Infosec News
-
Akira Ransomware Bypassing MFA on SonicWall VPNs
Akira ransomware operators are still hitting SonicWall SSL VPNs, even when OTP-based MFA is enabled.
Key points:
- Root cause linked to CVE-2024-40766, an access control flaw exploited in 2024.
- Attackers appear to have stolen both credentials and OTP seeds during earlier breaches.
- MFA bypass observed: multiple OTP prompts issued, then successful logins.
- Once inside, actors quickly scan networks, enumerate AD, and target Veeam servers for stored creds.
- BYOVD attacks used to kill endpoint protection via vulnerable drivers like rwdrv.sys.
- Even patched SonicOS 7.3.0 devices are being impacted.
Mitigation:
- Reset all VPN credentials, rotate MFA seeds, and monitor login patterns for anomalies. Backup servers should be treated as high-risk targets.
- MFA cannot protect against stolen seeds. If your SonicWall appliance ever ran vulnerable firmware, reset everything.
Sources:
-
Gen Z Failing at Identifying Phishing Attacks
A new global survey from Yubico reveals that Gen Z, those born between 1997–2012, is the most vulnerable group to phishing attacks, with 62% admitting to engaging with a phishing message in the past year, and are most likely to click on phishing links, attachments, or scams, with AI-powered social engineering attacks driving a new wave of deepfakes and voice-clone phishing.
The 2025 Global State of Authentication Survey, covering 18,000 participants across nine countries, found that:
- 44% of all respondents interacted with a phishing attempt in the past year.
- 70% believe AI has made phishing more effective, and 78% say attacks have grown more sophisticated.
- 54% of people shown a phishing email believed it was genuine or were unsure, highlighting the rising danger of AI-crafted scams.
- Only 48% of companies enforce MFA, and 40% of workers report no cybersecurity training at all.
Sources:
-
Scattered Lapsus$ Hunters Demand Neary $1 Billion in Ransom
A newly revived threat group calling itself Scattered Lapsus$ Hunters, a collaboration between members of Scattered Spider, Lapsus$, and ShinyHunters, has claimed responsibility for stealing over 1 billion Salesforce-related records and is demanding nearly $1 billion in ransom to prevent public release.
According to news reports, the attackers exploited Salesloft’s Drift integration, using stolen OAuth and refresh tokens to access Salesforce APIs and extract customer data, including contact information and case objects. Salesforce itself was not directly breached.
The group has launched a public extortion site listing roughly 40 affected organizations, including major names like Cloudflare, Palo Alto Networks, Zscaler, and Tenable. Victims are urged to “negotiate” to prevent leaks.
Salesforce maintains that its core platform remains secure, stating:
“There is no indication that the Salesforce platform has been compromised, nor is this activity related to any known vulnerability in our technology.”
Security researchers note that the campaign resembles previous Lapsus$ and Scattered Spider operations, focusing on third-party integrations to bypass enterprise protections. Google TAG and Mandiant are investigating the breach’s scope and potential secondary access vectors.
Sources:
-
Harvard Probes Data Breach Tied to Oracle Zero-Day Exploit
Harvard University is investigating a potential data breach after the Clop ransomware gang claimed to have stolen data by exploiting a zero-day flaw in Oracle’s E-Business Suite (CVE-2025-61882).
The university confirmed it was affected by the vulnerability, which has impacted multiple Oracle customers, but said the incident appears limited to a small administrative unit. Harvard stated it applied Oracle’s emergency patch and found no evidence of compromise in other systems.
The Clop group, known for high-profile zero-day exploits in platforms such as MOVEit Transfer and GoAnywhere MFT, recently began targeting Oracle users in a new extortion campaign. Harvard is the first organization publicly linked to the attacks, though more victims are expected to surface in the coming weeks.
Sources
- https://www.bleepingcomputer.com/news/security/harvard-investigating-breach-linked-to-oracle-zero-day-exploit/
- https://www.oracle.com/security-alerts/alert-cve-2025-61882.html
- https://www.crowdstrike.com/en-us/blog/crowdstrike-identifies-campaign-targeting-oracle-e-business-suite-zero-day-CVE-2025-61882/
-
Nation-State Hackers Breach F5 Networks
Summary
F5 Networks has confirmed a major security breach in which a nation-state-linked actor gained unauthorized access to internal systems and exfiltrated portions of BIG-IP source code and information on undisclosed vulnerabilities.
