, exposed through more than 200 data breaches between April 2024 and April 2025, are circulating online. Alarmingly, only 6% of these passwords are unique, with the remaining 94% being reused across multiple accounts, significantly increasing vulnerability to cyberattacks .
The analysis highlights that 42% of the passwords are between 8 to 10 characters long, and 27% consist solely of lowercase letters and digits, making them susceptible to brute-force and dictionary attacks. Commonly used passwords include "123456" (338 million instances), "password" (56 million), and "admin" (53 million). Personal names, such as "Ana," appear in 178.8 million passwords, while terms like "love," "sun," and "freedom" are also prevalent.

Cybersecurity experts emphasize the risks associated with weak and reused passwords, noting that such practices can lead to credential-stuffing attacks, where attackers use leaked credentials to gain unauthorized access to multiple accounts. They recommend using strong, unique passwords of at least 12 characters, incorporating a mix of uppercase and lowercase letters, numbers, and special symbols. Additionally, enabling multi-factor authentication (MFA) and utilizing password managers can significantly enhance account security.
This study underscores the critical need for improved password hygiene and the adoption of more secure authentication methods to protect personal and organizational data in an increasingly digital world.
Source:
https://cybernews.com/security/password-leak-study-unveils-2025-trends-reused-and-lazy/ -
LockBit Ransomware Group Breached: Internal Data and Victim Chats Leaked
The notorious LockBit ransomware gang has suffered a significant breach, with its dark web infrastructure defaced and internal data leaked. A message reading "Don't do crime CRIME IS BAD xoxo from Prague" appeared on one of LockBit's dark web sites, accompanied by a link to a cache of leaked data, including chat logs between the hackers and their victims.
Cybersecurity experts from Analyst1 and Rapid7 have reviewed the leaked materials and consider them authentic. The data reveals LockBit's indiscriminate targeting, including small businesses, for ransom. Analysts suggest this breach could significantly impact the group's operations and credibility.
This incident follows previous disruptions, including a major international law enforcement operation in February 2024 that seized some of LockBit's infrastructure . Despite past resilience, this latest breach represents a substantial blow to the group's stature.
https://www.computing.co.uk/news/2025/security/lockbit-ransomware-gang-hacked-again
-
Fake AI Tools Used to Spread Noodlophile Malware, Targeting 62,000+ via Facebook Lures
Cybercriminals are exploiting the popularity of AI tools by creating fake AI-powered platforms to distribute a new information-stealing malware called Noodlophile. These fraudulent platforms, often advertised through seemingly legitimate Facebook groups and viral social media campaigns, have attracted over 62,000 views on a single post, indicating a significant reach.
Users are lured into these schemes by promises of AI-generated content creation services, such as videos, logos, and images. Upon uploading their content, users are prompted to download what they believe is their AI-enhanced media. Instead, they receive a malicious ZIP archive named "VideoDreamAI.zip". This archive contains a deceptive executable file, "Video Dream MachineAI.mp4.exe", which initiates the infection chain.
The executable launches a legitimate binary associated with ByteDance's video editor, CapCut, which is used to run a .NET-based loader named CapCutLoader. This loader then downloads and executes a Python payload ("srchost.exe") from a remote server. The Python binary facilitates the deployment of Noodlophile Stealer, capable of harvesting browser credentials, cryptocurrency wallet information, and other sensitive data. In some instances, the stealer is bundled with a remote access trojan like XWorm, providing attackers with deeper access to infected systems.

Investigations suggest that the developer of Noodlophile is of Vietnamese origin, with a GitHub profile claiming to be a "passionate Malware Developer from Vietnam." This campaign underscores a growing trend where threat actors leverage public interest in AI technologies to propagate malware, highlighting the need for increased vigilance when engaging with online AI tools.
Sources:
https://thehackernews.com/2025/05/fake-ai-tools-used-to-spread.html -
Spain Probes Cybersecurity Gaps in Wake of Massive Power Grid Blackout
On April 28, Spain experienced a catastrophic blackout, losing 60% of its power—roughly 15GW—in just five seconds. While the cause remains under investigation, Spain's National Cybersecurity Institute (Incibe) is now scrutinizing small and medium-sized renewable energy producers for potential cybersecurity weaknesses.
The inquiry targets decentralized renewable sources—like solar and wind farms—that rely on internet-connected systems, making them more vulnerable to remote exploits. Investigators are questioning operators on remote access capabilities, recent patches, and anomaly logs.
Despite no initial evidence of cyber intrusion at Spain’s main grid operator (Red Eléctrica), the government isn't ruling out a coordinated cyberattack. With 100,000 cyber incidents recorded in Spain last year and a €1.1B investment announced to bolster cybersecurity, the investigation reflects growing concern over the fragility of modern, decentralized infrastructure.
Security experts remain skeptical, citing the technical difficulty of executing a synchronized attack of such scale. Yet the sheer impact has prompted a deeper look into firmware-level risks, IoT vectors, and underregulated installations—especially those below 1MW that fall outside real-time monitoring capabilities.
