Cracking metamask hash
-
Please delete the upper message ill rather attach a txt file, accidentaly deleted the post.
It would be excellent if you manage to elaborate how to transform this into a crackable 26600 hash format OR manage to get it working with 26620 kernel mode. Password is catanddog if you want to go with a shorter wordlist.
-
Please delete the upper message ill rather attach a txt file, accidentaly deleted the post.
It would be excellent if you manage to elaborate how to transform this into a crackable 26600 hash format OR manage to get it working with 26620 kernel mode. Password is catanddog if you want to go with a shorter wordlist.
@dbgdbg Deleted as requested. The issue was you need to comment out any lines that contain markdown code.
example:commented out lineThe tool already gave you a crackable hash under
hashcat -m 26620 hash (NEW format):$metamask$600000$xsq1OyKYinxYyiOUWyTVT820oedGQy+smC7EufhhEEg=$UuT70j+fJnU2tLU4bxZ35g==$I/DCva85GqSyhzTxlYLqjhacvnroBf2IAdFpanTaAd062T+T6UjivtLSyiawhbbe1un5UDDqasyVCtJwf/y32yaZ/zx67m3qz//s9wvYymXWicFWL81gLh3Tsqi/39v3E09ECpBcEezim8KmrdUB+zNwxjfufdzQ4RfrwOxY7FvD5wML7dI6G9hi18vWwbgz+SyJnjNA880VgKh/eV5YRjiEMUtGrcMfR/EXoPmvTpTsC4F3fUAPOtl1WW0TVqH1tdWLDwqH7g0F/Mo4TOOK7Ranfpm1D9LAg/UlWTLsh6a6f6TAUwBIqFvnZG1JEdB7m12brS1HJZh+y+wFWEzERTuvspbEBcOG2uqZAWiJG6HWQvua5OhhoawxSBff1l/kYRAdmBwT3Vt7Hk9HX4gIuebyKS+V7fk5QprNpw87eiiDcgM7fzhLwIzvt6cCDPZ2yLF8p/ycvDMwIQZf1mezYJbSHS1L7NYbxY5FJ/na2QDaojJr0FDJ0FKDX9UBB45T/MWZqeITXqW8vo3bQkuKeIG3B02Y4W3oRKw7EzfHCodVaZXnRL+Czem7sOIl9TFO4N250rztB2DRgkfsZh+OxCLjc02np/66OdJf5R9njFVHrJ4cX1ENCbn4miqeF40dS4hMqhLBNSTA+gKkd0aIZVvSL/MoaI9lyJQz4Mcgfxen6m52MDJu7cJajxXoiC1YOI+vhy1yj4qIaxHCDxhCQ380tcBxwJaxskqH7s/uokhQXs1eIYVbpX/ygDOh4e8ykSJu6e+HWki5WwBRW21O6V4d+jJDLr5mFgBHRdFGBVfaFQR/kLUedno7tXD6a+AGssGitQRMn7aQAbkOvdVwiMFmwpjvNXqxpdmK82oBMRWCOe9A03HpFrXTVkamu0OBZAbh+9CMJDcgPjcrrqwVQ8FkUwh3JrceiAkOzfFPSDswZJMItaj7o8i/gnaeaFXYn4Pcb/Wdyk4RsUocsOLEKekzPjZ/pzNxHpY++wmYXuODoL3UIqgZ8mq8GNWgMPFu/DSLeGHkY7XADJOPDz/befJo6Y0W4/yk84jFCaf2KuoH5BGufKYaS6KV2dtIbTaDTORfty0IkX/xEJVhFqA8W4421SvsE8bzHdxF7W6/UBqOeMJY0mBQXeyMoCxRWNQwhQ3H4TIXP0XTXIhc0kOZXlZPWhdMJS3xstGUR/2lGAWOWpn0g+wbksEaOVXFBHlMrXXfO1GrxWiklc7MnhJMmRZwBJR7EAPu/mY+jInmROycRjTpOPn481ueDUc1gIKPbk82RpEq6NH1pOohwHCjc7EJtgOUDePL3duuLNJYnvs7pDkkOrIO2oKsMW+XMTqZoTbmTM0a+ssZ0129LN73ar5vk2LrMlsHZeUUb8s7GuQjolZ8e3k7/y+jKdUjVKCgnUScH4LqhubdDQxCgxoHvsukNUrAzeb0EPR7Zbq0SeZxnJ4wd25ME+7QmWGeIgwPEMI0uWLbsQwLeJ63iv1XHmtkZnhcepZlDOGmTGCPnAkQyYReDFAGng3SEXA3tRY3uLNvfh7tExSknqfjpBKM3KARdh142grxbKT8RuHfC4e4WVkRZxWl/7QbFRl9BDi7rEMSeZCERojLFV8lSV8E6LmOuO1+r+NwVgCoDnE23XwPEXsqZOd7F4U3jtEIheXGe31i4z9wt/SisVKQuFR5A6wiVfENLyUimXq06YDY009TNEtXBrs+osTN7C/ECEXqzPxoatM3pDX8GE88RPgZCgPZGm3IyglCPBE9ptiyVss2acSF/X74V5ekujyuxopt32zh+SqvwuvhNOdxQZ99N0uq+1AfpuZOZ9bH6PcIPI9qR3hDoKXohWTs+moxz3m9taQ9XgX6qxab8D+i+qw3tVBnJi88FeLdS/OlWQJg5VE9juC5y5RpcoYR39LPOzRFEKK4K9LLAuHFpKuHZGfzIXKxeG4wBStVy7PvFLcqMCtsfJeYI+KPIuQvh1qydKHC5y7FkJNBTs0HIhskZ/RBRjib78Bkf010XUMCPcV6lxaD6qSu8Ko0caE6By4lNaSy0UaPVSIxjWZ6EZgjxVy3CYlR6BWIvsmX4djJQOgQx6+eT7ceV8bT6tDq7LhC46Z0nH+oUws/O+QApNAHSdZtFBzOd+xKqrX7p0ebXgrRaBH1KSoweFL6euRgpF/qVefN8JcKYodb42CYrmlWJZHk8X0ypGqPHZYFpDUkR3HaVxjE/2tg6tOTlh+RhKqeZHjYYKVVvtaFTjyelh/VqUkcmlYKhPOP1YOlAwFhYIFFpj094HY9jXWVsSoOlJG51279oHLGGusxQwhPP1FkzR73eYsr0ZjoAGrx2q1ztx7fynj+6AKdwmJf16x7+W17/uB6d9nESGAhlpe8SpZNovVVACkrFg3pn/yy1C8hJCcMmU1dVP5BjX8pn97LBJeWaPkgwG0a6T1qqqThzx3Oy0OwCbmDgE8gOznElRA0Garh5NW2Sp0PqNjjUoRmhyq6mU+Ul48LTWAHAZFqh/x9UCAnjw==hashcat output running -m 26620:
Session..........: 134659 Status...........: Cracked Hash.Mode........: 26620 (MetaMask Wallet (needs all data, checks AES-GCM tag)) Hash.Target......: $metamask$600000$xsq1OyKYinxYyiOUWyTVT820oedGQy+smC...Anjw== Time.Started.....: Tue Nov 25 13:47:25 2025 (2 secs) Time.Estimated...: Tue Nov 25 13:47:27 2025 (0 secs; Runtime limited: 59 mins, 58 secs) Kernel.Feature...: Pure Kernel Guess.Base.......: File (/home/cyclone/tmp/134659.wordlist.txt) Guess.Queue......: 1/1 (100.00%) Speed.#1.........: 1 H/s (1.24ms) @ Accel:8 Loops:512 Thr:512 Vec:1 Speed.#2.........: 0 H/s (0.00ms) @ Accel:8 Loops:512 Thr:512 Vec:1 Speed.#*.........: 1 H/s Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new) Progress.........: 1/1 (100.00%) Rejected.........: 0/1 (0.00%) Restore.Point....: 0/1 (0.00%) Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:599552-599999 Restore.Sub.#2...: Salt:0 Amplifier:0-0 Iteration:0-512 Candidate.Engine.: Host Generator + PCIe Candidates.#1....: catanddog -> catanddog Candidates.#2....: [Copying] Hardware.Mon.#1..: Temp: 44c Fan: 31% Util: 95% Core:2775MHz Mem:10251MHz Bus:1 Hardware.Mon.#2..: Temp: 44c Fan: 32% Util: 0% Core:2805MHz Mem:10251MHz Bus:1 Started: Tue Nov 25 13:47:21 2025 Stopped: Tue Nov 25 13:47:28 2025 -
If you're having issues getting hashcat working with the -m 26620 kernel, make sure you're following the directions on where to place the kernel / module files, then compile hashcat.