The intrusion is believed to have persisted for roughly 12 months before discovery.The company detected the incident on August 9, 2025, and delayed public disclosure at the request of the U.S. Department of Justice.
There is no indication that CRM, financial, support, or iHealth systems were accessed, although some customer configuration files were included in the stolen data.Technical and Attribution Details
- The attack is attributed to a Chinese cyber-espionage group tracked as UNC5221.
- The group deployed a custom backdoor named BRICKSTORM, previously used in intrusions against SaaS and BPO providers.
- The compromise targeted F5’s development environment, giving access to internal vulnerability data and code repositories.
- F5 brought in Mandiant and CrowdStrike for incident response, rotated all signing keys and credentials, and added additional security controls.
Government Response
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued Emergency Directive 26-01, requiring all federal agencies to:- Inventory all F5 BIG-IP, F5OS, BIG-IQ, and APM systems.
- Verify that management interfaces are not exposed to the internet.
- Apply vendor patches no later than October 22, 2025.
- Submit compliance reports to CISA by October 29, 2025.
CISA stated that the stolen source code and vulnerability information provide adversaries with a technical advantage for developing zero-day exploits.
CVEs and Patch References
Key vulnerabilities disclosed following the breach include:- CVE-2025-53868 – BIG-IP SCP/SFTP privilege escalation (CVSS 8.7)
- CVE-2025-61955 – F5OS command injection, appliance mode (CVSS 8.8)
- CVE-2025-57780 – F5OS arbitrary code execution, appliance mode (CVSS 8.8)
Administrators should immediately apply the latest firmware and software updates for BIG-IP, F5OS, BIG-IQ, APM, and BIG-IP Next (Kubernetes).
Recommended Actions:
- Patch all F5 systems immediately.
- Remove or restrict public access to management interfaces.
- Audit and retire end-of-life or unsupported devices.
- Monitor for anomalous configuration changes or new admin accounts.
- Treat F5 perimeter devices as high-risk until verified patched and hardened.
Sources:
- https://thehackernews.com/2025/10/f5-breach-exposes-big-ip-source-code.html
- https://www.reuters.com/technology/breach-us-based-cybersecurity-provider-f5-blamed-china-bloomberg-news-reports-2025-10-16/
- https://www.techradar.com/pro/security/significant-threat-to-us-networks-after-hackers-stole-f5-source-code-cisa-warns
-
Major Amazon Web Services (AWS) Outage
AWS is currently experiencing a major outage in the US-EAST-1 region, impacting dozens of core services and many third-party platforms.
Status: Degraded performance and elevated error rates across multiple services.
Root Cause (according to AWS): Internal subsystem failure tied to the monitoring of network load balancers and EC2 internal networking.Origin & propagation: Issues began around 3:11 a.m. ET in US-EAST-1, and have cascaded globally for services dependent on that region.
Affected AWS Services (partial list):
Core compute/storage/database services including EC2, S3, RDS, Lambda, CloudWatch, CloudFront, DynamoDB, SQS, SNS, ECS, EKS, Glue, Redshift, SageMaker, Cognito, Connect, VPC services, Step Functions, Secrets Manager, and more.
AWS lists around 90 services impacted.Third-Party Services / Platforms Impacted:
Major consumer/enterprise platforms reported disruptions: games like Fortnite, Roblox; apps like Snapchat, Venmo; smart home devices (Ring, Alexa); banks and financial apps; many SaaS services relying on AWS infrastructure.What this means for you:
- If you rely on AWS in US-EAST-1, expect slower API responses, partial failures, or launch errors (especially for new EC2 instances).
- If you rely on third-party services (SaaS, gaming, streaming, banking), you may see outages despite those services not being your direct provider.
Sources:
- AWS Status Page: https://health.aws.amazon.com/health/status
- Downdetector Report: https://downdetector.com/status/aws-amazon-web-services/
- Tom's Guide: https://www.tomsguide.com/news/live/amazon-outage-october-2025
- Reuters: https://www.reuters.com/business/retail-consumer/amazons-cloud-unit-reports-outage-several-websites-down-2025-10-20/
-
Xubuntu.org Compromised - Torrent Downloads Served Windows Malware
Over the weekend (October 18–19, 2025), the official Xubuntu website (xubuntu.org) was compromised. Attackers managed to inject a malicious download link into the torrent section of the downloads page. A similar attack also happened in September 2025 where attackers injected malicious javascript into non-English language pages of the site.
What Happened
The legitimate .torrent link was replaced with a ZIP archive:
xubuntu-safe-download.zipWhich contained files:
TestCompany.SafeDownloader.exe terms-of-service.txtThe EXE impersonated a “Xubuntu - Safe Downloader” GUI installer.
On execution, it installed itself to:%AppData%\Roamingand added a Windows registry key for persistence at startup.
Malware Behavior
The EXE was identified as a Crypto Clipper Trojan, flagged by 26/72 vendors on VirusTotal.
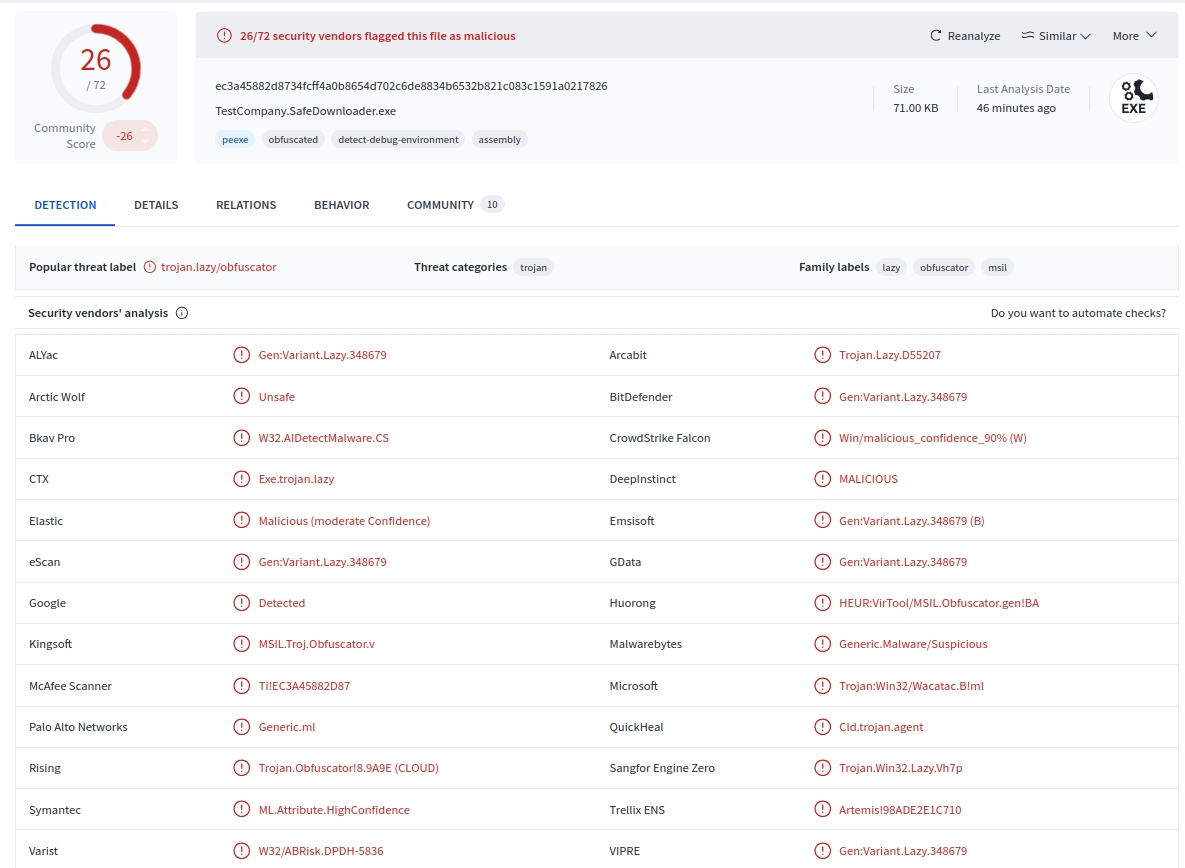
Behavior:
- Monitors the clipboard for cryptocurrency wallet addresses (BTC, ETH, LTC, etc.).
- Replaces copied wallet addresses with attacker-controlled ones.
- Windows-only payload. It targets Windows users downloading from Xubuntu.org.
- No confirmed reports of cryptocurrency theft at the time of this writing.
Technical Context
The malicious file was hosted within a WordPress uploads path "
/wp-content/uploads/", suggesting the compromise occurred via a vulnerable plugin or outdated component.A similar minor incident in September 2025 served malvertising on the same domain, implying the attackers retained access.