Sources:
https://www.ft.com/content/a24e6e3c-cf9f-4093-833b-6e7492e7e7f0 -
Exodus to Drop Monero (XMR) Support by August 2025 — What You Need to Know
Exodus Wallet, a popular self-custody cryptocurrency wallet, has officially announced it will discontinue support for Monero (XMR) on August 10, 2025. After this deadline, users will no longer be able to send, receive, or view XMR balances through Exodus.
What You Should Do:Before August 10, 2025:- You can send your XMR to another wallet or swap it for another asset within Exodus.
- Exodus Swap remains available for converting XMR to other coins until the cutoff date.
After August 10, 2025:- You won’t be able to interact with XMR in Exodus in any form.
- However, using your 25-word mnemonic, you can recover your Monero in any compatible wallet.
-
Troy Hunt's Mailchimp List Breached via Phishing Attack in March 2025While old news, Troy Hunt, the security researcher behind Have I Been Pwned, disclosed that his Mailchimp account was compromised on March 25, 2025, via a phishing attack. The attacker tricked him into entering credentials on a fake Mailchimp SSO site, then swiftly replayed both his username and OTP to the real Mailchimp login endpoint. Within moments, the intruder exported his full mailing list—over 16,000 records—before access could be revoked.
Cloudflare quickly blocked the phishing site, but not before Troy's credentials were compromised:
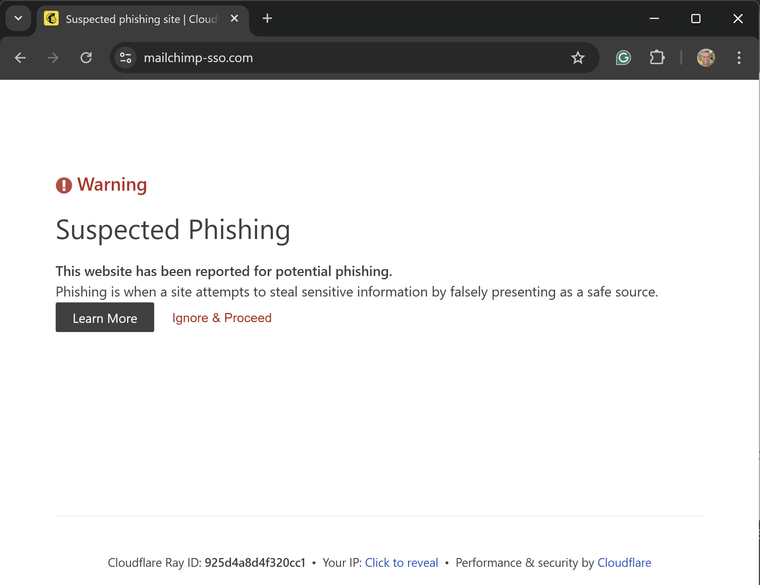
The stolen data included subscriber email addresses, subscription preferences, and metadata such as IP addresses, derived lat/long, time zones, and timestamps. Alarmingly, it also contained over 7,500 unsubscribed addresses, prompting questions about Mailchimp’s data retention policies and GDPR compliance.
The phishing email was sent to a unique Mailchimp-specific address, suggesting the attacker may have sourced their target list from a previous Mailchimp-related breach, possibly the 2022 crypto-targeted incident. Other organizations have reported receiving identical phishing messages, further supporting this theory.
Troy has since rotated credentials, removed the API key, and had his account access restored. The compromised data has already been loaded into Have I Been Pwned, and affected users have been notified.
https://haveibeenpwned.com/PwnedWebsites#TroyHuntMailchimpList
https://www.troyhunt.com/a-sneaky-phish-just-grabbed-my-mailchimp-mailing-list/
-
FBI Warns Senior U.S. Officials of AI Voice Cloning and Smishing Campaigns
The FBI has issued an urgent alert about a wave of sophisticated social engineering attacks where threat actors impersonate high-ranking U.S. officials using AI-generated voice cloning and malicious text messages (smishing).
These messages have targeted both current and former government personnel as well as their contacts, aiming to build trust and eventually extract access to sensitive accounts or information. The tactics mirror spear-phishing, but leverage newer AI tools to enhance credibility.
Notably:
- AI voice cloning usage surged 442% in late 2024, making vishing (voice phishing) a potent new threat.
- Publicly available speeches or interviews are often enough to train a voice model with highly realistic results.
- These methods are now part of campaigns by state-linked groups and ransomware actors like Scattered Spider and AlphV.
- Mandiant reports successful red-team use of cloned voices to bypass security teams and deploy malware.
This trend reflects a broader rise in AI-powered attack vectors and underscores the need for multi-factor authentication, strict access controls, and ongoing employee training in recognizing manipulative communications.
Sources:
https://www.ic3.gov/PSA/2025/PSA250515https://www.cybersecuritydive.com/news/fbi-us-officials-impersonated-text-ai-voice/748334/
-
Inside Job - Coinbase Faces $400M Fallout After Insider Data Breach and $20M Ransom Demand
On May 15, 2025, Coinbase disclosed a significant data breach involving bribed overseas customer support agents who leaked sensitive customer information. The breach affected approximately 1% of users, compromising data such as names, contact details, masked Social Security numbers, bank account identifiers, government-issued ID images, and transaction histories.