hashcat_26620_kernel
https://github.com/cyclone-github/hashcat_26620_kernelIf you're not able to get that working, you can download my hashcat v6.2.6 fork which comes pre-compiled with the -m 26620 kernel.
https://github.com/cyclone-github/hashcat/releases/tag/hashcat-6.2.6_cyclone-24-11-18 -
Keep in mind that hashcat v7.x recently added support for their own metamask wallet hash with dynamic iterations which is not compatible with the widely used 26620 kernel which I released back in March, 2024.
Now, to address your question:
Themetamask_extractorwill print two hashes:metamask_decryptorformat (can recover the password and seed phrase)
{"data": "","iv": "","keyMetadata": {"algorithm": "PBKDF2","params": {"iterations": }},"salt": ""}hashcat 26600 or 26620format (can be run with hashcat to recover only the password)
$metamask$600000$...$...$...If you're still needing more help, post your test wallet output from
metamask_extractorand we'll go from there (make sure to only post a test wallet with no balance and not a real wallet).@cyclone said in Cracking metamask hash:
Keep in mind that hashcat v7.x recently added support for their own metamask wallet hash with dynamic iterations which is not compatible with the widely used 26620 kernel which I released back in March, 2024.
I guess, it is compatible, but hash string should be changed from
$metamask$600000$...$...$...to
$metamask$rounds=600000$...$...$... -
@cyclone said in Cracking metamask hash:
Keep in mind that hashcat v7.x recently added support for their own metamask wallet hash with dynamic iterations which is not compatible with the widely used 26620 kernel which I released back in March, 2024.
I guess, it is compatible, but hash string should be changed from
$metamask$600000$...$...$...to
$metamask$rounds=600000$...$...$... -
Hello all members and @cyclone, Happy New Year. Greeting.
Regarding the metamask_decryptor, I have some ideas to upgrade it. I tried to use it to crack my old wallet.
At first, I used hashcat but 'Token Length Exception' error was occupied so I tried to use your decryptor.
But its speed is a bit slow and it's because yours use only CPU, not GPU. If you use CUDA, it would be better to speed up.
Also, we can add mask options like hashcat. Sorry for my suggestions but I really appreciate your tools.
Please let me know if you have some solutions for my sugesttions.
Thanks -
It is better to use hashcat to recover the wallet password, then use metamask_decryptor to recover the seed phrase. If you're having issues with getting hashcat to work, make sure to use metamask_extractor to properly extract the hash. Several users have run into issues getting hashcat and metamask hashes to work on Windows, so trying yours with hashcat on linux is worth a shot. I have hashcat with my custom 26620 metamask kernel hosted on github which is compatible with the metamask_extractor.
https://github.com/cyclone-github/hashcat -
Hi @cyclone, Long time no see. How are you today?
Regarding the Metamask Vault Decryptor, I can see 5430.89 h/s speed in the example screen. But when I test it on my side, I can see only about 82 h/s speed.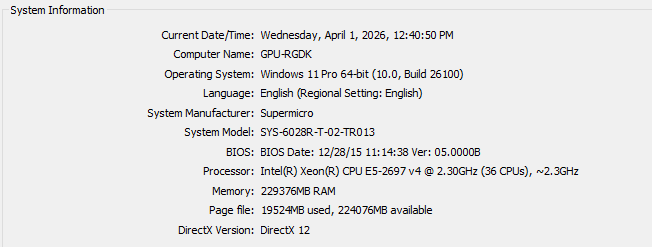
You can see my PC's spec in the uploaded screen. which device and OS did you use to test it on your side?