The Xubuntu team has disabled the affected download page and announced a migration to a static-site architecture to prevent further injection or file tampering.
What Was Not Affected
Direct ISO images and checksums hosted on Canonical’s official mirror (cdimage.ubuntu.com) were not compromised.
Only the torrent download link from the Xubuntu.org domain was affected.
Recommendations
If you downloaded Xubuntu via torrent from Xubuntu.org between October 18–19, 2025:
- Delete xubuntu-safe-download.zip immediately.
- Scan your Windows system for malware or autorun persistence keys.
- Rotate cryptocurrency wallets and reset all associated credentials.
- Verify all future downloads against SHA256/PGP checksums provided on Canonical mirrors.
Sources:
-
Recap of Record Setting Hyper-Volumetric DDoS Attacks in 2025 (CloudFlare)
Overview:
Recent months have seen a dramatic escalation in Distributed Denial-of-Service (DDoS) attacks, both in volume and packet rate. Two ultra-high-volume events stand out: a 7.3 Tbps / 4.8 Bpps attack on May 15 2025, and a later and eye watering 11.5 Tbps / 5.1 Bpps assault on September 3 2025, both successfully mitigated by Cloudflare.Key Details:
- The 7.3 Tbps attack targeted an unnamed hosting provider in mid-2025 and delivered roughly 37.4 TB of data in ~45 seconds.
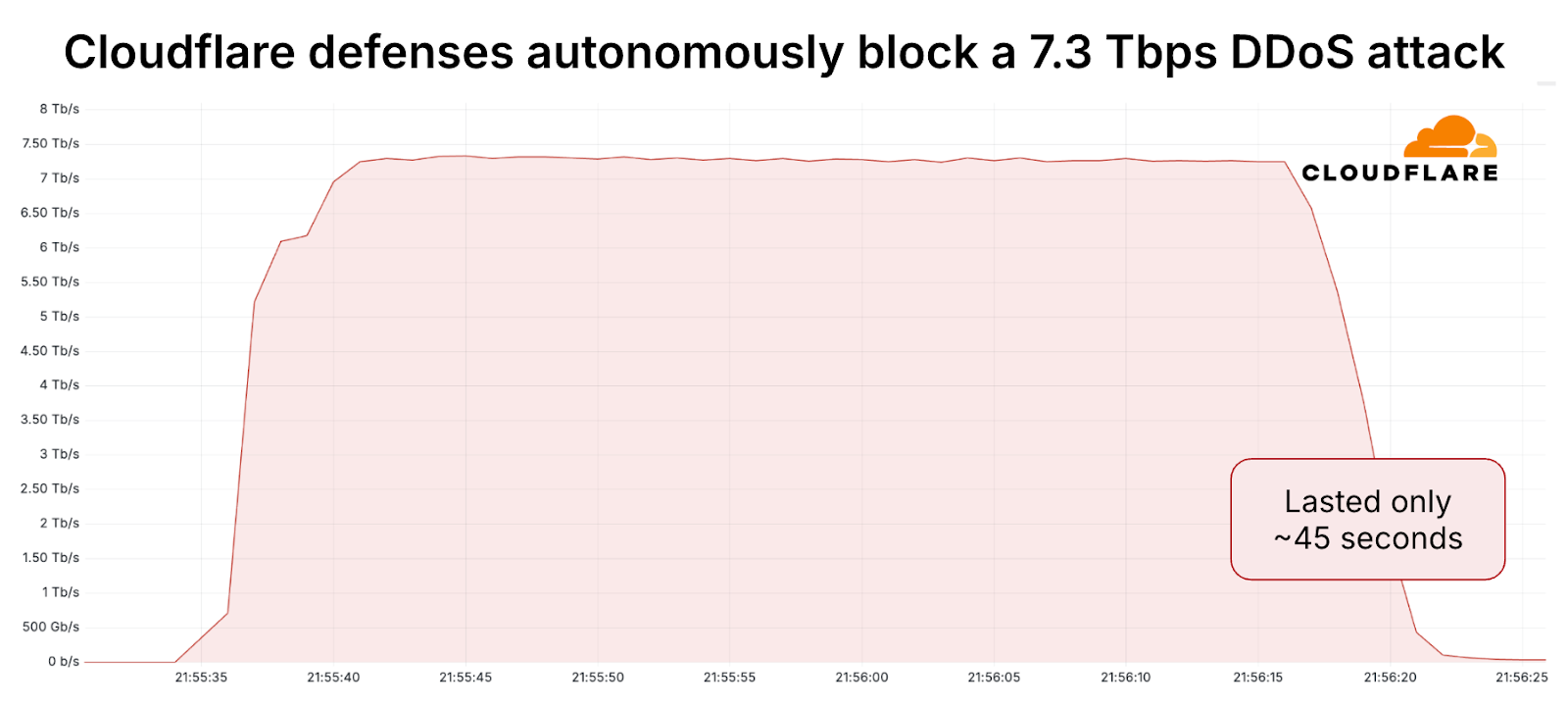
- The 11.5 Tbps event occurred in September 2025, lasted about 35 seconds, and was primarily a UDP flood. Sources included cloud providers and massive IoT botnets.