The attackers demanded a $20 million ransom, which Coinbase refused to pay. Instead, the company established a $20 million reward fund for information leading to the arrest and conviction of the perpetrators. The breach is projected to cost Coinbase between $180 million and $400 million, encompassing remediation efforts and customer reimbursements.
In response, Coinbase has terminated the involved contractors, enhanced fraud monitoring, and is cooperating with U.S. and international law enforcement agencies. The U.S. Department of Justice has initiated an investigation into the incident.
The breach has also led to multiple lawsuits alleging inadequate security measures by Coinbase. Despite the breach, Coinbase confirmed that no passwords, private keys, or customer funds were compromised.
Sources:
https://cybersecuritynews.com/coinbase-hacked
https://www.businessinsider.com/coinbase-hack-crypto-scam-fraud-coin-sp500-listing-cryptocurrency-exchange-2025-5
https://www.thetimes.com/business-money/companies/article/coinbase-says-hackers-bribed-staff-in-cyberattack-9vgkbq5wh -
Critical RCE Vulnerability in Lexmark Printers (CVE-2025-1127) Threatens Networks
A critical vulnerability, CVE-2025-1127, has been identified in over 150 Lexmark printer models, including the CX, MX, XC, and CS series. This flaw allows remote attackers to execute arbitrary code on unpatched devices by exploiting a combination of path traversal (CWE-22) and race condition (CWE-362) vulnerabilities in the embedded web server. The vulnerability has been assigned a CVSS v3.1 score of 9.1 (Critical).
Discovered by DEVCORE researchers through Trend Micro’s Zero Day Initiative, the exploit requires network access and valid credentials. However, many devices remain vulnerable due to unchanged default admin credentials. Attackers can leverage this flaw to deploy ransomware, exfiltrate documents, or use compromised printers as entry points into corporate networks.
Affected Models:
The vulnerability impacts devices running firmware versions released before February 13, 2025. A wide range of Lexmark models are affected, including CX950, XC9525, MX953, CX961, XC9635, CS963, CX833, MS531, MX532, CS531, CX930, XC9325, CS943, MX432, CX730, CS730, MS321, M1242, B2338, MS622, MX321, MB2338, MS725, B2865, MS822, MX721, XM5365, MB2770, CS622, CS421, C2325, CX522, MC2535, CX421, MC2325, B2236, MS331, M1342, B3442, XM1342, MX331, MB3442, C3426, CS431, CS331, C3224, C2326, MC3426, CX431, XC2326, MC3426, MC3224, CX331, CX820, XC6152, CS820, C6160, CS720, C4150, CX725, XC4140, CS921, C9235, CX920, XC9225, and more.Lexmark has released patched firmware versions with “.206” or “.408” suffixes across 38 distinct product families. Administrators can verify firmware versions through the control panel’s Settings → Reports → Menu Setting Page.
Sources:
https://gbhackers.com/critical-vulnerability-in-lexmark-printers/
https://cyberpress.org/lexmark-printer-flaw/ -
AirBorne Alert: 23 Zero-Click Vulnerabilities in Apple AirPlay Expose Billions of Devices to RCE Threats
Security researchers at Oligo Security have disclosed 23 previously unknown vulnerabilities in Apple's AirPlay protocol, collectively dubbed “AirBorne.” These flaws affect Apple and third-party AirPlay-compatible devices, including smart TVs, speakers, and in-car systems like CarPlay. Critically, several of the bugs are zero-click and wormable, meaning attackers can exploit them without user interaction and potentially spread laterally across networks.
The vulnerabilities allow remote code execution (RCE) and device hijacking over the same Wi-Fi network. Attackers can silently compromise a device, execute arbitrary payloads, and even eavesdrop via smart systems, turning entertainment features into serious security liabilities.
Impacted devices range from iPhones, iPads, and MacBooks to third-party IoT devices, many of which may not receive timely security updates. Despite Apple patching the core vulnerabilities in recent OS updates, many third-party vendors remain exposed, as they rely on outdated SDKs or unsupported firmware.
Key Points:
- Zero-click, wormable RCE vulnerabilities
- Exploitable via Wi-Fi proximity, no pairing needed
- 23 CVEs affecting both Apple and OEM AirPlay implementations
- Attacks demonstrated on smart TVs, speakers, and vehicle infotainment systems
- Major concern for unpatched third-party devices still using vulnerable AirPlay stacks
- Researchers urge users to disable AirPlay on untrusted networks
- Apple users should update iOS/macOS immediately
- Devs/OEMs must audit third-party SDKs and deploy firmware updates ASAP
Sources:
- https://www.kaspersky.com/blog/airborne-wormable-zero-click-vulnerability-in-apple-airplay/53443/
- https://timesofindia.indiatimes.com/technology/tech-news/apple-airplay-may-have-major-security-flaws-that-can-allow-hackers-to-hijack-devices-researchers-claim/articleshow/121346229.cms
- https://www.ndtv.com/world-news/apple-warns-iphone-users-advises-them-to-urgently-turn-off-this-feature-8464822
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login