-
Hi @cyclone, Long time no see. How are you today?
Regarding the Metamask Vault Decryptor, I can see 5430.89 h/s speed in the example screen. But when I test it on my side, I can see only about 82 h/s speed.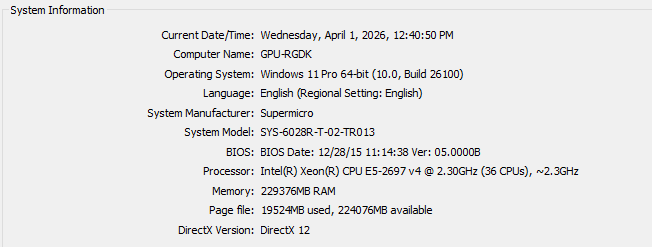
You can see my PC's spec in the uploaded screen. which device and OS did you use to test it on your side?
@Silver0666
I develop and test on Debian linux. Rig specs are listed here:
https://github.com/cyclone-github/hashgen-testing/tree/main/benchmarksThe speed difference you're seeing is likely due to the Metamask version of your wallet. The older 10k iteration pbkdf2 are much faster to run than the newer 600k iteration pbkdf2 vaults.
From the GitHub README:
https://github.com/cyclone-github/metamask_pwnExample vaults supported: * Old vault format: {"data": "","iv": "","salt": ""} * New vault format: {"data": "","iv": "","keyMetadata": {"algorithm": "PBKDF2","params": {"iterations": }},"salt": ""}For greater speed, you should use my hashcat_26620_kernel on the newer Metamask vaults.
https://github.com/cyclone-github/hashcat_26620_kernel -
Okay, make sense. it sounds like you used iteration=10000 version in your test. All right!
As you know, it would be faster if I use hashcat. But when I try to use it, I can see "Token length is overflow" error. It seems like my wallet's salt's length is too large. Do you have any insight to resolve this issue? -
Okay, make sense. it sounds like you used iteration=10000 version in your test. All right!
As you know, it would be faster if I use hashcat. But when I try to use it, I can see "Token length is overflow" error. It seems like my wallet's salt's length is too large. Do you have any insight to resolve this issue?@Silver0666
I've run into this before as well. You can either modify the hashcat kernel to allow longer tokens, or use hashcat'smetamask2hashcat.pyto generate a "short" -m 26610 hash.https://github.com/hashcat/hashcat/blob/master/tools/metamask2hashcat.py
-
Hi @cyclone, how is your weekend?
Could you help me to modify the limit of token in hashcat 26620 mode?
I'm using your hashcat 26620 mode to crack metamask vault. but when I try to crack it, I can see "Token length exception" error. so I'm going to modify it.
Could you help me with this?
Also, thanks for sharing hashcat 26620 module. -
Hi @cyclone, how is your weekend?
Could you help me to modify the limit of token in hashcat 26620 mode?
I'm using your hashcat 26620 mode to crack metamask vault. but when I try to crack it, I can see "Token length exception" error. so I'm going to modify it.
Could you help me with this?
Also, thanks for sharing hashcat 26620 module.@Silver0666
If you're not comfortable with modifying hashcat kernels, the best thing you can do is use the metamask2hashcat.py tool linked in my previous reply. Once you have the password recovered with hashcat using -m 26610, usemetamask_decryptorto recovery your seed phrase using the password recovered with hashcat.I'll also look into this issue to see if it's worth releasing an update to the 26620 kernel that can support longer tokens.
If you have any further questions, feel free to send me a DM on Matrix.
-
Okay, thanks for your support.
Hello! It looks like you're interested in this conversation, but you don't have an account yet.
Getting fed up of having to scroll through the same posts each visit? When you register for an account, you'll always come back to exactly where you were before, and choose to be notified of new replies (either via email, or push notification). You'll also be able to save bookmarks and upvote posts to show your appreciation to other community members.
With your input, this post could be even better 💗
Register Login