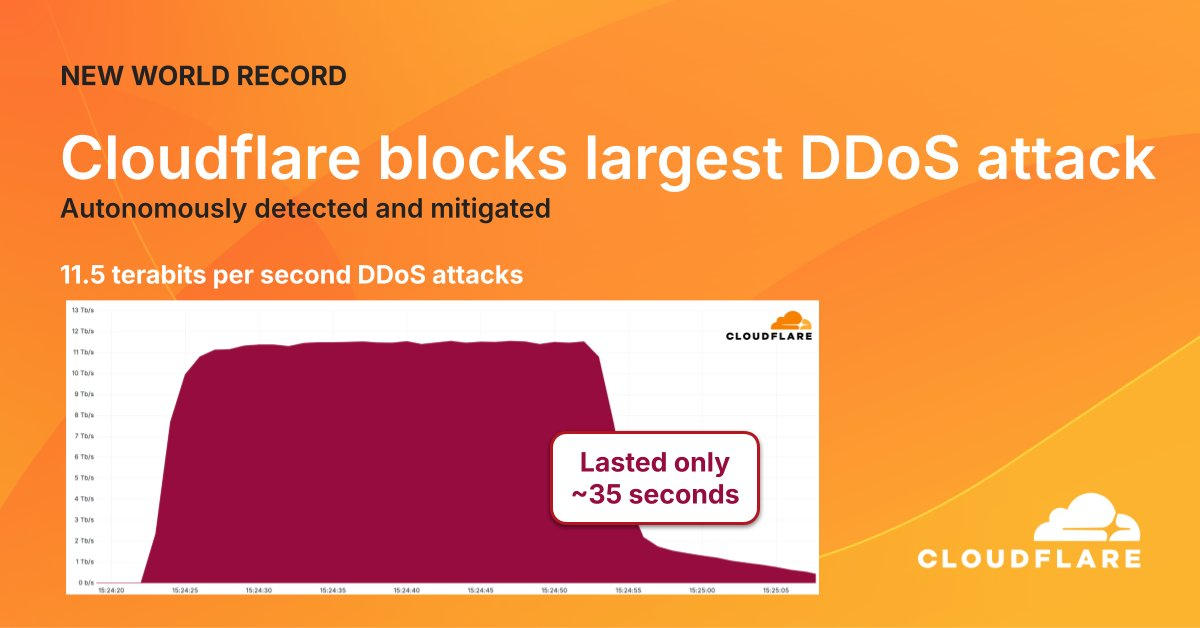
- These attacks reflect a trend: “hyper-volumetric” DDoS defined as >1 Tbps or >1 Bpps are now occurring at disproportionately high rates.
Final Thoughts:
- The sheer rate and short duration (under a minute) make detection and response challenging.
- Attackers are increasingly deploying multi-vector strategies and exploiting large botnets of compromised IoT/cloud devices.
- These record-breaking DDoS events signal that we’ve entered a new era of scale in DDoS attacks. The days of only mitigating sub-100 Gbps events are behind us - now it’s multi-Tbps and packet rates in the billions.
Sources:
-
Qilin Ransomware Using WSL to Deploy Encryptors on Windows
The Qilin ransomware group (formerly “Agenda”) has started abusing Windows Subsystem for Linux (WSL) to execute Linux ELF encryptors directly inside Windows environments, a move designed to evade EDR and antivirus detection.
Behavior:
- Threat actors gain access to a Windows host, then install or enable WSL via command-line tools or scripts.
- They transfer a Linux encryptor (ELF binary) using WinSCP and launch it through remote management tools like Splashtop (SRManager.exe).
- Since most Windows EDRs focus on PE-based behaviors, activity inside the WSL environment goes largely undetected.
Tactics:
- BYOVD attacks using vulnerable drivers (e.g. eskle.sys, rwdrv.sys, hlpdrv.sys) to disable security tools.
- Use of AnyDesk, ScreenConnect, Splashtop for persistence and remote access.
- DLL sideloading, dark-kill, and HRSword to remove traces or disable defenses.
- Manual inspection of files using Paint and Notepad before exfiltration.
Scale:
- Over 700 confirmed victims across 62 countries in 2025.
- Roughly 40 new victims/month during the second half of the year.
- Focus on hybrid Windows–Linux infrastructures, including VMware ESXi environments.
Sources:
- https://blog.talosintelligence.com/uncovering-qilin-attack-methods-exposed-through-multiple-cases/
- https://www.bleepingcomputer.com/news/security/qilin-ransomware-abuses-wsl-to-run-linux-encryptors-in-windows/
- https://www.trendmicro.com/en_us/research/25/j/agenda-ransomware-deploys-linux-variant-on-windows-systems.html
-
Rust CVE-2025-62518 - Critical RCE Vulnerability "TARmageddon" in Rust tar Libraries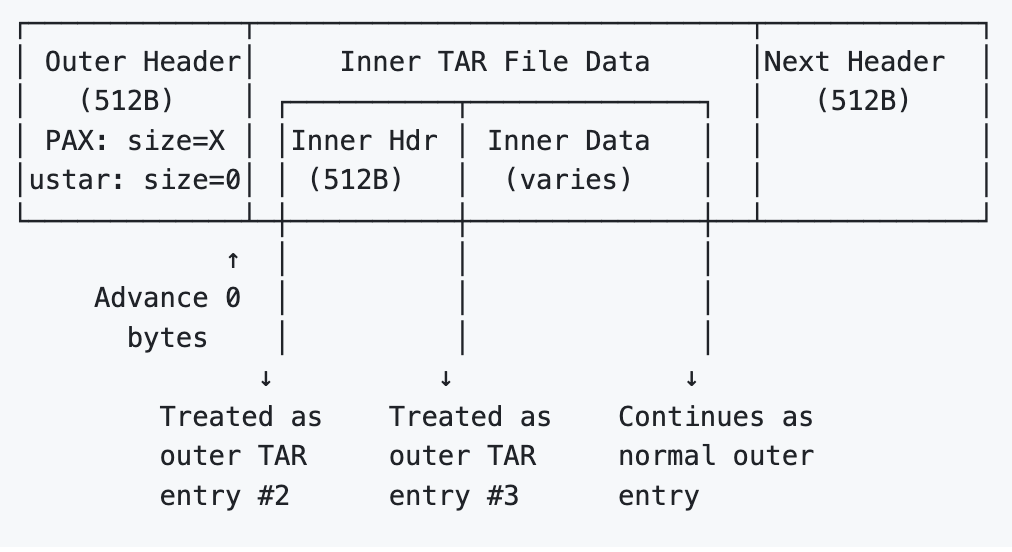
A new high-severity vulnerability (CVE-2025-62518, “TARmageddon”) has been disclosed in several Rust async tar libraries: async-tar, tokio-tar, and their forks.
The flaw is a boundary-parsing desynchronization in TAR header handling.
When archives contain PAX-extended headers that override the file size, the vulnerable parser incorrectly trusts the ustar size (often zero) to advance the read position. This misaligns the stream, letting hidden nested TAR data be treated as legitimate entries.This enables archive smuggling where attackers can insert extra files that overwrite configs or inject malicious build files. This can lead to remote code execution or supply-chain compromise when untrusted TARs are processed.
Note: this is not a memory safety vulnerability in Rust (which is inherintly memory safe), but a logic vulnerability in the code.
Impacted Ecosystem
- Directly vulnerable crates: async-tar, tokio-tar, krata-tokio-tar, astral-tokio-tar (<0.5.6)
Affected downstreams include:
- uv (Astral’s Python package manager)
- testcontainers
- wasmCloud, binstalk-downloader, and others
Attack Scenarios
- Python package RCE - malicious PyPI tarballs overwrite pyproject.toml.
- Container poisoning - crafted layers inject or overwrite files during unpack.
- BOM bypass - scanners approve the clean outer archive; hidden inner files slip through during extraction.
Sources:


